
A newly discovered malware campaign is quietly infiltrating US education and healthcare organizations using stealth techniques designed to blend malicious activity into normal internet traffic, according to new research from Cisco Talos.
The campaign, active since at least December 2025, deploys a previously undocumented backdoor dubbed “Dohdoor,” allowing attackers to maintain persistent access to compromised systems and potentially deliver additional malware payloads later in the intrusion chain. Researchers attribute the activity to a threat cluster tracked as UAT-10027, though definitive attribution to a specific nation-state group remains unclear.
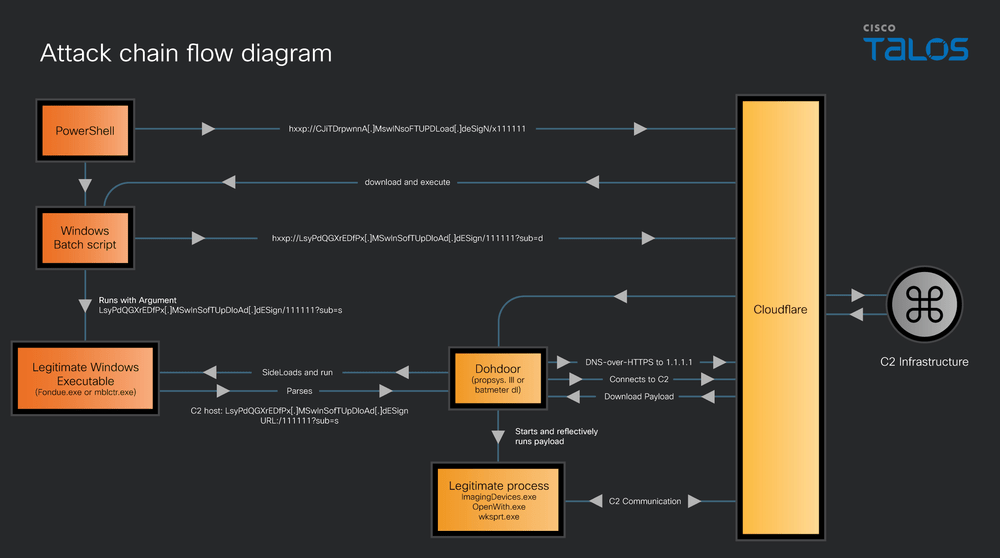
Unlike traditional malware that communicates with command servers through easily detectable channels, Dohdoor uses DNS-over-HTTPS (DoH), a legitimate privacy technology that encrypts DNS requests. By hiding malicious communications inside encrypted web traffic — often routed through reputable cloud infrastructure such as Cloudflare — attackers can evade many conventional network monitoring tools.
Cisco Talos researchers say the attacks primarily target organizations in the education and healthcare sectors in the United States, industries frequently selected by threat actors because of their large user bases, sensitive data holdings, and historically constrained cybersecurity resources.
The infection chain appears to rely on a multi-stage process that begins with malicious scripts, likely delivered through phishing or similar initial access techniques. Once executed, the attack downloads additional components and sideloads a malicious file that installs the Dohdoor backdoor. From there, attackers can remotely run commands, deploy further tools, or move deeper into a victim’s network.
Once active, Dohdoor can download and execute additional payloads directly in memory, a technique commonly used to avoid leaving forensic traces on disk. Analysts warn that such access could enable follow-on activity ranging from espionage to ransomware deployment, depending on the attackers’ objectives.
Although some signs resemble techniques previously linked to North Korean hacking groups, researchers say it is too early to make a firm attribution. What is clear, however, is that the attackers appear focused on quietly maintaining long-term access to targeted networks rather than carrying out quick, financially motivated attacks — underscoring the growing shift toward stealthier intrusions designed to remain undetected for extended periods.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


