A privilege escalation vulnerability in the IPVanish VPN macOS client could allow a local attacker to execute arbitrary code with root privileges without user interaction.
The issue stems from weaknesses in the app’s privileged helper component used when the OpenVPN protocol is enabled.
According to SecureLayer7 researchers who discovered it, the flaw allowed any unprivileged local process on a Mac with the IPVanish app installed to communicate with a privileged helper service and execute commands as root.
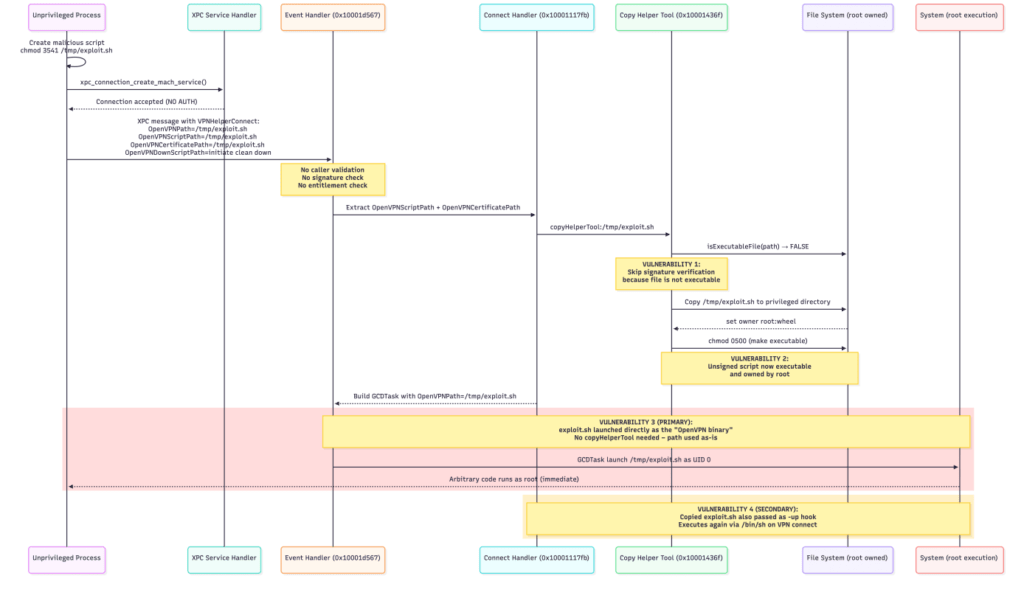
SecureLayer7 found that the helper service failed to authenticate processes that connected via macOS’ XPC interprocess communication mechanism. Because the service accepted connections from any local process without verifying its identity, an attacker could send crafted messages instructing the helper to perform privileged operations.
The researchers also identified additional weaknesses that made exploitation straightforward. One involved the OpenVPNPath parameter, which the helper used to launch the OpenVPN binary. The helper trusted this path directly from the incoming message and executed the file specified as the root, without verifying its location or code signature.
A second flaw existed in the helper’s file-copying routine. The component was designed to copy scripts and configuration files into a root-owned directory. However, the code only verified digital signatures for files that were already marked executable. By supplying a malicious script without the execute bit set, an attacker could bypass signature checks, have the file copied into the privileged directory, and then have the helper automatically make it executable.
Combined, these issues enabled a full privilege escalation chain. In a proof-of-concept exploit shared by SecureLayer7, a malicious script placed in /tmp/ipvanish_exploit.sh is executed as root by setting it as the OpenVPN binary path. The attack requires only local access and no user interaction once code execution as a standard user has been achieved.
IPVanish is a VPN provider offering encrypted internet connections, DNS leak protection, and kill-switch features for privacy-focused users. The macOS client relies on a privileged helper process to perform system-level tasks required for VPN networking operations.
The company acknowledged the issue and released a fix three days after the report, addressing the vulnerability in IPVanish for macOS versions 4.10.3 and 5.0.1 (beta users).
In a statement published on March 5, IPVanish said the vulnerability could only be exploited under limited circumstances. According to the company, a device would first need to be already compromised by malware or accessed physically, and the user would also need to have manually switched the VPN protocol from the default WireGuard to OpenVPN.
IPVanish stated the flaw was confined to the local system and did not affect the company’s VPN infrastructure, encryption, or user traffic. The company also said the updated macOS version changes the application flow so the helper no longer accepts data from locations that regular users can manipulate.
Users running the IPVanish macOS client are advised to update to version 4.10.3 or later immediately.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.