
A new attack dubbed AirSnitch enables full machine-in-the-middle (MitM) capabilities on Wi-Fi networks where client isolation is enabled, affecting both home routers and enterprise deployments.
The research was conducted by researchers from the University of California, Riverside, and KU Leuven’s DistriNet group. The team presented their findings at the Network and Distributed System Security (NDSS) Symposium 2026 in San Diego.
A fundamental flaw
Client isolation is a vendor-implemented feature that blocks direct communication between Wi-Fi clients connected to the same access point. It is commonly recommended to prevent attacks such as ARP spoofing and ICMP redirect abuse. However, the researchers note that client isolation is not standardized in IEEE 802.11, leading to inconsistent, ad hoc implementations across vendors.
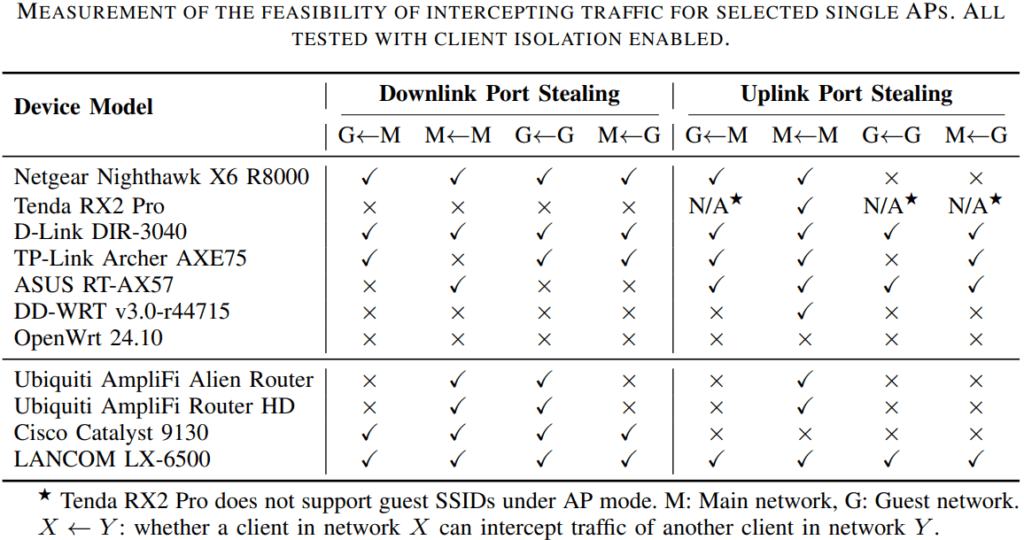
To evaluate its real-world robustness, the team tested five recent home routers from major vendors, two open-source router distributions (DD-WRT and OpenWrt), and several enterprise-grade devices. According to the paper, every tested router and network was vulnerable to at least one of the newly developed attacks.
The researchers also validated their findings in two live university networks, where they successfully demonstrated downlink traffic interception against their own test devices without impacting other users.
ndss-symposium.org
Breaking isolation at three layers
AirSnitch’s core insight is that client isolation is typically inconsistently enforced across three critical boundaries: encryption, routing, and internal switching.
Abusing shared Wi-Fi keys (GTK abuse)
Modern WPA2/WPA3 networks use a Group Temporal Key (GTK) to encrypt broadcast and multicast traffic. The researchers discovered that this shared key can be abused to inject malicious frames directly to victims, bypassing client isolation at the access point. By crafting broadcast frames encrypted with the GTK and spoofing the AP’s MAC address, an attacker can deliver unicast IP payloads to a victim device.
Even networks implementing Passpoint, an industry standard intended to secure public hotspots, are affected. The team found that group key management is incomplete, allowing attackers to obtain or manipulate group keys during certain handshake procedures and continue injecting traffic.
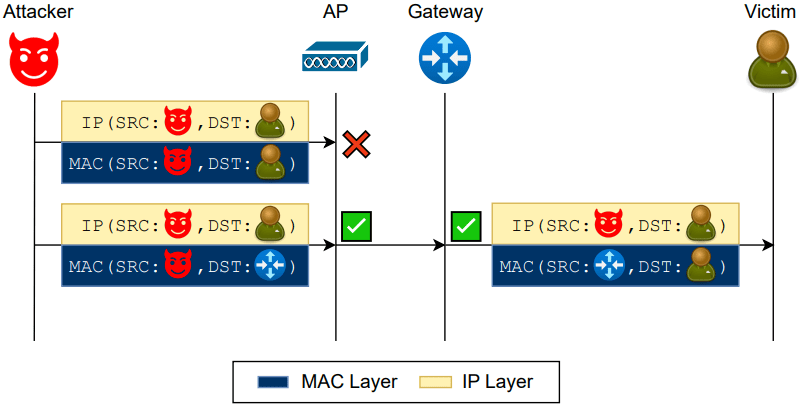
Gateway bouncing (routing-layer bypass)
Many routers enforce isolation only at Layer 2 (MAC layer) but fail to extend it to Layer 3 (IP routing). In what the researchers call a “gateway bouncing” attack, a malicious client sends packets to the network’s gateway MAC address but uses the victim’s IP as the destination. The gateway accepts and relays the packet back to the victim, effectively bypassing isolation controls.
