editorially independent. We may make money when you click on links
to our partners.
Learn More
Microsoft has released a security update to address a vulnerability in the .NET platform that could allow attackers to remotely crash affected applications.
The flaw enables unauthenticated attackers to trigger a Denial-of-Service (DoS) condition, potentially causing applications or services running on vulnerable .NET environments to become unavailable.
Exploitation of the vulnerability “… allows an unauthorized attacker to deny service over a network,” said NIST in its advisory.
Understanding the .NET DoS Vulnerability
The vulnerability, tracked as CVE-2026-26127, affects multiple versions of the .NET framework and poses a risk to organizations that rely on .NET-based web applications, APIs, and backend services.
Because the flaw can be exploited remotely without authentication or user interaction, internet-facing applications running vulnerable versions of the framework may be particularly exposed.
Microsoft assigned the vulnerability a CVSS score of 7.5.
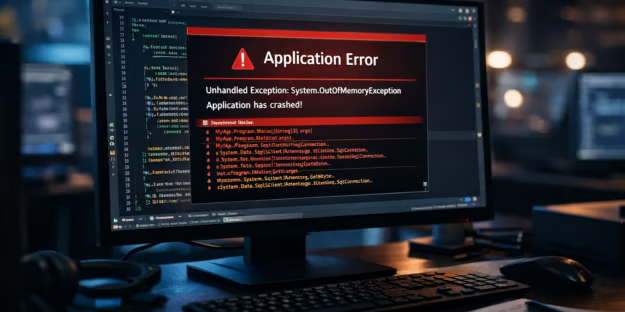
The issue stems from an out-of-bounds read vulnerability, a type of memory-handling flaw that occurs when software attempts to read data outside the boundaries of an allocated memory buffer.
When this happens, the application may access unintended memory locations, potentially causing instability, unexpected behavior, or application crashes.
In this case, an attacker can exploit the weakness by sending a specially crafted network request to a vulnerable .NET application.
If the malformed request triggers the out-of-bounds memory read, it can cause the application to crash — effectively resulting in a Denial-of-Service (DoS) condition that prevents legitimate users from accessing the service.
Microsoft has released a patch and there are no reports of exploitation in the wild at the time of publication.
How Organizations Can Reduce .NET DoS Risk
Organizations running .NET environments should apply the patch and implement additional security controls to reduce the risk of service disruption.
- Upgrade .NET environments and related dependencies (such as Microsoft.Bcl.Memory) to the latest patched versions.
- Use DevSecOps tools to scan for vulnerable dependencies to prevent outdated components from being redeployed.
- Monitor application logs and network traffic for unexpected crashes, malformed requests, or unusual activity that could indicate a denial-of-service attempt.
- Reduce the attack surface by restricting internet exposure of .NET services and implementing network segmentation or reverse proxies where possible.
- Implement web application firewall protections, rate limiting, and request throttling to block malformed or excessive requests that could trigger application crashes.
- Strengthen application resilience and availability controls, such as automatic restarts, health checks, and failover mechanisms to minimize service disruption.
- Test incident response plans and business continuity plans for scenarios around DoS incidents.
Collectively, these measures help organizations limit blast radius and build resilience.
Why Framework Vulnerabilities Matter for Enterprise Security
The disclosure of CVE-2026-26127 highlights a persistent challenge in modern software ecosystems: vulnerabilities in widely used development frameworks can have far-reaching impacts across many applications and environments.
Frameworks such as Microsoft .NET underpin a wide range of enterprise services, including cloud-native applications, web services, internal APIs, and backend business systems.
As vulnerabilities in foundational platforms continue to expose large portions of enterprise infrastructure, organizations are turning to zero trust solutions to help reduce attack surfaces.