editorially independent. We may make money when you click on links
to our partners.
Learn More
Identity security is one of the most urgent priorities for enterprises as AI adoption expands the attack surface and introduces new complexity.
The SpecterOps Trends in Identity Attack Path Management 2026 report highlights how organizations are increasing investment in identity security while struggling to turn visibility into consistent risk reduction.
“As identity becomes the control plane for more of the enterprise, the challenge is no longer just getting visibility,” said Jared Atkinson, CTO at SpecterOps in an email to eSecurityPlanet.
He explained, “Organizations are now working to build cross-functional discipline to prioritize findings and drive remediation, reducing attack paths over time.”
Jared added, “This effort becomes even more important as AI adoption introduces more non-human identities and trust relationships, and therefore more legitimate paths for an attacker to take.”
How AI Is Expanding Identity Risk
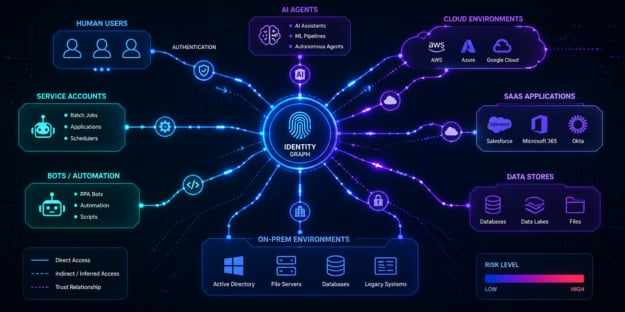
As organizations adopt AI agents and automate more workflows, the number of identities interacting with systems and data is expanding rapidly.
This includes not only human users, but also non-human identities (NHIs) such as service accounts, bots, and AI-driven processes.
Each new identity introduces additional access points, increasing the risk of misconfigurations, excessive privileges, and poorly governed credentials that attackers can exploit.
Why Attack Path Visibility is a Priority
This growing complexity is shifting how organizations prioritize security.
According to the SpecterOps report, 43% of organizations now rank attack path visibility as a top cybersecurity priority — surpassing even AI integration initiatives.
Before organizations can scale AI securely, they need clear visibility into how access and privileges are connected across their environments.
The Rise of Identity Attack Path Management
To address this challenge, Identity Attack Path Management (APM) is gaining traction as a key security capability.
The report shows that 35% of organizations have fully implemented identity APM solutions, up from 21% the previous year, and more than half are already using automated tools to discover identity-based attack paths.
This reflects a shift from simply managing identities to actively analyzing how those identities interact and create potential pathways for compromise.
How Identity Attack Paths Work
At its core, identity attack path management focuses on identifying how an attacker could move through an environment by chaining together access relationships.
These paths often span multiple systems, accounts, and environments, combining elements such as credential exposure, privilege escalation, and trust relationships.
For example, an attacker might leverage a low-privileged account, escalate permissions through misconfigurations, and eventually gain access to critical systems.
Because these paths are rarely linear and often cross cloud and on-prem environments, they can be difficult to detect without specialized tooling.
The Impact of Non-human Identities
The challenge is further compounded by the rapid growth of non-human identities.
The report notes that 34% of organizations already view managing NHIs as a significant challenge, as these identities frequently accumulate privileges faster than governance processes can keep up.
As AI adoption continues to accelerate, the number of machine identities — and the complexity of their relationships — will increase, making it even more difficult for security teams to maintain visibility and control.
A Shift toward Interconnected Identity Security
Together, these trends highlight a broader shift in identity security. It is no longer enough to manage users and permissions in isolation.
To effectively reduce risk in dynamic, automated environments, organizations need clear visibility into how identities, privileges, and systems are interconnected — and where those connections could be exploited.
How to Reduce Identity Security Risk
Modern environments include a mix of human users, service accounts, and automated processes, all of which introduce new access paths that can be exploited if not properly managed.
Addressing this risk requires a comprehensive approach that goes beyond basic identity and access management.
- Implement identity attack path management by continuously discovering attack paths, validating exposures, and treating identity relationships as critical dependencies.
- Enforce least privilege and just-in-time access across human and non-human identities to reduce standing privileges and limit attack paths.
- Establish strong identity governance with clear ownership, access reviews, lifecycle management, and alignment to frameworks.
- Secure and segment critical systems and identity infrastructure to limit lateral movement and reduce blast radius.
- Continuously monitor, log, and correlate identity activity across environments to detect anomalies and support threat hunting and forensics.
- Apply proactive testing through red teaming and attack simulations to identify gaps in identity controls and validate defenses.
- Develop and regularly test identity-focused incident response plans to improve resilience and reduce exposure to identity-based attacks.
Collectively, these steps help organizations reduce identity-related exposure and build resilience against evolving threats.
Identity Is Central to Security
The SpecterOps report reflects an ongoing shift in enterprise security, where identity is playing an increasingly central role.
As AI adoption expands and more processes become automated, organizations are managing a growing number of identities, credentials, and access relationships.
While tools can improve visibility into identity risk, organizations still need to operationalize that insight by prioritizing issues, coordinating remediation, and maintaining ongoing oversight.
These challenges are also driving organizations to adopt zero trust solutions that continuously verify identities and enforce strict access controls.