
Russia-linked threat actor APT28 has reactivated its advanced malware development team with a modern espionage toolkit that combines the BeardShell implant with a heavily customized version of the open-source Covenant framework.
APT28, also known as Fancy Bear and linked to Russia’s GRU Unit 26165, has conducted cyber-espionage operations since at least 2004 and is widely known for attacks targeting NATO and European governments.
ESET researchers traced the renewed activity to April 2024, when Ukraine’s national CERT (CERT-UA) discovered a keylogging implant, SlimAgent, on a compromised Ukrainian government system. Telemetry analysis and code comparisons revealed that SlimAgent is derived from the XAgent keylogging module, part of APT28’s flagship malware platform widely used during the 2010s. The tool captures keystrokes, screenshots, and clipboard data, and generates HTML-formatted logs that mirror the output format used by XAgent, reinforcing the lineage between the two toolsets.
Further investigation uncovered older samples dating back to 2018 that share nearly identical code structures with SlimAgent, including a distinctive six-stage data-collection loop and similar Windows API usage for logging foreground activity. Researchers concluded that these implants likely evolved from the same internal codebase, suggesting that APT28 developers maintained or repurposed legacy espionage components rather than building entirely new tools.
During the 2024 intrusion, investigators also identified the BeardShell implant operating alongside SlimAgent. BeardShell was previously documented by CERT-UA in mid-2025, where it was described as a PowerShell-based implant operating inside a .NET runtime and using legitimate cloud services as command-and-control (C2) infrastructure.
BeardShell communicates with operators via the Icedrive cloud storage service, executing PowerShell commands delivered through files stored in the attacker-controlled account. To maintain access, the malware developers reimplemented requests used by the official Icedrive client because the platform lacks a public API. APT28 developers frequently release updated builds when Icedrive changes its backend interface, restoring communications within hours.
Researchers also identified code artifacts linking BeardShell to the group’s earlier tooling. For example, the implant includes a rare opaque predicate obfuscation technique previously observed in Xtunnel, APT28’s network-pivoting tool used between 2013 and 2016. The reuse of this unusual mathematical construct strongly suggests continuity within the group’s internal development team.
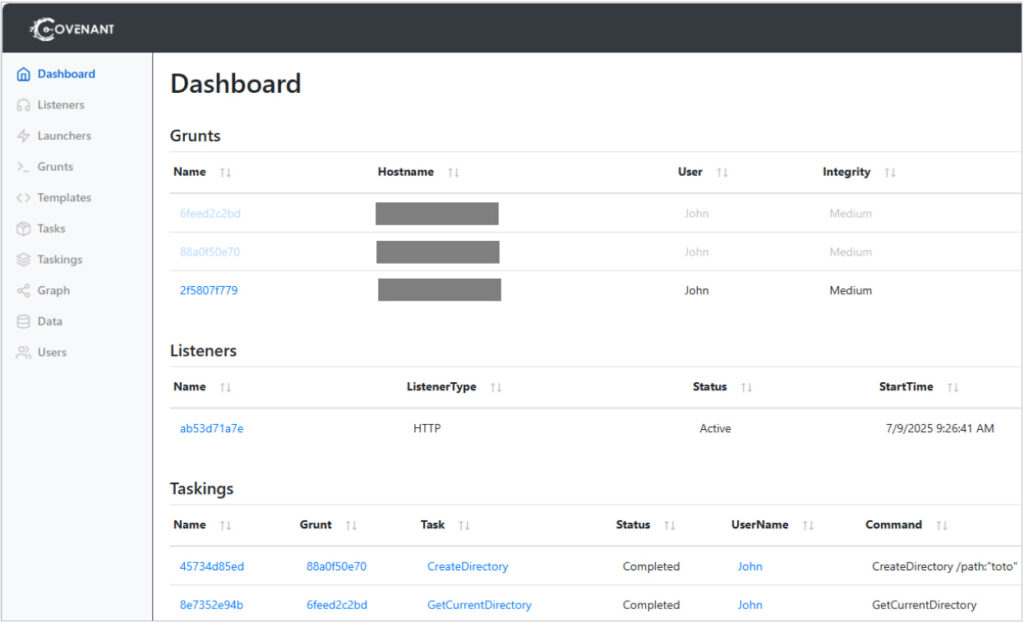
The most notable development, however, is APT28’s extensive modification of Covenant, an open-source .NET post-exploitation framework originally released in 2019. Rather than using the tool as-is, the attackers reworked major parts of its architecture to support long-term espionage operations.
ESET
Among the changes identified by researchers:
- Replacement of Covenant’s random implant identifiers with deterministic IDs derived from machine characteristics, enabling operators to track systems consistently across reboots.
- Adjustments to the framework’s two-stage execution flow to evade behavioral detection.
- Integration of cloud-based communication channels, implemented using the C2Bridge framework.
- Custom modules enabling C2 communications through services such as pCloud (2023), Koofr (2024–2025), and Filen (since July 2025).
In operational use, APT28 often deploys BeardShell and Covenant simultaneously, with each implant communicating through a different cloud provider. This redundancy allows attackers to quickly restore control if one infrastructure channel is disrupted.
Researchers say the reappearance of advanced custom tooling suggests APT28’s development team is once again actively producing high-end implants, possibly driven by intelligence priorities tied to the ongoing war in Ukraine.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


