Germany’s Bundestag is moving to standardize on the Wire messaging platform following a wave of phishing attacks targeting politicians, with President Julia Klöckner urging lawmakers to abandon less controlled apps like Signal.
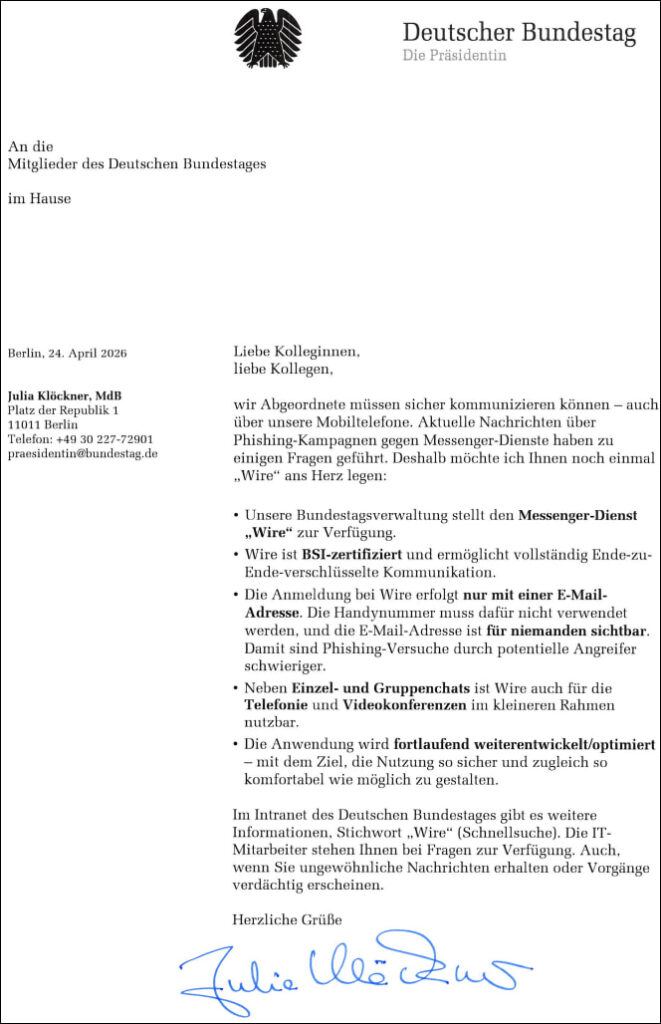
In a letter dated April 24, 2026, Bundestag President Julia Klöckner called on members of parliament (MPs) to adopt the Wire messenger for official communications. The recommendation follows recent phishing campaigns targeting the messaging platforms used by politicians, including incidents that affected Klöckner herself. The letter emphasizes the need for “secure communication,” particularly on mobile devices, where lawmakers increasingly handle sensitive discussions.
Klöckner highlighted that Wire is already provided by the Bundestag administration and is certified by Germany’s Federal Office for Information Security (BSI). The platform offers full end-to-end encryption and differs from mainstream messaging apps by allowing registration only via email address, eliminating the need for a phone number. According to Klöckner, this design reduces exposure to phishing attempts, as attackers cannot easily leverage publicly known phone numbers to impersonate users or initiate account takeover flows.
Wire’s positioning within Germany’s federal IT ecosystem further reinforces its appeal. The BSI recently approved a specialized version, “Wire Bund,” for handling classified information, enabling secure communication of sensitive government data. This version operates within controlled infrastructure managed by the ITZBund, aligning with Germany’s broader push for digital sovereignty. The certification is currently valid through 2028, though future compliance will require the integration of post-quantum cryptographic protections.
Wire, a Switzerland-based secure communications provider led by CEO Benjamin Schilz, has increasingly positioned itself as a privacy-centric alternative for governments and enterprises. Its platform supports encrypted messaging, group chats, voice calls, and video conferencing, and can be deployed in on-premise environments for tighter administrative control.
Signal faces scrutiny following a series of phishing-based account hijackings. As previously reported, attackers impersonated Signal support staff to trick users into revealing registration codes and PINs, enabling them to re-register accounts on devices under their control. Signal clarified that its infrastructure and encryption were not compromised, attributing the incidents entirely to social engineering.
In response, Signal has announced upcoming anti-phishing safeguards to reduce the risk of such attacks. Planned measures include enhanced user protections against fraudulent support messages and stronger account security mechanisms, though technical details remain limited.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.