Fiverr appears to have exposed user-uploaded files through publicly accessible Cloudinary URLs, with many assets indexed by Google search results.
The exposure was reported by user ‘morpheuskafka,’ on Hacker News. CyberInsider’s independent verification confirms the platform serves files via a public CDN without authentication, though we did not directly test the presence of sensitive data.
Fiverr is a publicly traded online marketplace headquartered in Israel that connects businesses with freelancers offering services ranging from graphic design and programming to financial consulting and document preparation. The platform handles a large volume of user-generated content, often including business documents, identification records, and other sensitive materials exchanged during project workflows.
The user who discovered the exposure states that Fiverr uses Cloudinary to process and deliver documents exchanged between freelancers and clients, including PDFs and images. Cloudinary is a cloud-based media management platform that supports access-controlled delivery via signed, expiring URLs. Fiverr reportedly configured these assets as publicly accessible, effectively treating Cloudinary as an open file host rather than a secure storage layer.
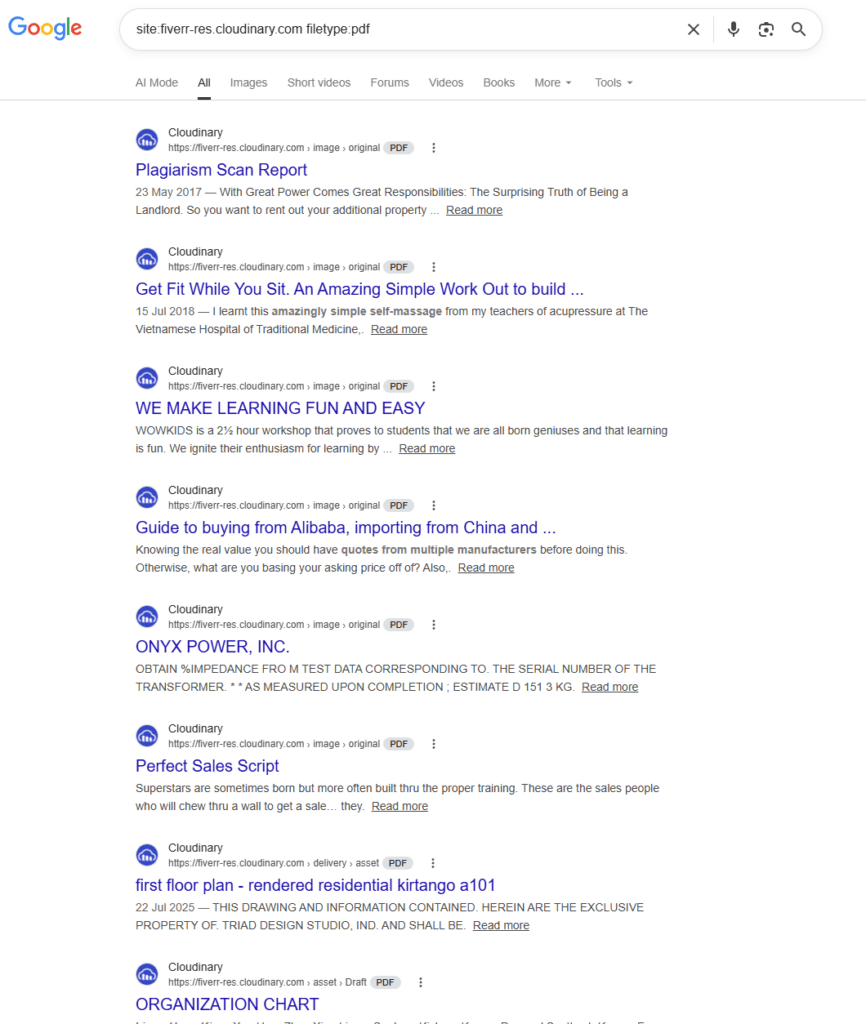
This configuration allowed documents shared in private conversations to be accessed via direct URLs, without authentication. The user further claimed that some of these URLs were linked in publicly accessible HTML pages, enabling search engines like Google to crawl and index them. Example search queries reportedly returned documents such as tax forms and other potentially sensitive files.
The reporter stated that Fiverr was notified of the issue via its designated security contact approximately 40 days prior to public disclosure, but did not respond. At the time of writing, Fiverr has not issued a public statement, and the company did not respond to our request for comment.
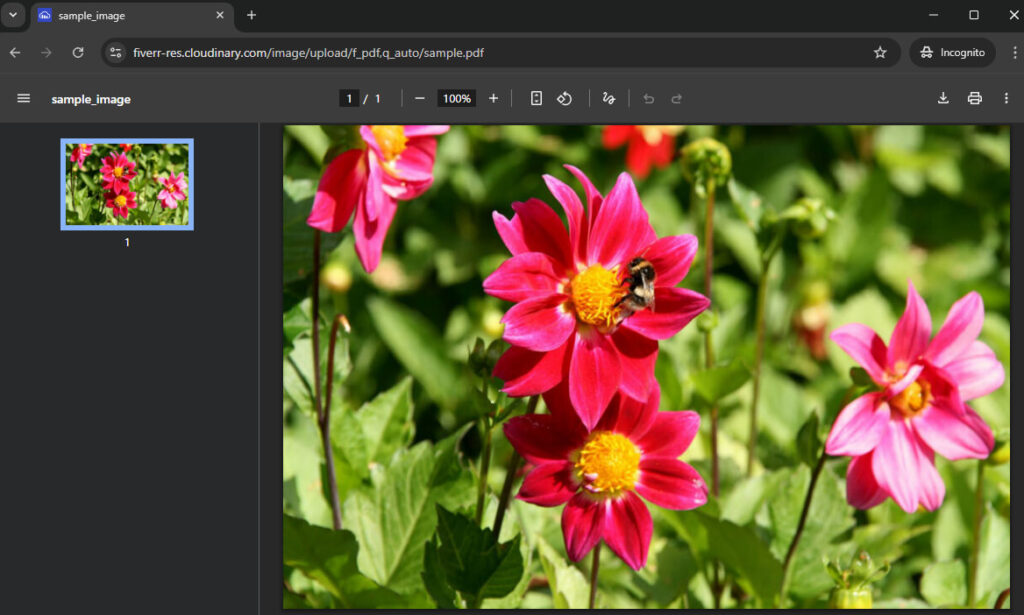
To validate the claims, we conducted limited testing and confirmed that Fiverr-hosted assets are served via Cloudinary URLs with no authentication required. These URLs were directly accessible in a browser, consistent with a public delivery configuration.
We also verified that some of these assets are indexed by Google, indicating they are discoverable through search queries. However, we did not attempt to locate or access documents containing personally identifiable information (PII) or other sensitive data.
Until Fiverr clarifies the scope of the issue and implements safeguards, users of the platform are advised to take precautions to reduce exposure, such as avoiding uploading sensitive information unless absolutely necessary and using password-protected files when possible.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.