
Citizen Lab has identified two advanced surveillance campaigns abusing weaknesses in global telecom networks to track mobile users and, in some cases, turn SIM cards into silent spying tools.
The investigation began in late 2024 after anomalous activity was detected in signaling firewall logs, with additional data provided by telecom security firm Cellusys. By analyzing signaling traffic, routing data, and telecom infrastructure records with partners like Telenor Linx and P1 Security, researchers linked real-world attack activity to global operator networks for the first time.
The report focuses on two threat clusters, dubbed STA1 and STA2, both believed to be tied to commercial surveillance vendors offering services to government clients.
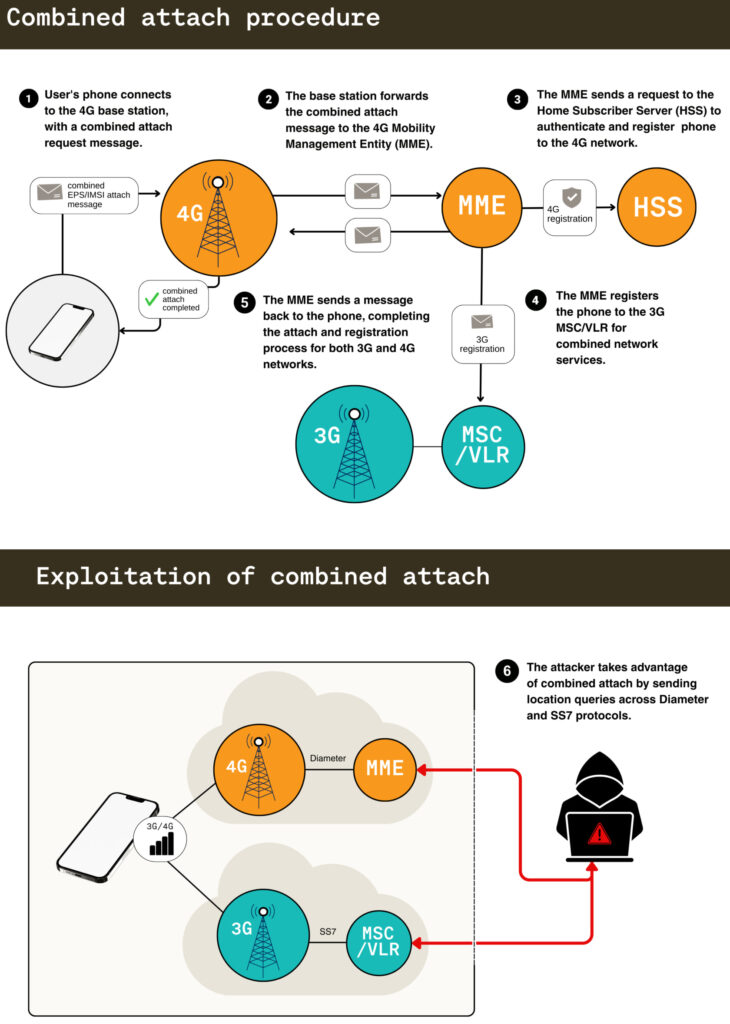
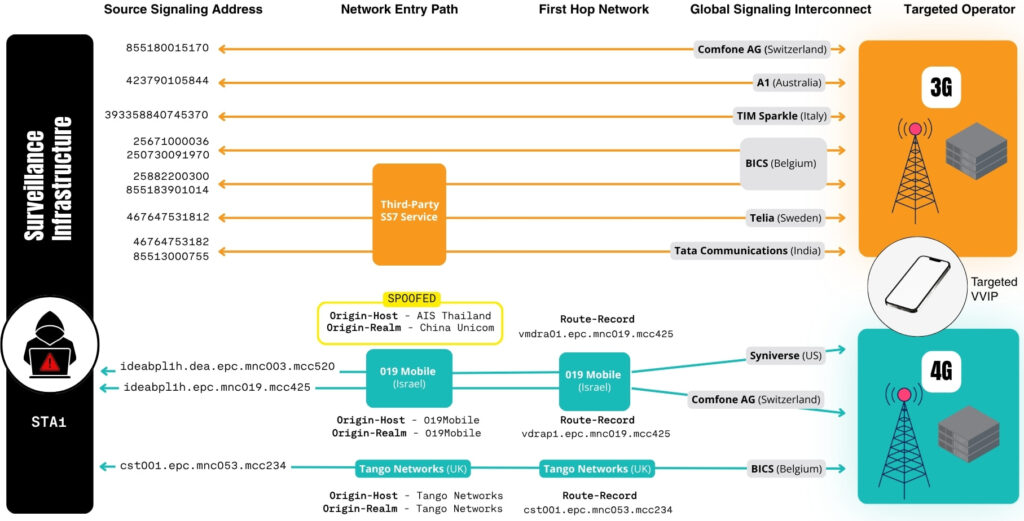
STA1 is a long-running, highly coordinated operation that uses both SS7 (3G) and Diameter (4G) signaling protocols to perform location tracking. In one November 2024 case, the actor targeted a high-profile executive, cycling through multiple operator identities across various countries, including Cambodia, Sweden, Italy, and Uganda. The attacker repeatedly switched between protocols and techniques to bypass telecom firewalls and extract location data.
The campaign also manipulated signaling identifiers and routing paths to hide its origin. Infrastructure tied to operators such as 019Mobile (Israel), Tango Networks UK, and Airtel Jersey appeared as entry or transit points. Citizen Lab notes these networks were likely abused via third-party access or spoofing rather than direct involvement. Historical telemetry shows similar activity dating back to at least 2022, with hundreds of tracking attempts linked to the same infrastructure.
STA2 uses a different approach, combining signaling attacks with device-level exploitation. In early 2025, researchers observed a binary SMS carrying hidden SIM Toolkit (STK) commands designed to exploit the S@T browser, a legacy SIM feature. This “SIMjacker”-style attack allows attackers to silently retrieve location data without user interaction.
The malicious SMS uses specific headers so it is processed directly by the SIM card and never shown to the user. Once executed, it collects cell tower data and sends it back via a hidden SMS to attacker-controlled systems. The attack chain also included SS7 probing and Diameter queries, indicating coordinated multi-layer surveillance.
Citizen Lab linked STA2 to a large-scale campaign involving over 15,000 location tracking attempts since 2022. The activity overlaps with infrastructure and patterns previously associated with Swiss-based Fink Telecom Services (FTS), a firm tied to telecom surveillance operations in earlier investigations.
These attacks do not rely on malware or device compromise, but instead exploit structural weaknesses in telecom protocols. SS7 lacks authentication entirely, while Diameter security features are often not enforced in practice. This allows attackers to impersonate trusted operators, route malicious queries through legitimate interconnect providers, and blend surveillance traffic into normal roaming activity.
Citizen Lab warns that the global telecom ecosystem remains vulnerable due to its reliance on trust-based interconnections and weak oversight of third-party access. Without stronger validation controls, improved firewall protections, and stricter regulations, these networks will continue to enable covert surveillance at a global scale.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


