editorially independent. We may make money when you click on links
to our partners.
Learn More
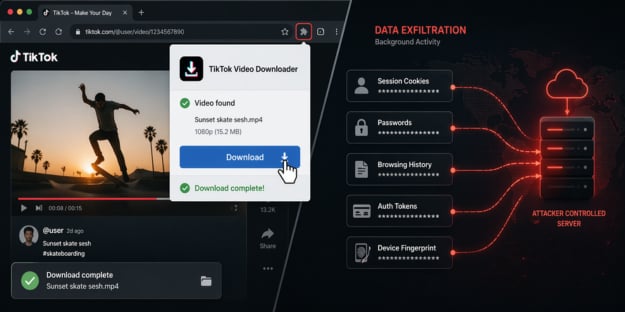
A widespread browser extension campaign is quietly compromising users by disguising data-stealing tools as TikTok video downloaders.
“While many people see browser extensions as harmless little widgets, oftentimes they have no idea who is actually behind these extensions, and what capabilities they contain within their source code,” said Natalie Zargarov, security researcher at LayerX in an email to eSecurityPlanet.
She added, “This is why users and enterprises need to be vigilant about the extensions they install, to make sure their sensitive data is not stolen.”
Inside the StealTok Extension Campaign
This campaign underscores a growing blind spot in enterprise security: browser extensions that appear legitimate at install time but evolve into active threats long after they’ve gained user trust.
According to LayerX researchers, more than 130,000 users have already been impacted, with thousands of installations still active.
Because these extensions come from trusted marketplaces like Chrome and Edge — and are sometimes even listed as “Featured” — they often bypass user skepticism and basic security controls.
How the Malicious Extensions Built Trust
According to LayerX’s research, at least 12 interrelated extensions were involved in the campaign.
While they appeared to be separate tools, they all shared a common codebase and were marketed as TikTok video downloaders.
On the surface, they delivered exactly what users expected — downloading videos, often without watermarks — which helped them build credibility and maintain a low profile.
This legitimate functionality played a key role in evading early detection and gaining widespread adoption.
Covert Behavior and Remote Control Capabilities
Behind the scenes, however, these extensions operated very differently. They incorporated covert tracking mechanisms and leveraged attacker-controlled remote configuration servers.
This capability allowed the threat actors to dynamically modify the extensions’ behavior after installation — enabling new features, expanding data collection, or redirecting traffic — without requiring updates through official extension stores.
By doing so, they effectively bypassed marketplace review processes and kept malicious activity hidden from both users and platform operators.
Systemic Weakness in Extension Security Models
At its core, this is a systemic weakness in how browser extensions are trusted and managed.
Extensions often request broad permissions and run within the browser, exposing sensitive data, session tokens, and user activity — access that’s often difficult to monitor or limit once granted.
Delayed Activation and Evasion Techniques
The campaign’s use of delayed capability injection further complicates detection.
Many of the extensions behaved normally for six to twelve months, allowing them to build a reputation and accumulate users before introducing more invasive functionality.
This delayed activation model makes it difficult for both marketplace reviewers and security tools to identify malicious intent during initial analysis.
In addition to behavioral manipulation, the extensions collected high-entropy fingerprinting data, including device characteristics, usage patterns, language settings, and even battery status.
When combined, this data enables persistent tracking of users across sessions and potentially across multiple services.
Reducing Browser Extension Risk
Browser extensions can pose security risks if not properly managed, as they often have access to user activity and sensitive data.
Managing these risks requires a focused approach to limiting permissions, monitoring behavior, and reducing unnecessary data exposure.
- Restrict and control browser extensions by enforcing allowlists, limiting high-risk categories, and auditing installed extensions regularly.
- Apply least-privilege principles by minimizing extension permissions and restricting access to only necessary domains and data.
- Continuously monitor extension behavior and network activity to detect anomalies, including unexpected outbound connections or permission changes.
- Implement browser isolation, segmentation, or separate profiles to prevent extensions from accessing sensitive systems and sessions.
- Strengthen detection and response by integrating browser telemetry into SIEM or XDR tools.
- Limit data exposure by enforcing data loss prevention controls and restricting extension access to sensitive information and authenticated sessions.
- Test incident response plans and use attack simulation tools with scenarios around malicious extensions and data exfiltration.
Together, these practices help organizations build resilience while reducing unnecessary exposure to extension-related risks.
The Shift Beyond One-Time Malware
The StealTok campaign highlights a shift in how attackers maintain access, moving beyond one-time malware to more persistent methods that leverage trusted platforms.
Browser extensions are especially attractive in this context because they operate within the user’s session and can bypass some traditional security checks.
While marketplace reviews tend to focus on initial approval, this case shows how risk can develop over time through updates and changes in behavior after installation.
These challenges reinforce the need for using zero trust, which helps continuously verify access and ensures no inherent trust.