
A new iPhone exploit kit called DarkSword is being used in real-world attacks to fully compromise vulnerable devices and steal highly sensitive data, including messages, saved passwords, and cryptocurrency wallet information.
Researchers say the toolkit has spread beyond a single operator, appearing in campaigns linked to multiple threat actors and commercial surveillance customers across several countries.
DarkSword was analyzed in coordinated reports published today by Lookout, iVerify, and Google’s Threat Intelligence Group. The investigation began after researchers examining infrastructure tied to the earlier Coruna iOS exploit chain found a related domain, static.cdncounter[.]net, connected to compromised Ukrainian websites. Lookout and iVerify traced the activity to watering hole attacks in which legitimate Ukrainian sites, including a government domain, silently loaded a hidden iframe that delivered the exploit chain to visiting iPhones. Google said it had already been tracking the same framework since at least November 2025 and had observed it used in separate campaigns targeting users in Saudi Arabia, Turkey, Malaysia, and Ukraine.
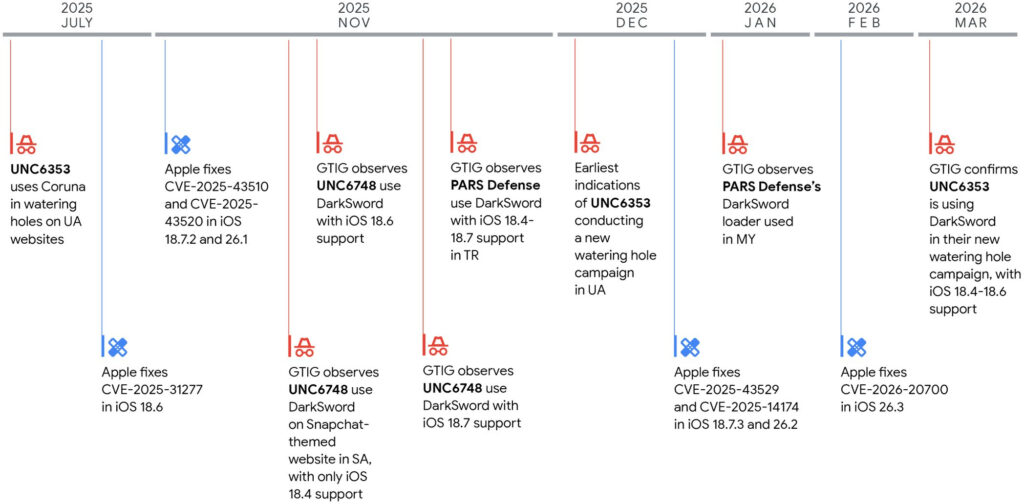
The affected platform is Apple’s iPhone, specifically devices running iOS 18.4 through 18.7, depending on the operator’s configuration. Apple had already patched the vulnerabilities used by DarkSword across a series of updates, culminating in full coverage by iOS 26.3, with additional fixes also landing in iOS 18.7.2 and 18.7.3. The three firms recommend updating immediately to iOS 18.7.6 or iOS 26.3.1, and enabling Lockdown Mode.
Six-flaw chain
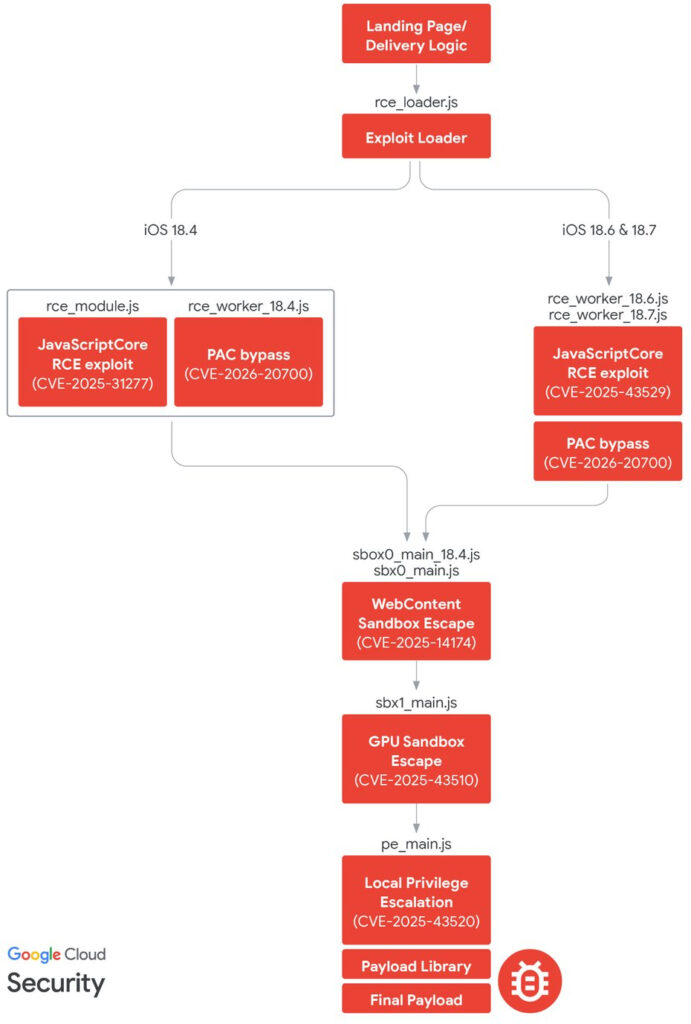
DarkSword is notable for being a full-chain iOS compromise framework written entirely in JavaScript. It leverages six vulnerabilities to escalate from Safari code execution to sandbox escape, then to privileged system processes, before gaining kernel-level access. The chain abuses flaws in JavaScriptCore, dyld, ANGLE, and the iOS kernel, allowing attackers to inject code into processes such as mediaplaybackd, configd, wifid, securityd, and UserEventAgent. From there, post-exploitation modules collect data and send it to attacker-controlled servers over HTTP or HTTPS.
The payloads seen after exploitation varied by operator. Google tracks three malware families tied to DarkSword, namely GHOSTBLADE, GHOSTKNIFE, and GHOSTSABER. In the Ukrainian watering hole activity attributed to UNC6353, a suspected Russian espionage cluster, the final payload was GHOSTBLADE, a rapid “grab-and-go” infostealer rather than a long-term surveillance implant. That malware harvested:
- SMS and iMessage databases
- Call logs
- Contacts
- Safari history and cookies
- Notes
- Calendars
- Health records
- Photos metadata
- iCloud Drive files
- Device identifiers
- Wi-Fi settings and passwords
- Mail indexes
- Installed app lists
- Telegram and WhatsApp data
- Keychain-related files
DarkSword also searches for wallet and exchange data associated with Coinbase, Binance, Kraken, KuCoin, OKX, MEXC, Ledger, Trezor, MetaMask, Exodus, Phantom, Uniswap, Gnosis Safe, and many others.
Researchers also found evidence that DarkSword has been adapted by different customers or operators. Google said the framework was used by the Saudi-focused cluster UNC6748 and by customers of Turkish surveillance vendor PARS Defense, each with modified delivery logic and different payloads. Some versions included encryption and better operational security, while others were strikingly sloppy, with hardcoded paths, debug logging, comments left in Russian and English, and weak cleanup routines.
iPhone users are advised to install the latest iOS updates and also consider enabling Lockdown Mode.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


