
McAfee researchers have uncovered an Android rootkit campaign dubbed “Operation NoVoice” that used seemingly benign Google Play apps to gain full control of devices, inject code into every app, and steal sensitive data, including WhatsApp account sessions.
According to a McAfee report, the campaign exploited known Android vulnerabilities patched between 2016 and 2021, primarily targeting older or unpatched devices. While devices running Android security patch level 2021-05-01 or later are not vulnerable to the specific exploits analyzed, users who installed the malicious apps may still have been exposed to additional, undiscovered payloads.
Malicious apps hidden in plain sight
The attack chain began with more than 50 apps distributed through Google Play, collectively amassing at least 2.3 million downloads. These apps posed as harmless utilities such as cleaners, casual games, and gallery tools, and functioned as advertised, raising no immediate suspicion.
McAfee
In the background, however, the apps silently connected to command-and-control (C2) servers, profiling infected devices and delivering tailored exploit packages. Notably, the apps requested no unusual permissions and embedded their malicious logic within legitimate SDK components, including modified versions of Facebook SDK classes to evade detection.
McAfee reported its findings to Google via responsible disclosure. Google subsequently removed the apps and banned the associated developer accounts.
Multi-stage attack chain
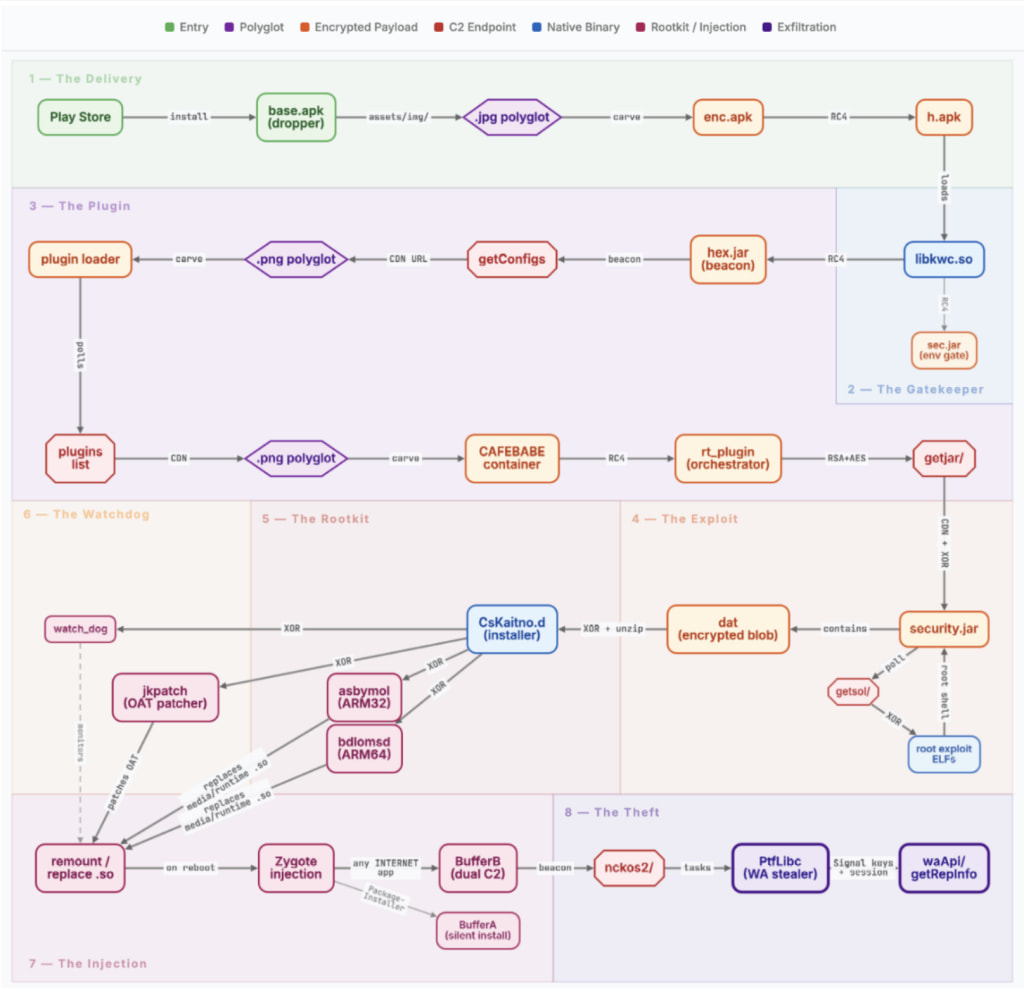
Operation NoVoice consists of multiple stages delivered dynamically from attacker-controlled infrastructure. The initial payload is concealed within a polyglot image file, appearing as a normal PNG while secretly carrying encrypted malware appended after the file’s end marker.
Once executed, the malware deploys a layered framework that:
- Evades analysis using 15 environmental checks (including emulator, VPN, and geofencing detection)
- Establishes persistent communication with C2 servers
- Downloads plugins disguised as image assets
- Selects and executes root exploits tailored to the device
McAfee identified 22 distinct exploits used in the campaign, including advanced kernel-level attacks targeting vulnerabilities in IPv6 handling and Mali GPU drivers. Successful exploitation grants attackers root access and disables Android’s SELinux protections.
After gaining root privileges, the malware installs a rootkit identified as CsKaitno.d, which modifies core system components to ensure persistence and control.
The rootkit replaces critical system libraries such as libandroid_runtime.so and libmedia_jni.so with malicious wrappers that intercept system calls. This allows attacker-controlled code to execute whenever any app launches. Additionally, it patches Android framework bytecode on disk, creating a secondary persistence layer that survives attempts to restore original libraries.
McAfee
A watchdog component continuously monitors the infection and reinstalls missing components, even forcing device reboots if tampering is detected. On affected devices, particularly those running Android 7 or older, a factory reset does not remove the infection. Full firmware reflashing is required.
WhatsApp session hijacking and data theft
The only payload recovered during analysis, named PtfLibc, specifically targets WhatsApp. It extracts encrypted databases, Signal protocol keys, registration identifiers, and user metadata, including phone numbers and account details.

McAfee
This data is exfiltrated via the attacker’s infrastructure, enabling the cloning of a victim’s WhatsApp session on another device. Because the malware operates within every app process, it can potentially target other applications as well, though no additional payloads were observed.
McAfee noted strong similarities between NoVoice and the notorious Triada malware family. Both use the same persistence mechanism and the same system property to track infections. This suggests either a direct evolution of Triada or shared tooling between threat actors.
The best defense is to upgrade to Android patch level 2021-05-01 or later, and avoid installing apps from unknown or low-reputation developers, even on Google Play.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


