A surge in attacks exploiting the critical cPanel & WHM vulnerability CVE-2026-41940 has resulted in at least 44,000 compromised systems now actively scanning and launching attacks.
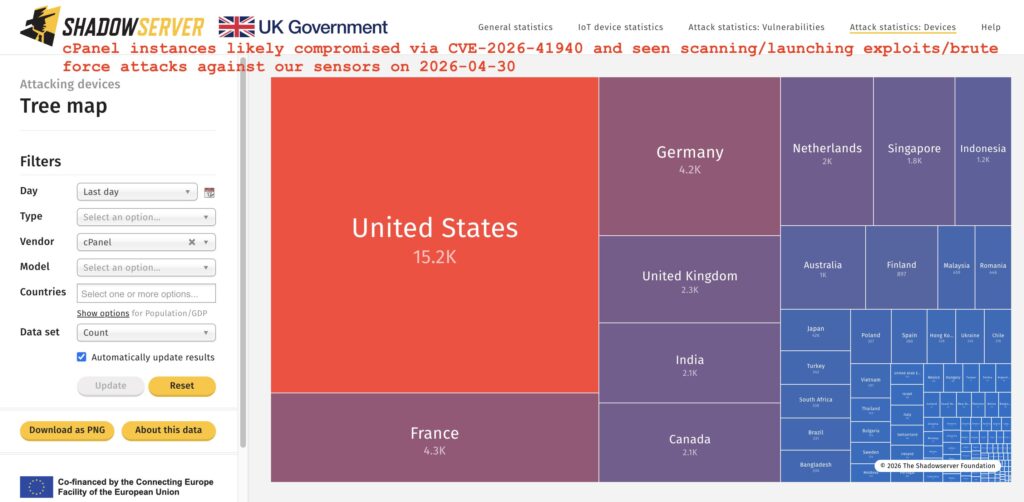
The warning was issued by Shadowserver, which reported a sharp spike in malicious traffic targeting its global honeypot sensors. The nonprofit cybersecurity organization reported that the 44,000 figure reflects unique IP addresses compromised by hackers, which are now also involved in scanning, exploitation attempts, or brute-force attacks against other vulnerable cPanel instances.
The spike follows the disclosure of CVE-2026-41940, a critical authentication bypass vulnerability affecting cPanel & WHM that allows unauthenticated attackers to gain full administrative access. The flaw stems from improper session handling and can be exploited to inject arbitrary session variables, effectively bypassing login protections. Public proof-of-concept exploit code has already lowered the barrier to entry for attackers, contributing to the rapid weaponization now being observed.
Shadowserver’s public dashboard shows the geographic distribution of the malicious activity. The United States accounts for the largest share, with approximately 15,200 IPs breached, followed by France (4,300), Germany (4,200), the United Kingdom (2,300), India and Canada (around 2,100 each), and several other countries, including the Netherlands, Singapore, and Indonesia.
cPanel & WHM is one of the most widely deployed web hosting control panels, used by hosting providers and enterprises to manage websites, email services, and server infrastructure. Its extensive adoption, powering millions of internet-facing systems, makes it a high-value target. Successful exploitation grants attackers full administrative control, enabling website defacement, data exfiltration, malware deployment, and lateral movement within hosting environments.
Beyond the 44,000 breached and actively attacking systems, Shadowserver notes that approximately 650,000 internet-exposed cPanel/WHM instances have been observed in broader device scans, highlighting a vast attack surface.
While the vulnerability was publicly disclosed on April 28, evidence suggests attackers may have been exploiting it as early as February, indicating a possible zero-day window of several weeks or longer. The current spike in activity reflects both opportunistic scanning and the incorporation of the exploit into automated attack toolkits.
Administrators should assume that unpatched systems are at high risk of compromise, apply the latest security updates released by cPanel, verify version compliance across all servers, and audit logs for suspicious session activity or unauthorized access. Additional protective measures include restricting access to cPanel/WHM ports (2083 and 2087), enforcing IP allowlists, and deploying web application firewalls or intrusion detection systems to detect exploitation attempts.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.