editorially independent. We may make money when you click on links
to our partners.
Learn More
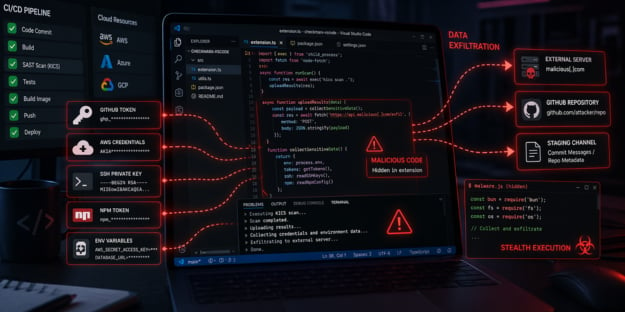
A supply chain attack targeting Checkmarx tooling has exposed developer environments.
Attackers pushed malicious Docker images and tampered extensions capable of stealing credentials and other sensitive data.
This “… continues a dangerous trend that’s accelerated over the past month: CI/CD pipelines have become the new perimeter,” said Eli Woodward, Cyber Threat Intelligence Advisor at Team Cymru in an email to eSecurityPlanet.
He added, “Instead of flashy zero-days or sophisticated phishing campaigns, TeamPCP is methodically abusing trusted resources across our technology ecosystems.”
Inside the Checkmarx Supply Chain Attack
The compromise centers on Keeping Infrastructure as Code Secure (KICS), a widely used tool designed to scan Terraform, Kubernetes, and other cloud configuration files for security risks.
Socket researchers discovered that attackers poisoned official images in the checkmarx/kics Docker Hub repository, modifying the bundled KICS binary to include hidden data collection capabilities.
As a result, scan outputs — often containing sensitive configuration details, credentials, or secrets — could be silently harvested and transmitted to attacker-controlled infrastructure.
The risk is amplified because KICS is commonly embedded in CI/CD pipelines, meaning organizations may have unknowingly exposed sensitive infrastructure data during routine automated scans.
Several commonly used tags, including v2.1.20, alpine, debian, and latest, were temporarily redirected to malicious images before being restored.
A rogue v2.1.21 tag was also introduced despite not corresponding to any legitimate upstream release.
Malicious VS Code Extensions and Payload Delivery
As the investigation progressed, it became clear the incident extended beyond just compromised container images.
Researchers identified suspicious behavior in Checkmarx-related VS Code extensions, pointing to a broader, coordinated supply chain attack across multiple distribution channels.
Deeper analysis revealed that certain extension versions (notably 1.17.0 and 1.19.0) contained hidden functionality that downloaded and executed a second-stage payload, mcpAddon.js, using the Bun runtime.
The payload was fetched from a hardcoded GitHub URL tied to a backdated, manipulated commit in Checkmarx’s repository, allowing attackers to leverage a trusted source to evade detection.
Credential Theft and Attack Propagation
The mcpAddon.js payload functions as a comprehensive credential harvester, targeting sensitive data such as GitHub tokens, cloud credentials, npm configs, SSH keys, and environment variables.
Once collected, the data is compressed, encrypted, and exfiltrated to external infrastructure and attacker-controlled public GitHub repositories, sometimes within victim accounts.
In some cases, repository metadata and commit messages were also used as covert staging channels.
This campaign represents a sophisticated, multi-stage software supply chain compromise.
It combines techniques such as Docker image poisoning via tag overwrites, Git history manipulation with backdated commits, RCE through developer extensions, and CI/CD pipeline abuse.
Using stolen GitHub credentials, the malware propagates by identifying repositories with secrets, creating new branches, and injecting malicious workflows to extract those secrets as artifacts.
These workflows execute automatically upon commit and are later removed to reduce forensic visibility, enabling the attack to scale across repositories, organizations, and pipelines.
Attribution and Broader Impact
Researchers have confirmed a working attack chain, though parts of the operation remain under active investigation.
A threat actor group known as TeamPCP is claiming responsibility for the incident.
This campaign also appears to extend beyond just Checkmarx tooling.
Separate findings show the Bitwarden CLI was also compromised via a similar GitHub Actions vector, indicating a broader supply chain attack targeting developer tools and CI/CD pipelines.
Socket’s research team is continuing to investigate the Bitwarden incident as well.
How to Reduce Supply Chain Risk
Organizations should treat this incident as a supply chain and credential exposure issue rather than a standalone tooling problem.
While immediate containment is important, longer-term risk reduction depends on strengthening controls across CI/CD pipelines, dependencies, and identity management.
- Remove all affected Checkmarx Docker images, extensions, and related artifacts, and replace them with verified, trusted versions pinned to immutable digests.
- Rotate all potentially exposed credentials, including GitHub tokens, cloud credentials, npm tokens, SSH keys, and CI/CD secrets, and transition to short-lived or just-in-time credentials where possible.
- Audit GitHub and CI/CD environments for unauthorized repositories, injected workflows, suspicious runs, and unexpected artifact generation or downloads.
- Harden CI/CD pipelines by restricting workflow creation, limiting token permissions, enforcing least privilege, and requiring approvals for new or modified workflows.
- Monitor endpoints, build systems, and cloud environments for anomalous behavior, including unexpected runtime execution (e.g., Bun), credential access, and abnormal token usage.
- Strengthen supply chain security by pinning dependencies, verifying artifacts, enforcing registry allowlists, and implementing SBOM tracking for visibility.
- Test incident response plans with supply chain attack scenarios to validate detection, containment, and recovery capabilities.
Taking these steps helps organizations build resilience against supply chain attacks while limiting the potential blast radius if a compromise occurs.
The Shift to Supply Chain Threats
This incident reflects a broader shift in attacker focus toward the software supply chain, where compromising trusted tools can provide access to multiple environments through a single entry point.
It also highlights the focus on credential-based attacks, where stolen tokens, keys, and secrets enable persistence and movement across systems, pipelines, and cloud environments.
These evolving risks are why organizations are using zero trust solutions to help manage trust and limit blast radius of supply chain incidents.