In 2025, the financial cyberthreat landscape continued to evolve. While traditional PC banking malware declined in relative prevalence, this shift was offset by the rapid growth of credential theft by infostealers. Attackers increasingly relied on aggregation and reuse of stolen data, rather than developing entirely new malware capabilities.
To describe the financial threat landscape in 2025, we analyzed anonymized data on malicious activities detected on the devices of Kaspersky security product users and consensually provided to us through the Kaspersky Security Network (KSN), along with publicly available data and data on the dark web.
We analyzed the data for
- financial phishing,
- banking malware,
- infostealers and the dark web.
Key findings
Phishing
Phishing activity in 2025 shifted toward e-commerce (14.17%) and digital services (16.15%), with attackers increasingly tailoring campaigns to regional trends and user behavior, making social engineering more targeted despite reduced focus on traditional banking lures.
Banking malware
Financial PC malware declined in prevalence but remained a persistent threat, with established families continuing to operate, while attackers increasingly prioritize credential access and indirect fraud over deploying complex banking Trojans. To the contrary, mobile banking malware continues growing, as we wrote in detail in our mobile malware report.
Infostealers and the dark web
Infostealers became a central driver of financial cybercrime, fueling a growing dark web economy where stolen credentials, payment data, and full identity profiles are traded at scale, enabling widespread and destructive fraud operations.
Financial phishing
In 2025, online fraudsters continued to lure users to phishing and scam pages that mimicked the websites of popular brands and financial organizations. Attackers leveraged increasingly convincing social engineering techniques and brand impersonation to exploit user trust. Rather than relying solely on volume, campaigns showed greater targeting and contextual adaptation, reflecting a maturation of phishing operations.
The distribution of top phishing categories in 2025 shows a clear shift toward digital platforms that aggregate multiple user activities, with web services (16.15%), online games (14.58%), and online stores (14.17%) leading globally. Compared to 2024, the rise of online games and the decline of social networks and banks indicate that attackers are increasingly targeting environments where users are more likely to take a risk or engage impulsively. Categories such as instant messaging apps and global internet portals remain significant phishing targets, reflecting their role as communication and access hubs that can be exploited for credential harvesting.
TOP 10 categories of organizations mimicked by phishing and scam pages that were blocked on home users’ devices, 2025 (download)
Regional patterns further reinforce the adaptive nature of phishing campaigns, showing that attackers closely align category targeting with local digital habits. For example, online stores dominate heavily in the Middle East.
TOP 10 categories of organizations mimicked by phishing and scam pages that were blocked on home users’ devices in the Middle East, 2025 (download)
Online games and instant messaging platforms feature more prominently in the CIS, suggesting a focus on younger or highly connected user bases.
TOP 10 categories of organizations mimicked by phishing and scam pages that were blocked on home users’ devices in the CIS, 2025 (download)
APAC demonstrates almost equal shares of online games and banks which signifies a combined approach targeting different users.
TOP 10 categories of organizations mimicked by phishing and scam pages that were blocked on home users’ devices in APAC, 2025 (download)
In Africa, a stronger emphasis on banks reflects the continued importance of traditional financial services. Most likely, this is due to the lower security level of the financial institutions in the region.
TOP 10 categories of organizations mimicked by phishing and scam pages that were blocked on home users’ devices in Africa, 2025 (download)
Whereas in LATAM, delivery companies appearing in the top categories indicate attackers exploiting the growth of e-commerce logistics.
TOP 10 categories of organizations mimicked by phishing and scam pages that were blocked on home users’ devices in Latin America, 2025 (download)
Europe presents a more balanced distribution across categories, pointing to diversified attack strategies.
TOP 10 categories of organizations mimicked by phishing and scam pages that were blocked on home users’ devices in Europe, 2025 (download)
Attackers actively localize their tactics to maximize relevance and effectiveness.
The distribution of financial phishing pages by category in 2025 reveals strong regional asymmetries that reflect both user behavior and attacker prioritization.
Globally, online stores dominated (48.45%), followed by banks (26.05%) and payment systems (25.50%). The decline in bank phishing may suggest that these services are becoming increasingly difficult to successfully impersonate, so fraudsters are turning to easier ways to access users’ finances.
However, this balance shifts significantly at the regional level.
In the Middle East, phishing is overwhelmingly concentrated on e-commerce (85.8%), indicating a heavy reliance on online retail lures, whereas in Africa, bank-related phishing leads (53.75%), which may indicate that user account security there is still insufficient. LATAM shows a more balanced distribution but with a higher share of online store targeting (46.30%), while APAC and Europe display a more even spread across all three categories, pointing to diversified attack strategies. These variations suggest that attackers are not operating uniformly but are instead adapting campaigns to regional digital habits, payment ecosystems, and trust patterns – maximizing effectiveness by aligning phishing content with the most commonly used financial services in each market.
Distribution of financial phishing pages by category and region, 2025 (download)
Online shopping scams
The distribution of organizations mimicked by phishing and scam pages in 2025 highlights a clear shift toward globally recognized digital service and e-commerce brands, with attackers prioritizing platforms that have large, active user bases and frequent payment interactions.
