editorially independent. We may make money when you click on links
to our partners.
Learn More
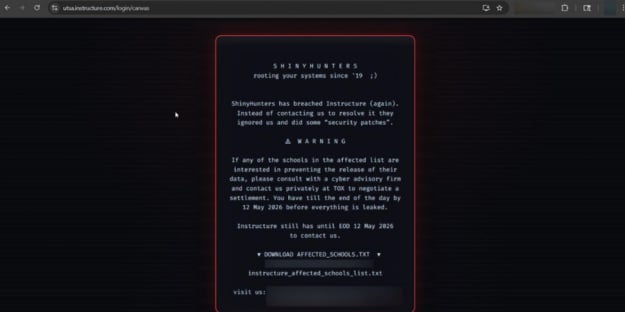
Students across the United States were locked out of coursework, quizzes, and grades during finals week after threat actors defaced hundreds of Canvas login portals in a ShinyHunters-linked extortion campaign.
The disruption impacted colleges, universities, and school districts worldwide, underscoring the growing cybersecurity risks facing cloud-based education platforms.
“ShinyHunters has breached Instructure (again). Instead of contacting us to resolve it they ignored us and did some ‘security patches,’” the group wrote in a Canvas login portal defacement message, according to BleepingComputer.
Key Takeaways from the Canvas Incident
- ShinyHunters-linked threat actors defaced Canvas login portals affecting approximately 330 educational institutions at this time.
- The disruption impacted students and faculty during finals week, limiting access to coursework, grades, and assignments.
- The incident follows claims that attackers stole 280 million student and staff records tied to Canvas platforms.
- Reports indicate the attackers exploited a vulnerability that allowed modification of institutional login pages.
- The campaign highlights the growing risks associated with centralized cloud-based education platforms and SaaS extortion tactics.
What We Know So Far About the Recent Canvas Incident
| Incident Detail | Reported Information |
| Affected Platform | Instructure Canvas |
| Threat Actor Group | ShinyHunters |
| Attack Type | Extortion and portal defacement |
| Estimated Institutions Impacted | Approximately 330 |
| Reported Impact | Login portal defacement, service disruption |
| Attack Timing | During U.S. university finals week |
| Affected Regions | United States and reportedly Australia |
| Vendor Response | Canvas placed into maintenance mode while investigation continues |
Canvas Outage Impacts Universities Worldwide
The incident has reportedly impacted approximately 330 educational institutions, with defacement notices appearing on both Canvas login portals and the Canvas mobile app.
Universities including Columbia, Georgetown, Harvard, Princeton, Rutgers, and Kent State warned students and faculty about the disruption, while Reddit users also reported affected universities in Australia.
Because Canvas serves as a centralized learning management platform for thousands of institutions worldwide, the disruption quickly spread across multiple regions and academic environments.
The timing of the attack amplified its impact.
Many colleges and universities in the United States are currently in the middle of final exams, leaving students unable to access coursework, quizzes, study materials, grades, and assignment submissions.
Professors and administrators also reportedly experienced issues finalizing grades and managing end-of-semester academic operations as Canvas services became unavailable.
Instructure Investigates Alleged Data Theft in Previous Incident
The latest disruption comes only days after Instructure disclosed it was investigating claims that threat actors had stolen approximately 280 million student and staff records tied to more than 8,800 schools and educational platforms using Canvas.
According to the attackers, the allegedly stolen data includes user records, enrollment information, and private messages that were reportedly accessed through Canvas APIs and data export features.
Instructure has confirmed that data was accessed during that broader incident but said its investigation remains ongoing.
Attack Highlights Risks of Centralized SaaS Platforms
Reports indicate the defacement campaign exploited a vulnerability in Instructure’s systems that allowed attackers to modify institutional login pages.
Although technical details have not been disclosed, the incident highlights how extortion groups increasingly combine data theft with public disruption to pressure organizations into paying ransoms.
The campaign also underscores the growing risks associated with centralized cloud-based education technology ecosystems.
Because thousands of schools depend on a single platform provider, a compromise affecting one vendor can rapidly cascade across hundreds of institutions simultaneously.
In response to the incident, Instructure later placed Canvas into maintenance mode while investigating and responding to the attack.
The company said it continues working to determine the full scope of the breach and restore affected services.
How Organizations Can Improve Cyber Resilience
As extortion groups increasingly target SaaS providers that store large volumes of sensitive student and staff data, organizations should reassess how they secure learning management systems and connected services.
- Review privileged account access and enforce role-based access controls to limit unnecessary exposure to sensitive systems and data.
- Require phishing-resistant multifactor authentication for administrators, faculty, and other high-risk accounts.
- Restrict unnecessary API access and closely monitor data export activity for signs of abuse or unauthorized downloads.
- Centralize authentication, API, and platform logs into a SIEM to detect suspicious activity and unauthorized portal changes in real time.
- Conduct regular third-party security assessments of cloud learning platform vendors and review their incident response and data protection practices.
- Maintain offline backups and establish alternate communication and learning continuity plans in case critical platforms become unavailable.
- Test incident response and disaster recovery plans through tabletop exercises that simulate SaaS outages, ransomware, and data extortion scenarios.
Implementing these measures can help educational institutions reduce exposure to evolving extortion threats while building greater operational resilience against future SaaS platform attacks and disruptions.
Risks of Centralized Cloud Platforms
The Canvas incident highlights the growing risks organizations face when relying heavily on centralized cloud platforms.
Educational institutions are often attractive targets because they manage large amounts of sensitive student and staff data across complex and decentralized IT environments.
The attack also reflects how extortion groups are expanding beyond traditional ransomware tactics.
Rather than focusing solely on encrypting systems, attackers are increasingly combining data theft with service disruptions and public pressure to increase leverage during negotiations.
As attacks against cloud-based platforms continue to evolve, many organizations are turning to zero trust strategies to strengthen access controls, reduce exposure, and limit the impact of compromised accounts or systems.