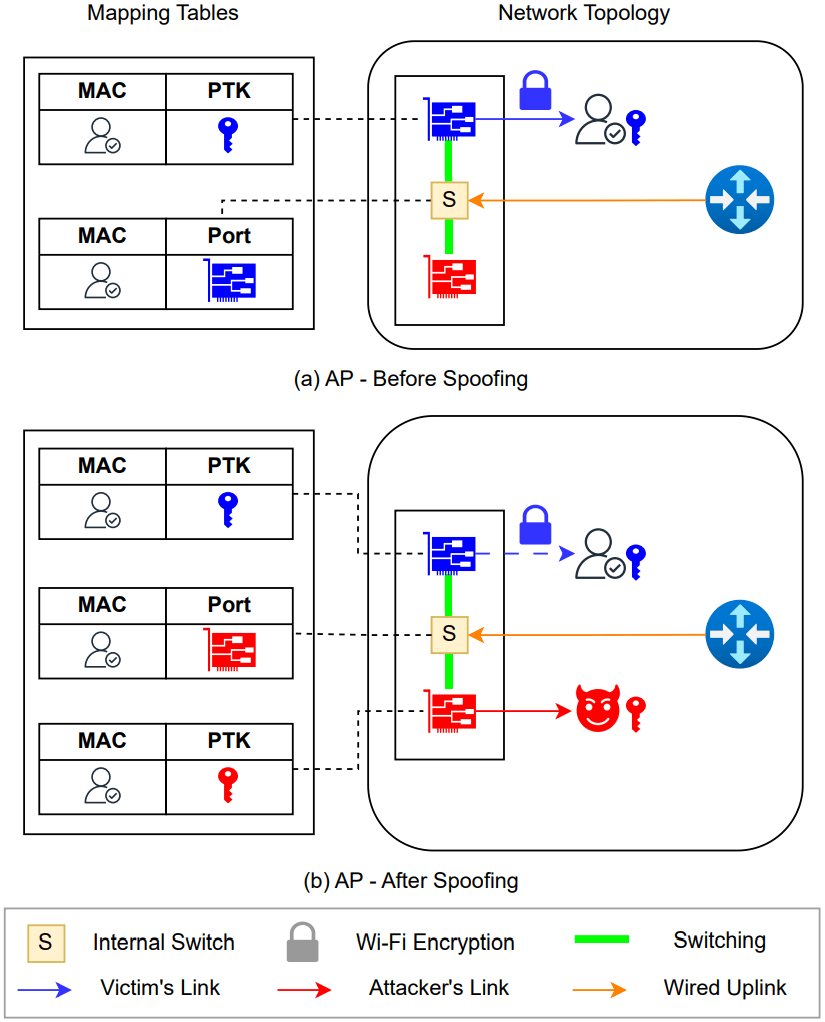
Port stealing (switching-layer interception)
Perhaps the most severe finding involves repurposing a classic Ethernet “port stealing” attack in Wi-Fi environments. By spoofing a victim’s MAC address and associating with a different BSSID (e.g., another frequency band or guest network), the attacker can trick the access point’s internal switching logic into rebinding the victim’s MAC address to the attacker’s port.
As a result, traffic destined for the victim is encrypted using the attacker’s negotiated session key (PTK) and delivered to the attacker instead. In some configurations, traffic protected by WPA2/WPA3 was even observed leaking in plaintext when redirected through an open SSID.
ndss-symposium.org
Full machine-in-the-middle
By chaining injection and interception primitives, the researchers demonstrated full bidirectional MitM attacks in enterprise-style deployments, including multi-AP networks. WPA2/WPA3-Enterprise networks, long considered resistant to insider interception due to per-client credentials, were also affected.
In enterprise testbeds, attackers were able to intercept RADIUS authentication traffic between access points and backend authentication servers. By brute-forcing weak RADIUS shared secrets, they escalated the attack to credential interception via rogue access points.
The team’s broader conclusion is that Wi-Fi encryption protocols fail to strongly bind together a client’s MAC address, IP address, session keys, and physical association point. This weak layer synchronization creates exploitable gaps that client isolation does not adequately close.
Widespread impact
Tested devices included models from Netgear, TP-Link, D-Link, ASUS, Tenda, Ubiquiti, Cisco, and LANCOM, as well as firmware from DD-WRT and OpenWrt. Vulnerabilities varied by configuration, but isolation bypasses were consistently possible through one or more techniques.
The findings indicate that the problem is architectural rather than vendor-specific, stemming from design assumptions in WPA2/WPA3 and non-standardized isolation policies.
Mitigations
The researchers propose stronger binding between cryptographic keys and network-layer identities, improved group key management, and clearer isolation domains across BSSIDs and distribution systems. However, meaningful fixes will likely require coordinated changes in standards and firmware implementations.
In the meantime, administrators can reduce exposure by:
- Avoiding shared-password (WPA2/3-Personal) networks in sensitive environments.
- Using WPA3-Enterprise with properly secured RADIUS configurations and strong shared secrets.
- Segmenting guest and internal networks onto separate VLANs and, where possible, on separate physical infrastructure.
- Monitoring for duplicate MAC associations and anomalous re-authentication events.
- Keeping AP firmware up to date and turning off unused SSIDs or frequency bands.
Because AirSnitch operates as an insider attack, exploitation requires an attacker to join the network, either as a guest user or with legitimate credentials. However, in public hotspots, university campuses, hotels, and enterprise guest networks, that bar is often very low.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


