The idea that quantum computers could one day break today’s encryption has moved from theory into serious discussion. In practical terms, it means that the mathematical problems protecting everything from secure websites and messaging apps to cryptocurrencies could become solvable, allowing attackers to recover private keys, decrypt sensitive data, or impersonate users. While that moment hasn’t arrived yet, recent research suggests it may be closer than previously thought.
Chris Peikert is a professor of computer science at the University of Michigan and a leading researcher in lattice-based cryptography and post-quantum security, whose work has helped shape the foundations of modern post-quantum encryption, including algorithms standardized by NIST. Peikert is also the Chief Scientific Officer at Algorand, a fast proof-of-stake blockchain that uses post-quantum cryptography to support secure decentralized apps and digital assets.
We spoke with Chris Peikert about the real-world impact of quantum computing on encryption, from cryptocurrencies to VPNs, messaging apps, and the broader internet infrastructure.
“Even a small chance… presents a major risk”
CyberInsider: How much of the current concern about quantum computers breaking encryption is exaggerated marketing hype? Should we already be worried about the safety of our data?
Chris Peikert: Overall, there is a good deal of hype about quantum computing, but breaking public-key cryptography, both encryption and authentication, also known as “digital signatures,” is one of the few true “killer apps” of quantum computers. This is a task where there is an exponential “quantum advantage” over classical computers.
At a fundamental level, the security of the Internet and all cryptocurrencies would be totally undermined by large-scale quantum computers, so even a small chance that they become real in the near future presents a major risk for everyone today.
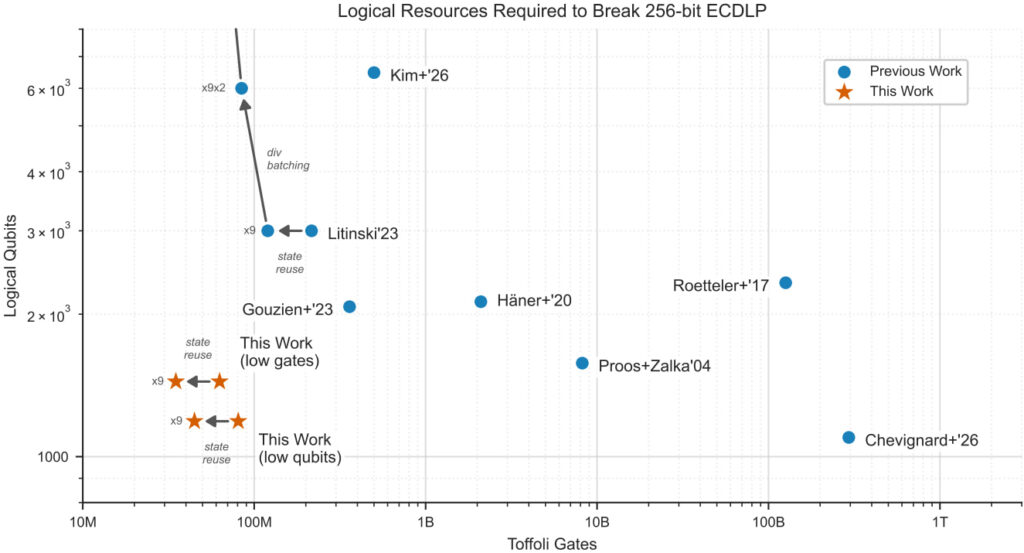
CyberInsider: Google recently published a paper suggesting quantum computers could break cryptocurrency encryption much more efficiently than previously thought, claiming that ECDLP over secp256k1 could be broken in minutes with ~1,000 logical qubits. Can you explain in simple terms what that means, and from your perspective, is this a real shift or incremental progress framed aggressively?
Chris Peikert: Put simply, this paper says that in order to break a very widely used cryptographic tool, a quantum computer would need significantly fewer resources (about 20 times fewer) than was previously known. While this is not a fundamental reshaping of our previous understanding, it is a major step forward toward real quantum computers being able to break our legacy cryptography.
CyberInsider: Some cryptographers noted that Google’s paper lacked enough proof to validate its claims. As an established scientist, did you see any red flags, or was Google’s paper “good enough” for responsible disclosure to the public?
