editorially independent. We may make money when you click on links
to our partners.
Learn More
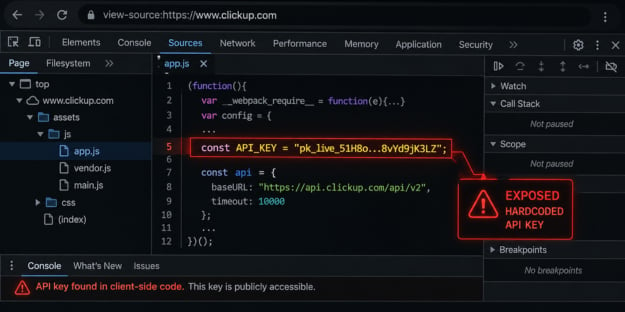
A hardcoded API key embedded in ClickUp’s public website has quietly exposed hundreds of corporate and government email addresses for more than a year.
The flaw, first reported in early 2025, remained active as of April 2026 — allowing anyone to access sensitive data with a simple request and no authentication.
“I went to http://clickup[.]com, opened the page source, and found a hardcoded API key in the javascript. I sent one GET request and got back 959 email addresses and 3,165 internal feature flags,” said security researcher Impulsive in their X post about the issue.
ClickUp Data Exposure Explained
The exposure originated from ClickUp’s web application, where a publicly accessible JavaScript file loaded prior to authentication contained a hardcoded third-party API key.
Because client-side code is inherently visible, the key could be easily extracted and used to query a backend endpoint via an unauthenticated GET request.
This lack of access controls exposed a dataset including 959 email addresses and 3,165 internal feature flags, impacting employees from large organizations and government entities across multiple regions.
Beyond revealing personally identifiable information (PII), the feature flags provide insight into internal development processes such as beta features, A/B testing, and product roadmap signals.
This information could be leveraged for targeted attacks, competitive intelligence, or platform abuse.
Reported in January 2025 and still unresolved at the time of publication, the vulnerability has heightened the risk of targeted phishing, credential stuffing, and other social engineering attacks.
Reducing SaaS Security Risks
In light of the ClickUp incident, organizations should take a more proactive approach to SaaS security, especially around credentials and API exposure.
Hardcoded keys, limited access controls, and lack of visibility into third-party integrations can create unnecessary risk and extend exposure windows.
- Enforce strong authentication and access controls, including phishing-resistant MFA, conditional access policies, and device trust requirements across all SaaS platforms.
- Monitor for signs of compromise by auditing access logs, tracking domain exposure in threat intelligence feeds, and detecting anomalous login or API activity.
- Strengthen email and phishing defenses with DMARC, DKIM, SPF, and email security tools to reduce the risk of targeted social engineering attacks.
- Limit exposure and access by applying least privilege, restricting sensitive workflows in third-party tools, and minimizing publicly accessible user or directory data.
- Conduct regular third-party risk assessments and SaaS security posture reviews to identify misconfigurations, excessive permissions, and delayed remediation.
- Implement strong credential and API key hygiene by rotating secrets regularly, scoping tokens appropriately, and avoiding hardcoded credentials in client-side code.
- Test incident response plans and use attack simulation tools with scenarios around hardcoded keys and targeted phishing attacks.
Collectively, these measures help strengthen organizational resilience while reducing overall exposure to credential misuse, misconfigurations, and SaaS-related security risks.
Preventable Security Risks
This incident highlights a preventable issue — hardcoded credentials in client-side code — and reinforces that even larger organizations can overlook basic security controls.
It also illustrates how a single misconfiguration, when combined with limited access restrictions and delayed remediation, can lead to prolonged exposure.
The implications extend beyond ClickUp, as many organizations rely heavily on third-party SaaS platforms to support core operations.
These challenges reinforce the need for a zero trust approach, where access is continuously verified and tightly controlled regardless of user, device, or environment.