editorially independent. We may make money when you click on links
to our partners.
Learn More
A vulnerability in GitHub’s infrastructure could have allowed attackers to execute code on backend systems using nothing more than a standard git push command.
The flaw affected both GitHub.com and GitHub Enterprise Server (GHES), exposing millions of repositories to potential compromise before it was patched.
“By exploiting an injection flaw in GitHub’s internal protocol, any authenticated user could execute arbitrary commands on GitHub’s backend servers with a single git push command,” said Wiz researchers.
GitHub CVE-2026-3854 Explained
The vulnerability, CVE-2026-3854, allows any authenticated user to escalate privileges and execute arbitrary commands on GitHub’s backend systems.
This created the potential for unauthorized access to sensitive code repositories, internal configurations, and secrets.
Input Validation Failure
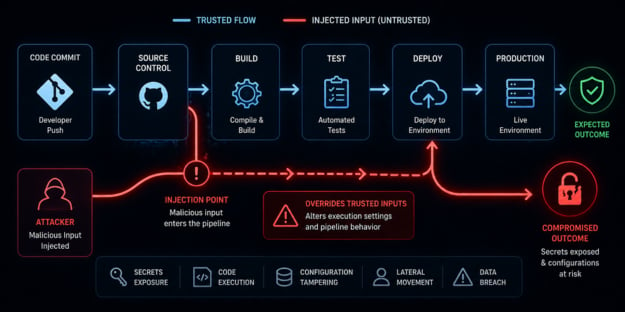
The flaw stems from an input validation failure within GitHub’s internal git protocol.
User-supplied git push options were embedded directly into an internal metadata structure known as the X-Stat header without proper sanitization.
Because this header relies on semicolon-delimited key-value pairs, an attacker could inject additional fields simply by including semicolons in their input.
Header Injection and Override
Compounding the issue, the system processes these fields using a “last-write-wins” parsing model.
This means that injected values appearing later in the header can override legitimate security controls defined earlier in the request.
By exploiting this behavior, attackers could manipulate critical settings, such as execution environments and hook configurations, ultimately enabling remote code execution.
The attack required no specialized tools, as a single crafted git push could trigger the full exploitation chain, making it easy to abuse.
Potential Impact
On GHES, successful exploitation could lead to complete server compromise, including full access to hosted repositories and internal data.
On GitHub[.]com, the risk extended further due to its multi-tenant architecture, where compromising a shared storage node could potentially expose repositories belonging to other users and organizations.
GitHub has since released patches for affected GHES versions, and there are no confirmed reports of active exploitation at the time of publication.
Hardening Self-Hosted GitHub
Securing self-hosted GitHub environments requires more than patching and should include a layered, proactive approach.
- Upgrade to the latest GHES version and test updates in a staging environment before deploying to production.
- Enforce least privilege by auditing user access, restricting permissions, and limiting the use of long-lived credentials.
- Monitor and log git activity by sending audit logs to a SIEM and alerting on unusual push options, hook execution, or other anomalous behavior.
- Harden configurations by restricting custom hooks, validating execution paths, and disabling unnecessary features.
- Strengthen input validation and internal trust boundaries to ensure all user-controlled data is sanitized across services.
- Segment and protect infrastructure by isolating GHES systems, limiting network access, and deploying endpoint detection on hosts.
- Test incident response plans with scenarios around software supply chain compromise.
These steps can help organizations build resilience against compromise while reducing overall exposure across your GitHub environment.
Implicit Trust in Microservices
CVE-2026-3854 highlights a common challenge in modern application security: managing complexity across interconnected services.
As organizations rely on microservices and internal APIs, implicit trust between components can introduce security risks if not properly controlled.
This is where adopting a zero trust approach can help reduce risk by eliminating implicit trust between services and continuously validating every interaction.