Vercel has disclosed a security incident involving unauthorized access to parts of its internal systems, as a threat actor simultaneously claims to be selling access keys, source code, and database information allegedly linked to the company.
The incident was confirmed on April 19, 2026, via a security bulletin published by Vercel’s security team, which states that the company detected unauthorized access and has since engaged external incident response experts to investigate and contain the breach. Law enforcement has also been notified, and the company says it is continuing its forensic analysis while maintaining service availability.
According to Vercel, the impact appears to be limited to “a subset of customers” who are being contacted directly. The company has not yet disclosed the nature of the compromised systems or whether sensitive customer data, source code, or credentials were exfiltrated. However, it emphasized that its platform remains operational and that updates will follow as the investigation progresses.
The disclosure coincides with a post on a cybercrime forum by a threat actor using the “ShinyHunters” moniker, who claims to be selling access to Vercel’s infrastructure. The listing advertises “access keys, source code, and database” data, along with API keys and tokens allegedly tied to internal deployments and developer environments. The threat actor further suggests that the data could enable a large-scale supply-chain attack targeting applications built on Vercel’s platform.
The forum post references technologies closely associated with Vercel’s ecosystem, such as Next.js and Turborepo, and claims potential reach across millions of developers via compromised deployment pipelines.
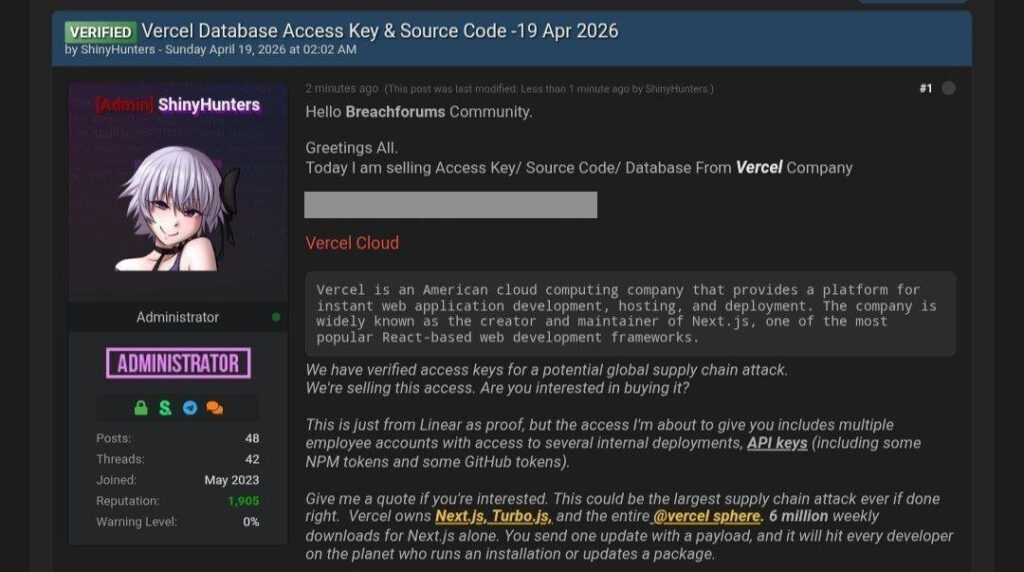
Notably, Vercel is not currently listed on the known ShinyHunters extortion portal. We reached out to ShinyHunters, and they denied involvement in the Vercel incident. This suggests the possibility of a copycat actor or loosely affiliated individuals reusing the name.
Vercel is a US-based cloud platform provider best known for its frontend hosting and deployment services, widely used by developers building modern web applications. The company is the primary steward of Next.js, one of the most popular React frameworks, and its infrastructure plays a critical role in the deployment pipelines of startups, enterprises, and open-source projects alike.
In its advisory, Vercel urged customers to take precautionary measures while the investigation is ongoing. These include reviewing account and environment activity logs for suspicious behavior, rotating environment variables and API keys, and leveraging built-in features for managing sensitive variables. The company is also offering direct support to customers needing assistance with credential rotation or incident response steps.
Given the potential implications of exposed API keys or deployment tokens, organizations using Vercel should prioritize credential hygiene and monitor for unauthorized changes to builds, deployments, or project configurations.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.