
Meta has introduced new security and transparency enhancements to its end-to-end encrypted backup system for WhatsApp and Messenger, strengthening how encryption keys are distributed and verified while opening parts of its infrastructure to independent auditing.
The updates build on the company’s HSM-based (Hardware Security Module) Backup Key Vault architecture. This system underpins encrypted backups by storing recovery secrets inside tamper-resistant hardware, ensuring that neither Meta nor cloud providers like Apple or Google can access users’ message archives. The improvements focus on two areas: enabling over-the-air (OTA) key distribution for Messenger and publishing verifiable evidence of secure infrastructure deployments.
WhatsApp and Messenger collectively serve billions of users worldwide. While end-to-end encryption has protected messages in transit since 2016, backups stored in cloud services have historically posed a weaker link. Meta’s HSM-based approach aims to close that gap by ensuring that only users can decrypt stored data.
Meta’s whitepaper explains that when users enable encrypted backups, their device generates a 256-bit encryption key locally, which is used to encrypt all backup data, including messages, photos, and videos, before it is uploaded to cloud storage. Crucially, this key never leaves the device in plaintext, and even the user’s password protecting it is not visible to Meta or third parties.
To safeguard recovery, an encrypted version of the backup key is stored in the HSM-based vault using the OPAQUE password-authenticated key exchange protocol. This design allows the system to verify a user’s password without ever learning it, reducing the risk of credential exposure. The vault also enforces strict rate-limiting on password attempts and can permanently lock access after repeated failures, mitigating brute-force attacks.
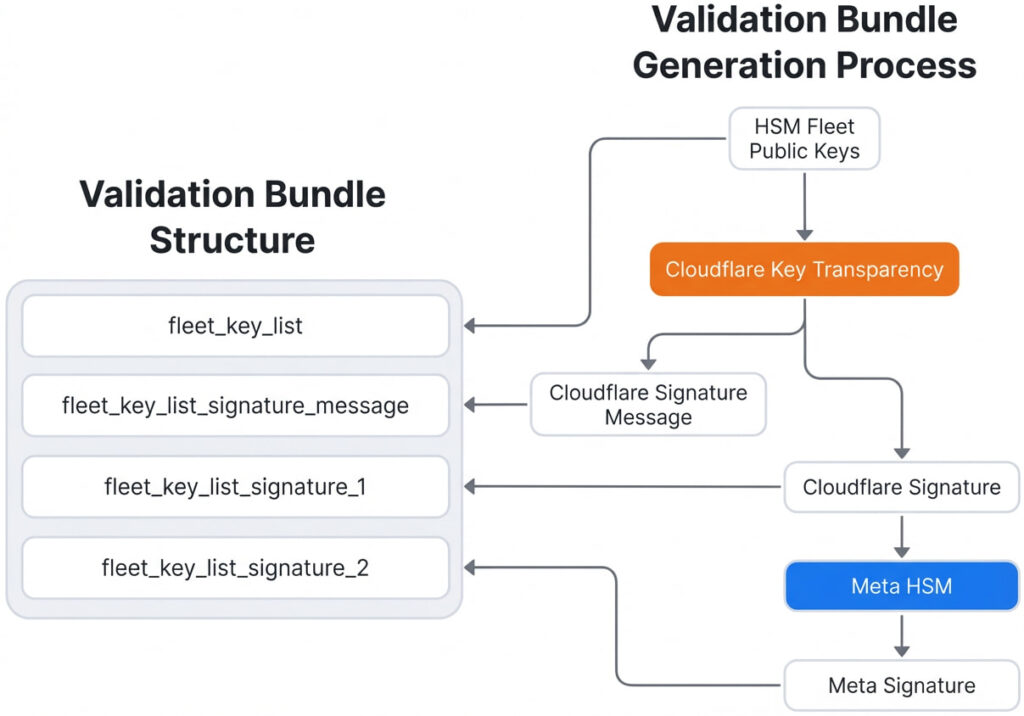
One of the most notable additions is the OTA fleet key distribution mechanism, which replaces the need to hardcode trusted infrastructure keys into Messenger apps. Instead, clients now receive a “validation bundle” containing the HSM fleet’s public keys at runtime. These bundles are signed by Cloudflare and counter-signed by Meta, with entries logged in Cloudflare’s Key Transparency system. Clients verify signatures, check timestamps for freshness, and ensure that the responding server’s key matches the approved list before proceeding.
Meta
The vault operates as a distributed fleet across at least seven datacenters, using majority-consensus replication to remain functional even during partial outages. This design ensures both availability and integrity, preventing a single point of failure.
Meta is also increasing transparency by committing to publishing cryptographic proof of each new HSM fleet deployment. Advanced users and researchers can verify these deployments using Meta’s open-source “mbt” (Meta Binary Transparency) CLI tool, which performs multiple checks, including signature validation, SHA-256 digest verification, and cross-referencing with Cloudflare’s independent audit logs, to confirm that fleet keys have not been tampered with.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


