
A wave of malicious iOS apps posing as legitimate cryptocurrency wallets has been discovered on Apple’s App Store, aiming to steal users’ recovery phrases and compromise their funds.
The campaign, uncovered by Kaspersky and tracked as FakeWallet, has likely been operating undetected since at least late 2025.
The operation involved at least 26 apps impersonating widely used wallets, including MetaMask, Coinbase, Trust Wallet, Ledger, TokenPocket, imToken, and Bitpie. The apps relied on cloned logos and subtle name variations to pass as legitimate offerings and rank in search results, particularly in the Chinese App Store, where restrictions on crypto apps create an opportunity for impersonators.
Apple has removed a number of the identified apps after being notified of the findings. We contacted Apple for comment on the campaign and its review process, but did not receive a response by the time of publication.
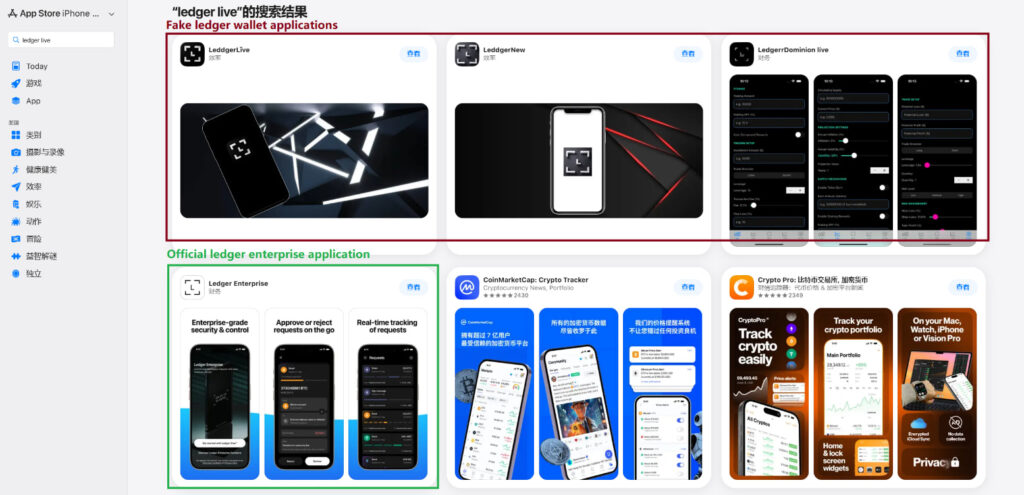
Kaspersky
The malicious apps often appeared harmless at first glance, functioning as simple tools like calculators or games to avoid raising suspicion. However, once launched, they redirected users to external pages that mimicked official download prompts, instructing them to install modified versions of cryptocurrency wallets.
This technique abuses Apple’s enterprise provisioning system, which allows apps to be installed outside the App Store. Attackers leverage this feature to sideload trojanized wallet apps without undergoing Apple’s standard review checks.
After installation, the fake wallets are engineered to intercept recovery phrases, the key to accessing and controlling cryptocurrency funds. The malware alters wallet functionality to capture sensitive input during setup or recovery.
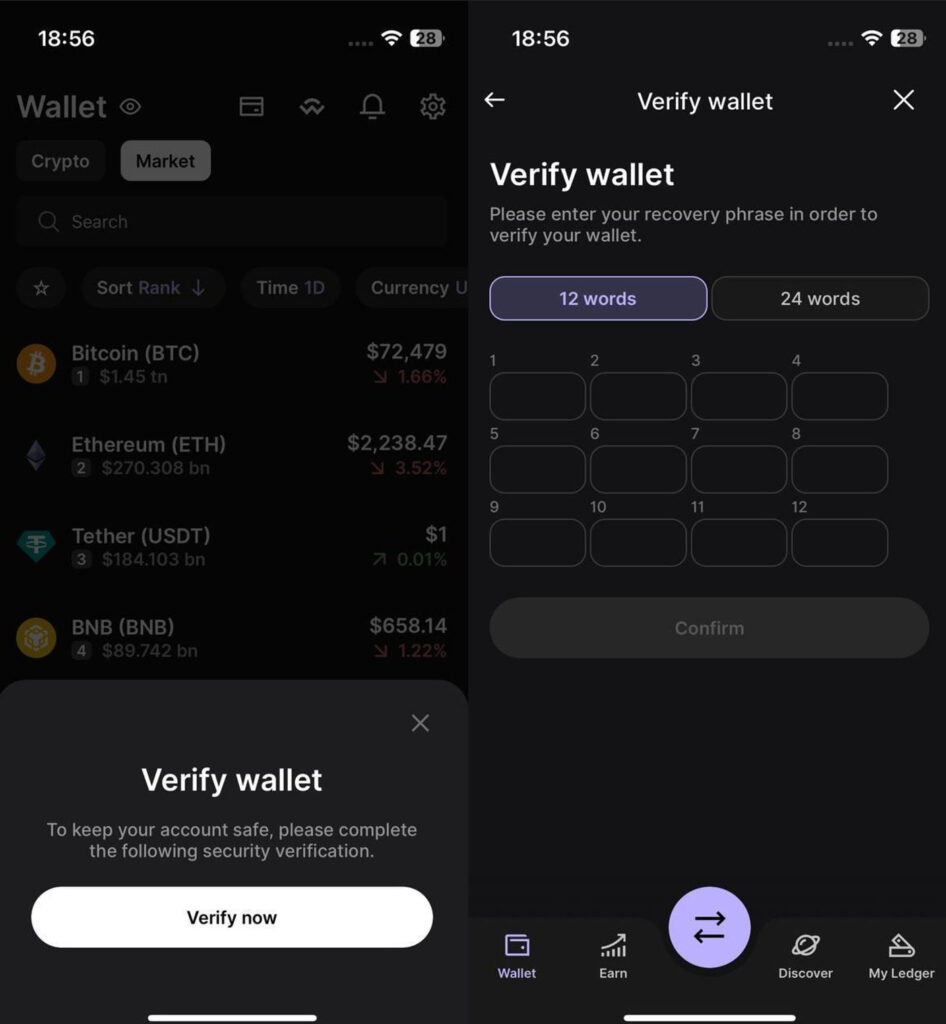
In some cases, particularly involving Ledger-themed apps, users are shown fake “security verification” prompts that lead to convincing phishing screens. These interfaces mimic legitimate wallet behavior and request seed phrases under false pretenses.
Once entered, the data is encrypted and sent to attacker-controlled servers, enabling full access to victims’ wallets.
Kaspersky
The campaign primarily targets users in China, but the malware itself does not enforce geographic limits and could affect users elsewhere. Kaspersky also identified Android versions of the trojanized wallets distributed through phishing websites, indicating a cross-platform operation.
Users should exercise caution when installing cryptocurrency apps, especially if official versions are unavailable in their region. It is recommended to download apps only from verified developers, treat redirections outside the App Store with suspicion, and reject the installation of provisioning files.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