Chris Peikert: Although the scientific community cannot directly validate the paper’s claims due to the “zero-knowledge proof” that was provided, the ultimate claims are entirely credible and in line with other recent scientific literature on closely related topics. There are no red flags or serious suspicions about the correctness of the findings.
CyberInsider: The paper suggests attacks could intercept transactions in real time or even break Bitcoin encryption, pushing all cryptocurrencies to zero value. Is that something people should take seriously today, or is it still far off?
Chris Peikert: This is not an attack that can actually be mounted today, nor (quite likely) in the next few years. However, the prospect of this attack certainly needs to be taken seriously today, because modifying existing systems to prevent such attacks in the future requires a great deal of early planning and effort, and will take significant time to complete. It is very important that such updates are successfully completed before there is a noticeable risk of quantum attacks becoming real.
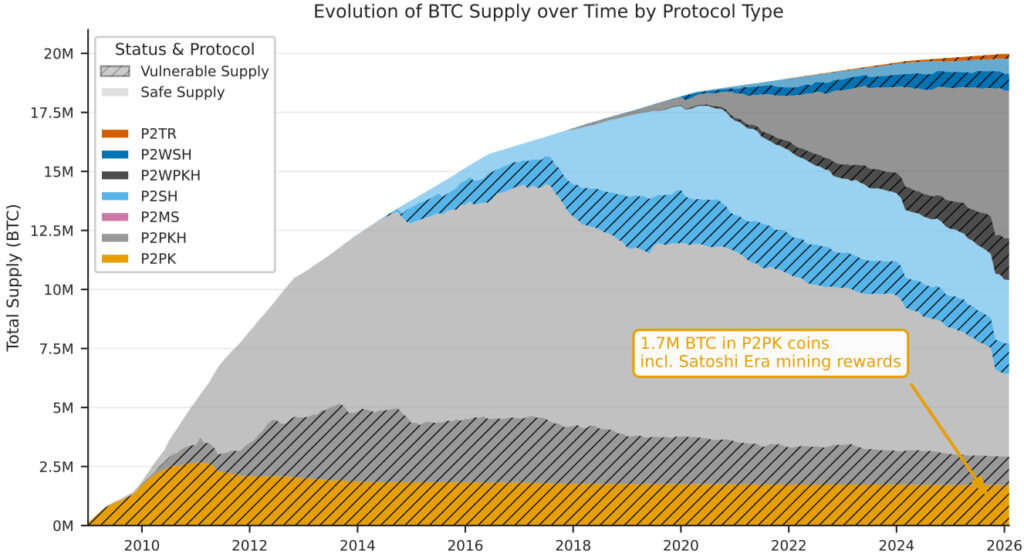
CyberInsider: Do you think it’s realistically practical to migrate cryptocurrencies to PQC, or are the complexities underestimated?
Chris Peikert: The complexities are widely understood to be high and quite challenging to overcome from a scientific and engineering perspective. With enough effort and resources, I think it’s realistic to migrate many cryptocurrency projects in time. However, compared with legacy cryptography, there is a much smaller supply of PQC expertise in the world, and considering the engineering and social challenges and other priorities, some projects may not be able to properly adapt.
CyberInsider: VPNs like ExpressVPN, Surfshark, and Nord VPN, and end-to-end encryption messaging apps like Signal and Zoom, have already adopted “quantum-resilient” algorithms approved by the US National Institute of Standards and Technology (NIST). With our current understanding, how confident are we that these (NIST PQC selections) will be strong enough to resist breakage when the time to put them to the test comes?
Chris Peikert: The core mathematics of these “post-quantum” algorithm standards has been used and studied in cryptography for about three decades, with many very talented researchers trying to break or weaken them over the years. At present, the picture for the NIST-approved algorithms is stable, with recent attack research having quite small effects on their (high) security strengths.
However, any kind of cryptography always has the possibility that some unexpected breakthrough will significantly weaken or completely break it. So, for now, it is prudent to build in some margin of safety by using the largest security levels the application can reasonably afford.
CyberInsider: If these algorithms and key encapsulation mechanisms hold up to the first, truly powerful quantum computers, does this mean that they will be safe forever against that technology?
