
A new banking trojan named TCLBANKER spreads through victims’ own WhatsApp and Microsoft Outlook accounts, allowing the malware to propagate autonomously.
According to researchers at Elastic Security Labs, TCLBANKER appears to be a major evolution of the previously documented SORVEPOTEL/MAVERICK malware family, which is associated with banking fraud operations.
The malware is delivered through trojanized MSI installers masquerading as Logitech’s “Logi AI Prompt Builder” software. Attackers bundle a malicious DLL alongside the legitimate application to abuse DLL sideloading, enabling the malware to execute when the installer launches. Once active, TCLBANKER deploys two primary components: a banking trojan focused on credential theft and remote fraud, and a separate worm module that spreads the malware to new victims.
WhatsApp worm propagation
The worm functionality turns infected systems into active distribution nodes. Instead of relying entirely on attacker-controlled spam servers, the malware abuses victims’ trusted accounts, increasing the likelihood that recipients will open malicious messages.
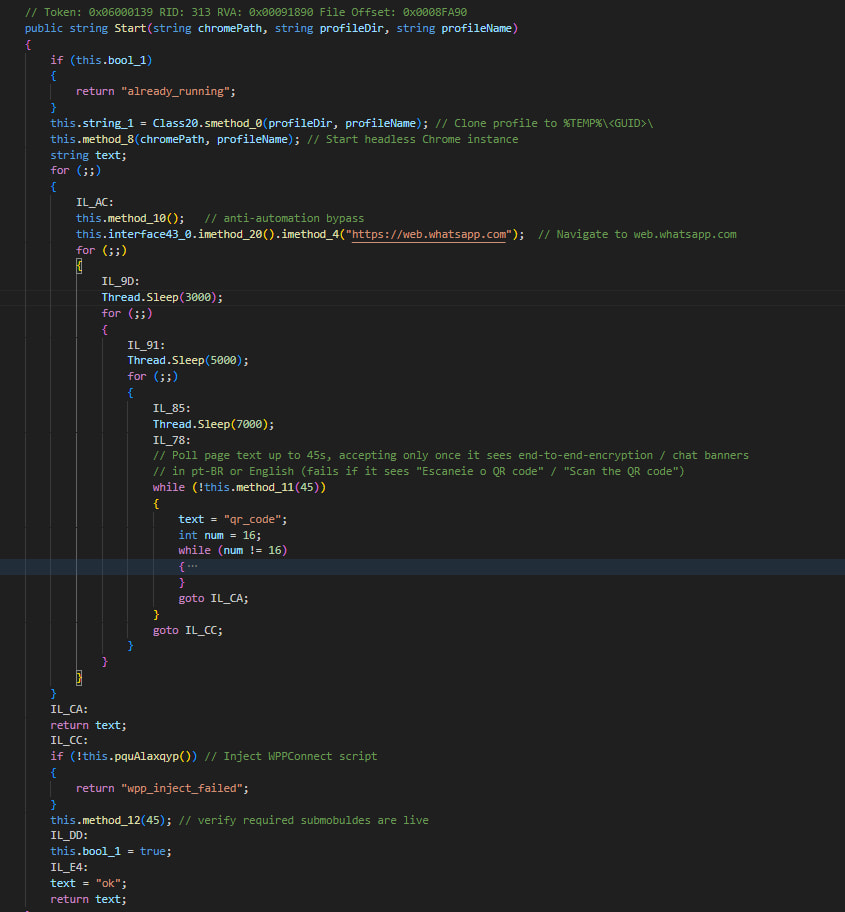
The WhatsApp propagation module hijacks authenticated WhatsApp Web sessions stored in Chromium-based browsers such as Chrome, Edge, Brave, Opera, and Vivaldi. The malware searches browser profiles for evidence of active WhatsApp Web logins and clones the necessary session files, including cookies and IndexedDB data, into a temporary directory.
Using Selenium WebDriver and a headless browser instance, TCLBANKER resumes the victim’s existing WhatsApp session without requiring QR-code reauthentication. Researchers found the malware injects JavaScript specifically designed to evade anti-bot protections by hiding automation indicators and spoofing legitimate browser characteristics.
Once access is established, the malware harvests the victim’s contact list through an embedded WhatsApp automation framework and begins distributing phishing messages and malicious files.
The malware filters contacts, focusing primarily on Brazilian phone numbers and avoiding group chats and broadcast lists. It can also receive remote instructions from operators to pause or resend campaigns while reporting delivery progress back to its command-and-control infrastructure.
Elastic Security Labs
The Outlook propagation module operates similarly but targets the corporate and business environments. If Outlook is not already running on the infected machine, the malware attempts to launch it, then attaches to it via COM automation.
The module harvests email addresses from both the victim’s contact lists and historical inbox messages, enabling attackers to build large recipient lists of trusted business contacts. It then sends phishing emails directly through the victim’s legitimate Outlook account, making the messages significantly harder for spam filters and recipients to detect as malicious.
The phishing emails observed by Elastic impersonated invoice and electronic tax document notifications and directed recipients to attacker-controlled domains hosting malicious downloads. The messages were carefully formatted in Portuguese and designed to resemble legitimate corporate communications.
Researchers also noted that TCLBANKER’s infrastructure heavily relies on Cloudflare Workers and related serverless hosting services for command-and-control operations, phishing pages, and malware delivery. This setup allows operators to rotate infrastructure rapidly while blending in with legitimate Cloudflare-hosted traffic.
Although TCLBANKER includes extensive anti-analysis protections, banking overlays, and remote-control features, Elastic believes the campaign may still be in relatively early operational stages. Investigators discovered development artifacts, debug paths, and phishing domains that were not yet fully operational at the time of analysis.
The banking trojan targets 59 banking, fintech, and cryptocurrency platforms and can deploy convincing full-screen overlays designed to steal credentials or stall victims while fraudulent transactions occur in the background.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


