A newly disclosed Windows zero-day vulnerability dubbed “RedSun” is being actively exploited in the wild, allowing attackers to gain SYSTEM privileges by abusing Microsoft Defender.
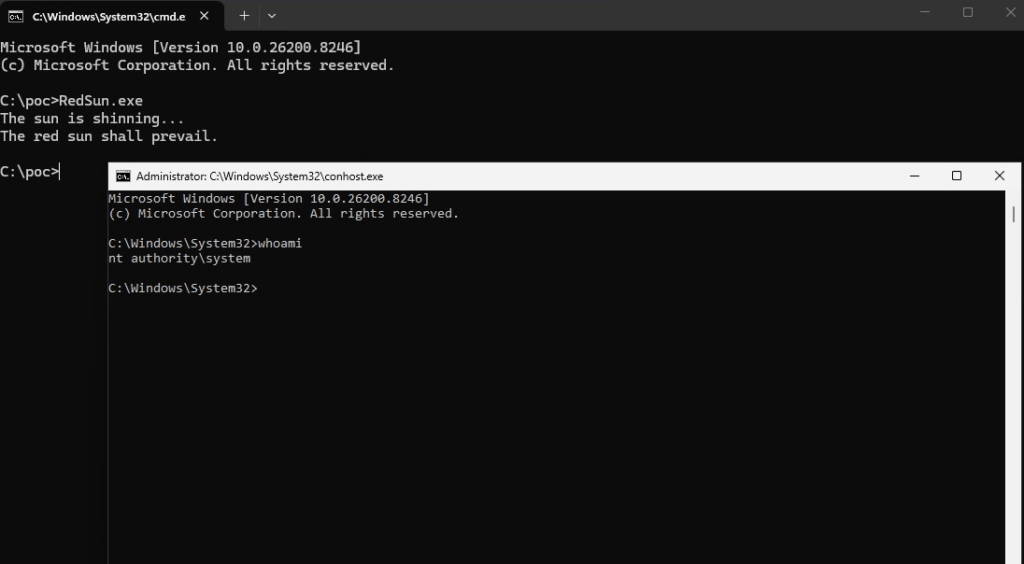
The vulnerability was publicly disclosed by the researcher “Nightmare-Eclipse,” who also released the earlier BlueHammer exploit. The proof-of-concept (PoC) code is available on GitHub and includes a fully working privilege escalation chain targeting Microsoft Defender. At the time of writing, RedSun has no CVE identifier and remains unpatched.
Shortly after its release, security firm Huntress reported real-world attacks using RedSun alongside BlueHammer and another tool called “UnDefend.” Researchers observed attackers deploying binaries such as RedSun.exe and FunnyApp.exe in user-accessible folders, such as Downloads and Pictures, often followed by hands-on activity, including system enumeration commands.
How the exploit works
RedSun exploits how Microsoft Defender handles certain files linked to cloud storage providers such as OneDrive or Dropbox.
The attack begins by registering a fake cloud sync provider using legitimate Windows APIs. The attacker then creates a specially crafted placeholder file that appears to be stored in the cloud. This file includes metadata that triggers Defender to scan and “remediate” it.
Next, the attacker silently redirects the file’s location using a Windows feature called a reparse point. This causes any access to the file’s directory to instead point to C:\Windows\System32, a highly privileged system folder.
When Defender scans the malicious file, it attempts to restore or rewrite it to its original location. However, due to the redirection, Defender ends up writing attacker-controlled content into System32 while running with SYSTEM privileges.
The researcher’s PoC demonstrates this by overwriting TieringEngineService.exe, a legitimate Windows service binary, and then launching it to achieve full system compromise.
Defender abused as an escalation path
Microsoft Defender, which runs with elevated privileges to protect the system, is central to the exploit. The issue lies in how it follows file paths during remediation without verifying that the destination hasn’t been tampered with.
This allows attackers to effectively turn Defender into a tool for privilege escalation, using its own trusted access to modify protected parts of the operating system.
Microsoft previously patched BlueHammer (tracked as CVE-2026-33825), but that fix addressed a different technique. RedSun uses a separate method and is not mitigated by the earlier update.
Mitigation and detection
Since no patch is currently available, organizations should focus on detecting suspicious behavior and limiting initial access. Recommended steps include:
- Monitoring for unexpected cloud sync provider registrations on endpoints
- Alerting on unusual use of filesystem redirection (reparse points)
- Watching for changes to critical system files like TieringEngineService.exe
- Enabling Attack Surface Reduction (ASR) rules to reduce common entry points
Although RedSun requires an attacker to already have code execution on a system, this is often achieved through phishing, malicious downloads, or browser exploits, making the risk significant in real-world scenarios.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.