The Bitwarden CLI has been compromised as part of the ongoing Checkmarx supply chain campaign, with attackers injecting malicious code into an official release through a poisoned CI/CD workflow.
According to a brief report from the Socket Research Team, the compromised package is @bitwarden/cli version 2026.4.0, which contains malicious code embedded in the file bw1.js. The researchers identified the issue during ongoing monitoring of the broader Checkmarx campaign, which has already impacted multiple developer ecosystems.
Bitwarden is a widely used open-source password manager that provides secure credential storage and sharing for individuals and enterprises. Its CLI tool is commonly integrated into developer workflows and automation pipelines, making it a high-value target for attackers seeking access to sensitive credentials, API keys, and infrastructure secrets.
Initial analysis suggests the attackers gained access by exploiting a GitHub Actions workflow in Bitwarden’s CI/CD pipeline. This mirrors previously documented techniques in the Checkmarx campaign, where threat actors leveraged stolen credentials to inject malicious workflows, exfiltrate secrets, and tamper with build outputs before distribution. In this case, the malicious code was introduced during the automated build process and subsequently published as part of a legitimate CLI release.
CyberInsider has reached out to Bitwarden for comment, and a spokesperson sent the following statement:
The Bitwarden security team identified and contained a malicious package that was briefly distributed through the npm delivery path for @bitwarden/cli@2026.4.0 between 5:57 PM and 7:30 PM (ET) on April 22, 2026, in connection with a broader Checkmarx supply chain incident.
The investigation found no evidence that end user vault data was accessed or at risk, or that production data or production systems were compromised. Once the issue was detected, compromised access was revoked, the malicious npm release was deprecated, and remediation steps were initiated immediately.
The issue affected the npm distribution mechanism for the CLI during that limited window, not the integrity of the legitimate Bitwarden CLI codebase or stored vault data.
Users who did not download the package from npm during that window were not affected. Bitwarden has completed a review of internal environments, release paths, and related systems, and no additional impacted products or environments have been identified at this time. A CVE for Bitwarden CLI version 2026.4.0 is being issued in connection with this incident.
Checkmarx supply chain incident
The broader Checkmarx supply chain attack, uncovered earlier by Socket in collaboration with Docker, revealed a multi-stage compromise affecting container images, VS Code extensions, and developer tooling tied to Checkmarx’s KICS platform. In that campaign, attackers deployed a payload known as mcpAddon.js, designed to harvest credentials from developer environments, including GitHub tokens, cloud provider credentials (AWS, Azure, Google Cloud), npm tokens, SSH keys, and environment variables.
The malware also demonstrated worm-like behavior, using stolen GitHub tokens to automatically inject malicious GitHub Actions workflows into accessible repositories. These workflows were designed to extract repository secrets by serializing them into artifacts, which attackers could later retrieve. Additionally, the operation included mechanisms to republish compromised npm packages, enabling further propagation across the software supply chain.
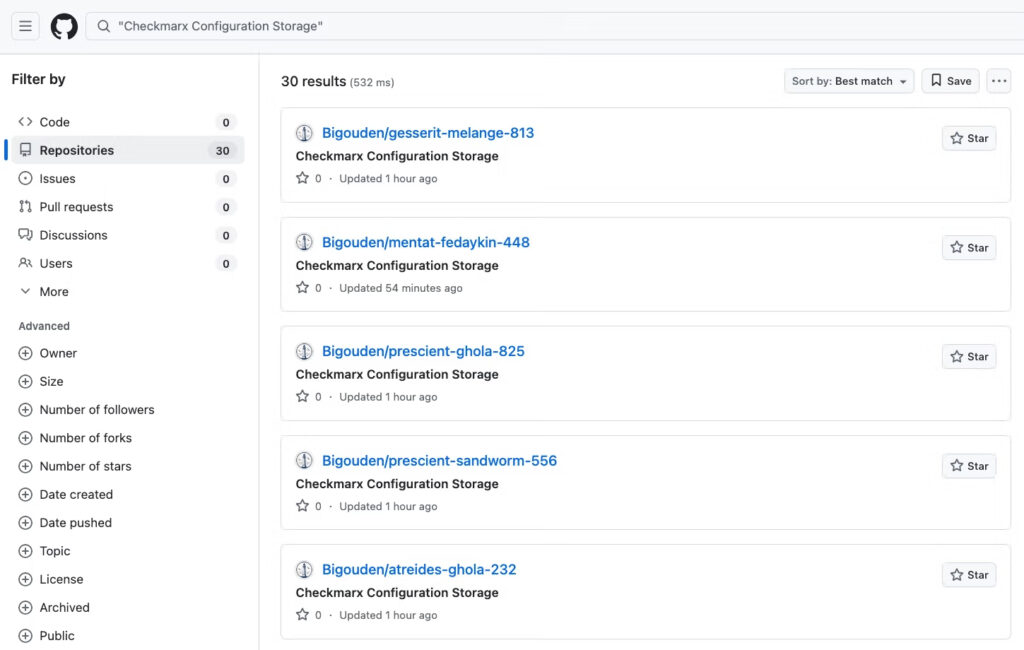
Socket
Although it is not yet confirmed whether the Bitwarden CLI compromise includes the same payload or capabilities, the reuse of the GitHub Actions attack vector strongly suggests a shared origin.
Organizations using Bitwarden CLI are advised to treat this as a potential credential exposure event. Recommended actions include:
- Review CI/CD logs for unusual workflow activity or unauthorized changes
- Rotate all secrets that may have been accessible to the affected pipelines
- Verify the integrity of downloaded CLI versions and avoid using v2026.4.0
- Monitor for suspicious outbound connections or unexpected automation behavior
Given the campaign’s focus on developer infrastructure, security teams should also audit GitHub repositories for unauthorized workflows and ensure that CI/CD permissions are tightly scoped.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.