Netflix (28.42%) solidified its ranking as the most impersonated brand, followed by Apple (20.55%), Spotify (18.09%), and Amazon (17.85%). This reflects a move away from traditional retail-only targets toward subscription-based and ecosystem-driven services.
TOP 10 online shopping brands mimicked by phishing and scam pages, 2025 (download)
Regionally, this trend varies: Netflix dominates heavily in the Middle East, Apple leads in APAC, while Spotify ranks first across Europe, LATAM, and Africa. Although most of the top platforms are highly popular across different regions, we may suggest that the attackers tailor brand impersonation to regional popularity and user engagement.
Payment system phishing
Phishing campaigns are impersonating multiple payment ecosystems to maximize coverage. While PayPal was the most mimicked in 2024 with 37.53%, its share dropped to 14.10% in 2025. Mastercard, on the contrary, attracted cybercriminals’ attention, its share increasing from 30.54% to 33.45%, while Visa accounted for a significant 20.06% (last year, it wasn’t in the TOP 5), reinforcing the growing focus on widely used banking card networks. The continued presence of American Express (3.87%) and the increasing number of pages mimicking PayPay (11.72%) further highlight attacker experimentation and regional adaptation.
TOP 5 payment systems mimicked by phishing and scam pages, 2025 (download)
Financial malware
In 2025, the decline in users affected by financial PC malware continued. On the one hand, people continue to rely on mobile devices to manage their finances. On the other hand, some of the most prominent malware families that were initially designed as bankers had not used this functionality for years, so we excluded them from these statistics.
Changes in the number of unique users attacked by banking malware, by month, 2023–2025 (download)
Windows systems remained the primary platform targeted by attackers with financial malware. According to Kaspersky Security Bulletin, overall detections included 1,338,357 banking Trojan attacks globally from November 2024 to October 2025, though this number is also declining due to increasing focus on mobile vectors. Desktop threats continued to be distributed via traditional delivery methods like malicious emails, compromised websites, and droppers.
In 2025, Brazilian-origin families such as Grandoreiro (part of the Tetrade group) stood out for their constant activity and global reach. Despite a major law enforcement disruption in early 2024, Grandoreiro remained active in 2025, re-emerging with updated variants and continuing to operate. Other notable actors included Coyote and emerging families like Maverick, which abused WhatsApp for distribution while maintaining fileless techniques and overlaps with established Brazilian banking malware to steal credentials and enable fraudulent transactions on desktop banking platforms. Besides traditional bankers, other Brazilian malware families are worth mentioning, which specifically target relatively new and highly popular regional payment systems. One of the most prominent threats among these is GoPix Trojan focusing on the users of Brazilian Pix payment system. It is also capable of targeting local Boleto payment method, as well as stealing cryptocurrency.
There was also a surge in incidents in 2025 in which fraudsters targeted organizations through electronic document management (EDM) systems, for example, by substituting invoice details to trick victims into transferring funds. The Pure Trojan was most frequently encountered in such attacks. Attackers typically distribute it through targeted emails, using abbreviations of document names, software titles, or other accounting-related keywords in the headers of attached files. Globally in the corporate segment, Pure was detected 896 633 times over 2025, with over 64 thousand users attacked.
Contrary to PC banking malware, mobile banker attacks grew by 1.5 times in 2025 compared to the previous reporting period, which is consistent with their growth in 2024. They also saw a sharp surge in the number of unique installation packages. More statistics and trends on mobile banking malware can be found in our yearly mobile threat report.
Complementing traditional financial malware, infostealers played a significant role in enabling financial crime both on PCs and mobile devices by harvesting credentials, cookies, and autofill data from browsers and applications, which attackers then used for account takeovers or direct banking fraud. Kaspersky analyses pointed to a surge in infostealer detections (up by 59% globally on PCs), fueling credential-based attacks.
Financial cyberthreats on the dark web
The Kaspersky Digital Footprint Intelligence (DFI) team closely monitors infostealer activity on both PC and mobile devices to analyze emerging trends and assess the evolving tactics of cybercriminals.
Fraudsters especially target financial data such as payment cards, cryptocurrency wallets, login credentials and cookies for banking services, as well as documents stored on the victim’s device. The stolen data is collected in log files and shared on dark web resources, where they are bought, sold, or distributed freely and then used for financial fraud.
With access to financial data, fraudsters can gain control of users’ bank accounts and payment cards, and withdraw funds. Compromised accounts and cards are also frequently used in subsequent activities, turning the victims into intermediaries in a fraud scheme.
Compromised accounts
Kaspersky DFI found that in 2025, over one million online banking accounts (these are not Kaspersky product users) served by the world’s 100 largest banks fell victim to infostealers: their credentials were being freely shared on the dark web.
The countries with the highest median number of compromised accounts per bank were India, Spain, and Brazil.
The chart below shows the median number of compromised accounts per bank for the TOP 10 countries.