Chris Peikert: It is important to understand that we do not need to build real quantum computers in order to analyze whether cryptographic algorithms are resilient to them.
Security analyses are based on abstract models of what quantum computers can do, and typically use very favorable assumptions and metrics about the eventual power of these computers, which makes the analysis more cautious and safer. The goal is to have cryptography that will remain secure against any kind of physically realizable computing device, whether classical or quantum.
CyberInsider: What are the biggest non-theoretical risks in PQC right now, implementation, performance, or something else?
Chris Peikert: The biggest practical risks or unknowns are probably related to implementation quirks that are specific to PQC schemes, and to whether PQC will be performant enough in real applications.
Some widely used protocols will require redesigning, or at least heavy modification, in order to incorporate PQC in a practically efficient way, and this may introduce unexpected side effects that attackers might be able to exploit in clever and qualitatively new ways.
CyberInsider: There’s a growing consensus that quantum computers mainly threaten public-key cryptography, while symmetric encryption like AES remains relatively safe. Do you agree with that distinction, as it is presented in this article by cryptography engineer Filippo Varsoda, and how important is it for people in practice?
Chris Peikert: Yes, this analysis is broadly agreeable. As far as we know, existing symmetric-key cryptography is much less vulnerable to realistic quantum attacks than public-key cryptography is. Quantum computers can obtain some small theoretical advantages in attacking symmetric cryptography, but not enough to be a major concern in practice compared to other higher-priority considerations, such as migrating public-key cryptography.
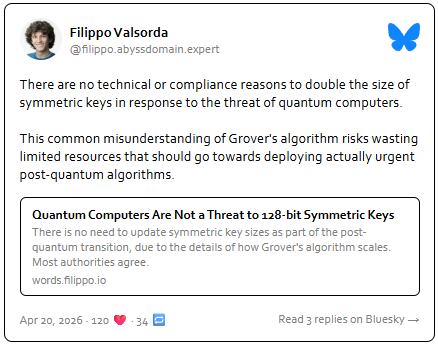
CyberInsider: Varsoda also argues that we’ll need to double symmetric key sizes because of quantum attacks, while others find that unnecessary. From your perspective, is that concern justified, or is it a misunderstanding of how quantum algorithms like Grover’s actually work?
Chris Peikert: I agree with that article and the research used to reach its conclusions.
“It is far too late to wait”
CyberInsider: What is your timeline estimate for when quantum computing becomes an actual threat to conventional cryptography schemes? Could the technology arrive “suddenly,” and catch everyone unprepared?
Chris Peikert: If “suddenly” means a huge unanticipated public breakthrough in quantum-computing hardware, I think this is pretty unlikely. Public players in the quantum-computing space report their improvements, which have followed fairly closely the extrapolations of prior progress. We will continue to see a steady march forward in building larger-scale devices.
However, another notion of “suddenly” is fairly likely to occur: it will take relatively little time to go from quantum breaking scaled-down “toy” cryptography (e.g., 20-bit elliptic curves) to breaking full-sized, deployed cryptography. This is because the marginal improvement in quantum hardware to take this step is quite small compared to what’s still needed to break “toy” cryptography in the first place.
So, it will likely take some time to reach that first point, and then we will “suddenly” reach the endpoint. This is why it is far too late to wait until “toy” schemes are quantumly broken before preparing to migrate. All this refers to the public players. It is very hard to have any confidence on where the classified/secret research lies, including that of other large countries.
CyberInsider: What’s the most misleading narrative currently circulating about quantum threats to cryptography?
Chris Peikert: Some have said that quantum computers are just a fantasy, and that migration to post-quantum cryptography should only happen if large quantum computers are fairly likely to emerge fairly soon.
This gets the risk analysis wrong, because quantum computers would be totally catastrophic to legacy cryptography. Instead, migration to PQC should happen unless there is high confidence that large quantum computers will not emerge, and knowledgeable people do not have any good reason to believe this.
CyberInsider: If you had to give one piece of advice to people worried about their data security, or the quantum threat to encryption, what would that be?
Chris Peikert: Users should seek out products and services that have made it an early priority to migrate to post-quantum cryptography, that have the long-term expertise to execute on that migration, and that use standard and well-vetted public algorithms to do so.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.