editorially independent. We may make money when you click on links
to our partners.
Learn More
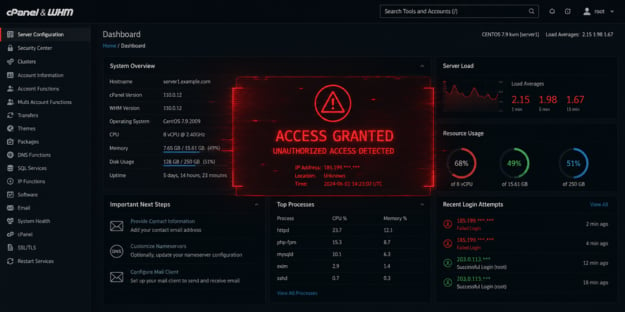
An authentication vulnerability in cPanel and Web Host Manager (WHM) is putting web hosting environments at risk, prompting the company to release an emergency patch and warn administrators to act quickly.
The flaw affects multiple authentication paths and could allow attackers to gain unauthorized access to servers if left unpatched.
“Let’s call this what it is: an unauthenticated authentication bypass in cPanel and WHM, a management-plane solution deployed on tens of thousands of servers and sitting in front of a meaningful chunk of the internet,” said Benjamin Harris, CEO and founder of watchTower in an email to eSecurityPlanet.
He added, “Once again, we’re running around with half the Internet seemingly ablaze, and given the increased usage of AI in vulnerability research, we anticipate this new normal to become increasingly familiar.”
Inside the cPanel Authentication Flaw
This cPanel vulnerability could enable full server takeover, as Web Host Manager’s (WHM) root-level access allows control over websites, databases, email systems, and configurations if compromised.
The issue affects all supported cPanel versions, expanding the attack surface and potentially impacting multiple customers in shared and enterprise hosting environments.
While full technical details have not been released, the flaw involves authentication mechanisms that may allow attackers to bypass login checks and gain unauthorized access.
Successful exploitation could grant administrative access to WHM, enabling configuration changes, account management, access to customer data, and deployment of malicious code or persistence mechanisms.
Security firm watchTower has released a detection tool to help identify vulnerable hosts.
cPanel has issued patches and there are already reports of exploitation in the wild.
Reducing Risk in cPanel Deployments
Securing cPanel and WHM environments requires a combination of patching and strong operational controls.
- Patch immediately by upgrading to the latest secure cPanel builds and forcing updates where necessary.
- Enforce strong access controls by enabling MFA, limiting root usage, and applying role-based access principles.
- Restrict administrative access by using IP allowlisting, firewall rules, and placing WHM behind a VPN or bastion host.
- Monitor and log authentication activity, alerting on failed login spikes, unusual access patterns, and other suspicious behavior.
- Harden systems by disabling unnecessary services, applying secure configurations, and deploying file integrity monitoring.
- Conduct proactive compromise assessments and ensure secure, tested backups are available for recovery.
- Test incident response plans with scenarios around control plane compromise.
Implementing these controls helps strengthen resilience while limiting the potential blast radius of a compromised hosting environment.
Risks of Centralized Admin Access
Attackers are increasingly focusing on administrative control planes that manage large portions of infrastructure.
Platforms like cPanel are attractive targets because a single compromise can impact hundreds or even thousands of downstream websites and customers.
This concentration of access amplifies risk, making strong authentication controls and segmentation important.
As a result, securing these management layers should be a priority for organizations operating shared or multi-tenant environments.
This is where a zero trust approach can help by reducing reliance on implicit trust and enforcing strict verification across administrative access points.