
LastPass has warned customers about an ongoing phishing campaign that impersonates the company using fake email threads designed to trick recipients into revealing their credentials.
The company says the activity began around March 1, 2026, and notes that its own systems were not compromised.
LastPass is a widely used password manager that allows individuals and organizations to securely store and manage login credentials in encrypted vaults. The service integrates with browsers, mobile devices, and enterprise identity systems, making it a common target for phishing campaigns seeking to capture access credentials to multiple online accounts at once.
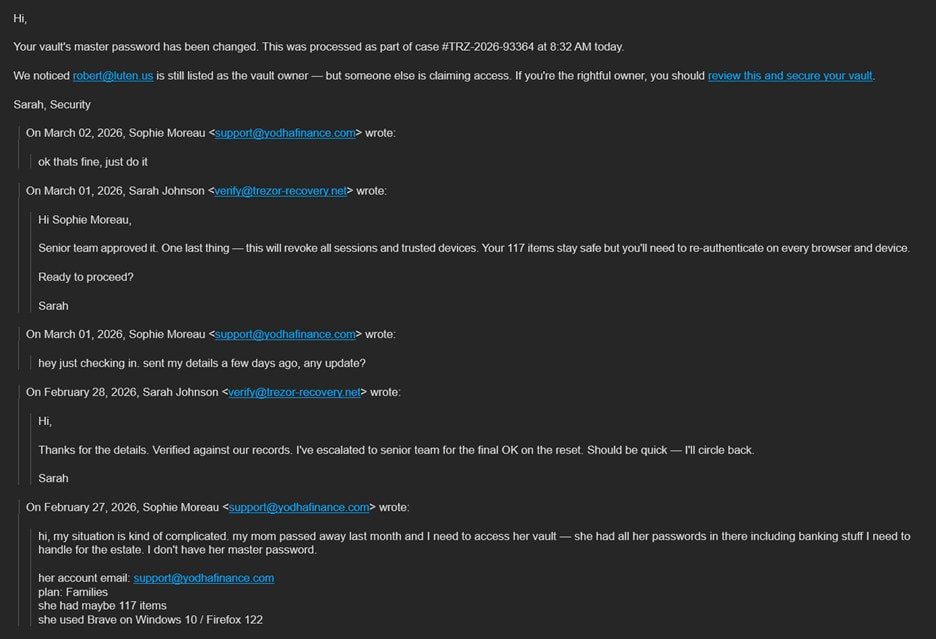
According to LastPass, attackers are distributing phishing emails that appear to be part of legitimate internal email conversations discussing suspicious activity on a user’s account. The goal is to create urgency and prompt victims to click on malicious links that lead to credential-harvesting pages.
The threat actors send messages with subject lines such as “Re: pending approval,” “Fwd: Re: your request,” “Re: Access request pending,” and “Re: credential download.” The emails are crafted to look like forwarded messages discussing actions allegedly taken on the recipient’s LastPass account, including:
- Vault export attempts
- Full account recovery requests
- Registration of a new trusted device
- Credential downloads
By presenting these events as suspicious or unauthorized, the attackers attempt to trigger an alarm and prompt the recipient to follow instructions in the message.
LastPass
The attackers also employ display name spoofing, a technique that manipulates the sender name to appear as if the email originated from LastPass. Many email clients, particularly on mobile devices, display only the sender’s name while hiding the underlying email address, which can allow malicious senders to impersonate trusted brands more easily.
Fake LastPass login pages
Victims who click the links in these messages are redirected through several intermediary URLs before landing on a phishing domain, verify-lastpass[.]com, which hosts a fake LastPass single sign-on (SSO) login page. The attackers generate numerous variations of the link by appending different numbers to the login path, enabling them to produce large numbers of unique URLs that all point to the same credential-harvesting site.
Examples of infrastructure used in the campaign include redirect links delivered through SendGrid tracking domains and compromised or unrelated domains such as: hancochem[.]at, atomicminerals[.]ca, redlakegold[.]ca, bedfordmetals[.]com, and 79resources[.]com.
LastPass noted that the malicious messages originate from unrelated sender addresses such as office@hancochem.at, support@yodhafinance.com, and info@itpbusa.com.
Mitigation advice
LastPass says it is working with third-party partners to have the phishing domains removed and encourages users to remain cautious when receiving account-related emails.
Users are advised not to click links in unsolicited emails claiming to report suspicious account activity, and to verify the sender address, not just the display name. LastPass should only be accessed directly through the official website or the browser extension, rather than via email links. Finally, users should never share their master password and should keep in mind that LastPass employees will never ask for it.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


