A researcher has disclosed a privacy weakness in Mullvad VPN that could allow users to be probabilistically identified across different VPN servers by correlating the exit IP addresses assigned to their WireGuard connections.
The issue stems from how Mullvad deterministically assigns exit IPs based on a user’s WireGuard key, resulting in recognizable patterns that may persist across servers.
The researcher using the online handle “tmctmt” described the behavior as a potential fingerprinting vector that could undermine some of the anonymity users expect from a privacy-focused VPN provider. Mullvad has acknowledged the report and says it is already testing mitigations for part of the behavior.
Mullvad is a Sweden-based VPN provider widely regarded in the privacy community for its no-logs policy, anonymous account system, and support for privacy-preserving payment methods. Unlike many competing VPN services that route large numbers of users through a smaller set of shared exit IP addresses, Mullvad distributes users across multiple exit IPs per server to reduce congestion, rate-limiting problems, and abuse-triggered IP blocks.
According to the researcher, the problem is not that users receive stable IP addresses on a single server, but that the assignment appears to follow a deterministic pattern across all servers. In practice, this means a user connecting to several Mullvad servers may receive a unique or semi-unique “constellation” of exit IPs that can be correlated.
To investigate the behavior, tmctmt wrote a script that repeatedly rotated WireGuard public keys and collected assigned exit IPs from nine Mullvad servers located across several countries, including Australia, Germany, Finland, Chile, South Africa, and the United States. After generating data from 3,650 different public keys overnight, the researcher mapped the available IP pools and analyzed the assignment patterns.
Despite the mathematically enormous number of possible IP combinations, estimated at more than 8.2 trillion across the tested servers, the experiment produced only 284 distinct combinations. Further analysis showed that assigned IPs consistently landed within approximately the same percentile range of each server’s IP pool.
For example, a user assigned an exit IP near the 81st percentile of one server’s pool would typically receive exit IPs near the same percentile on other servers as well. The researcher concluded that Mullvad likely uses a seed-based random number generation mechanism tied to the WireGuard public key or tunnel identifier when selecting exit IP addresses.
The write-up speculates that Mullvad’s backend may rely on deterministic pseudo-random number generation behavior similar to Rust’s random_range implementation, where the same seed and varying bounds still produce outputs clustered around equivalent proportional positions within each pool. Mullvad’s desktop and mobile clients are largely written in Rust.
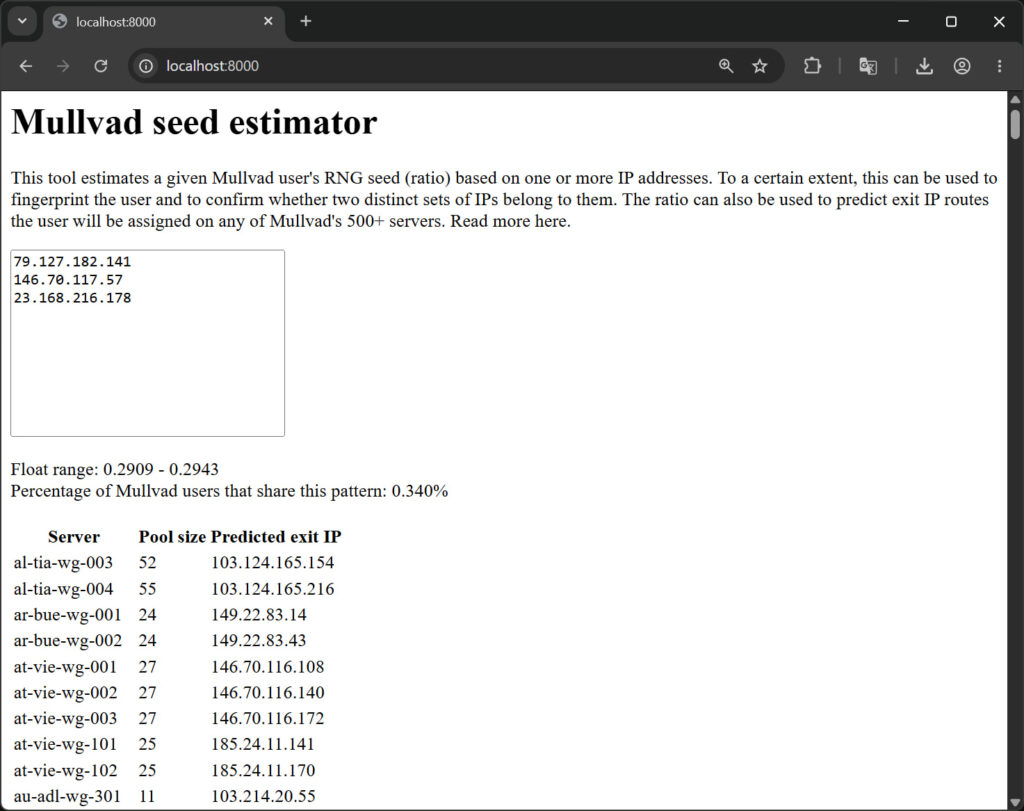
To demonstrate the privacy implications, tmctmt released a proof-of-concept “seed estimator” tool that calculates the possible range associated with a set of observed Mullvad exit IPs. In one example provided by the researcher, a combination of IPs narrowed the user population down to roughly 0.34% of active Mullvad users.
tmctmt
Assuming approximately 100,000 active users, that would leave around 340 users sharing the same inferred fingerprint. While not uniquely identifying an individual, the researcher argued that the data could still enable high-confidence correlation attacks when combined with IP logs, account activity, moderation records, breached datasets, or legal requests.
Mullvad’s (un)official response
Shortly after the report gained attention on Hacker News, Mullvad co-founder and co-CEO Fredrik Strömberg, posting under the username “kfreds,” responded publicly to the findings.
“Some aspects of the described behavior are as we intended and some are not,” Strömberg wrote.
He added that Mullvad had already begun testing a patch to address the unintended behavior in its infrastructure, warning that users attempting to reproduce the findings might see inconsistent results while mitigations are rolled out.
Strömberg also noted that the company would reevaluate whether some of the intended design decisions remain acceptable in light of the newly identified privacy implications, describing the issue as a trade-off between usability and anonymity.
The executive also encouraged security researchers to privately notify vendors before publicly disclosing privacy or security flaws.
CyberInsider also contacted Mullvad to request a statement on the topic, and we will update this post when we hear back from the VPN vendor.
For users concerned about correlation attacks, the researcher recommends avoiding frequent server switching while using the same WireGuard key and periodically forcing key rotation by logging out and back into the Mullvad application. Mullvad normally rotates WireGuard keys every 1 to 30 days, although users relying on third-party clients may retain static keys indefinitely.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.