TOP 10 countries with the highest compromised account median (download)
Compromised payment cards
Seventy-four percent of payment cards that were compromised by infostealer malware, published on dark web resources and identified by the Digital Footprint Intelligence team in 2025, remained valid as of March 2026. This means that attackers could still use the cards that had been stolen months or even years prior.
It should be noted that the number of bank accounts and payment cards known to have been compromised by infostealers in 2025 will continue to rise, because fraudsters do not publish the log files immediately after the compromise but only after a delay of months or even years.
Data breaches
Regardless of the industry in which the target company operates, data breaches often expose users’ financial data, including payment card information, bank account details, transaction histories and other financial information. As a consequence, the compromised databases are sold and distributed on underground resources.
It should be noted that the threat is not limited to the exposure of financial information alone. Various identity documents and even seemingly public data, such as names, phone numbers and email addresses, can become a risk when they are published on the dark web. Such data attracts fraudsters’ attention and can be used in social engineering attacks to gain access to the user’s financial assets.
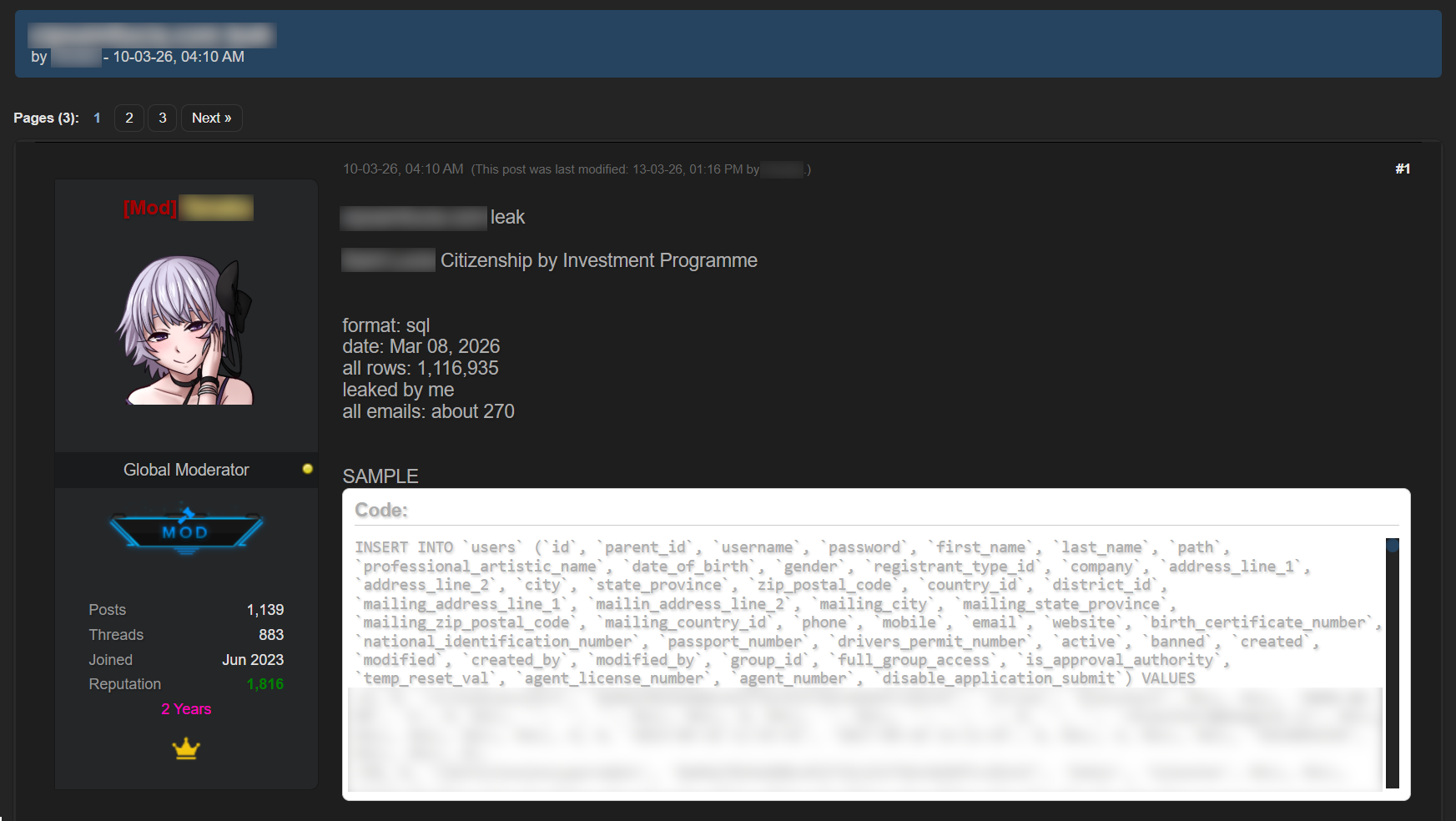
An example of a post offering a database
Sale of bank accounts and payment cards
The dark web often features services provided by stores that specialize in selling bank accounts and payment cards. Fraudsters typically obtain data for sale from a variety of sources, including infostealer logs and leaked databases, which are first repackaged and then combined.
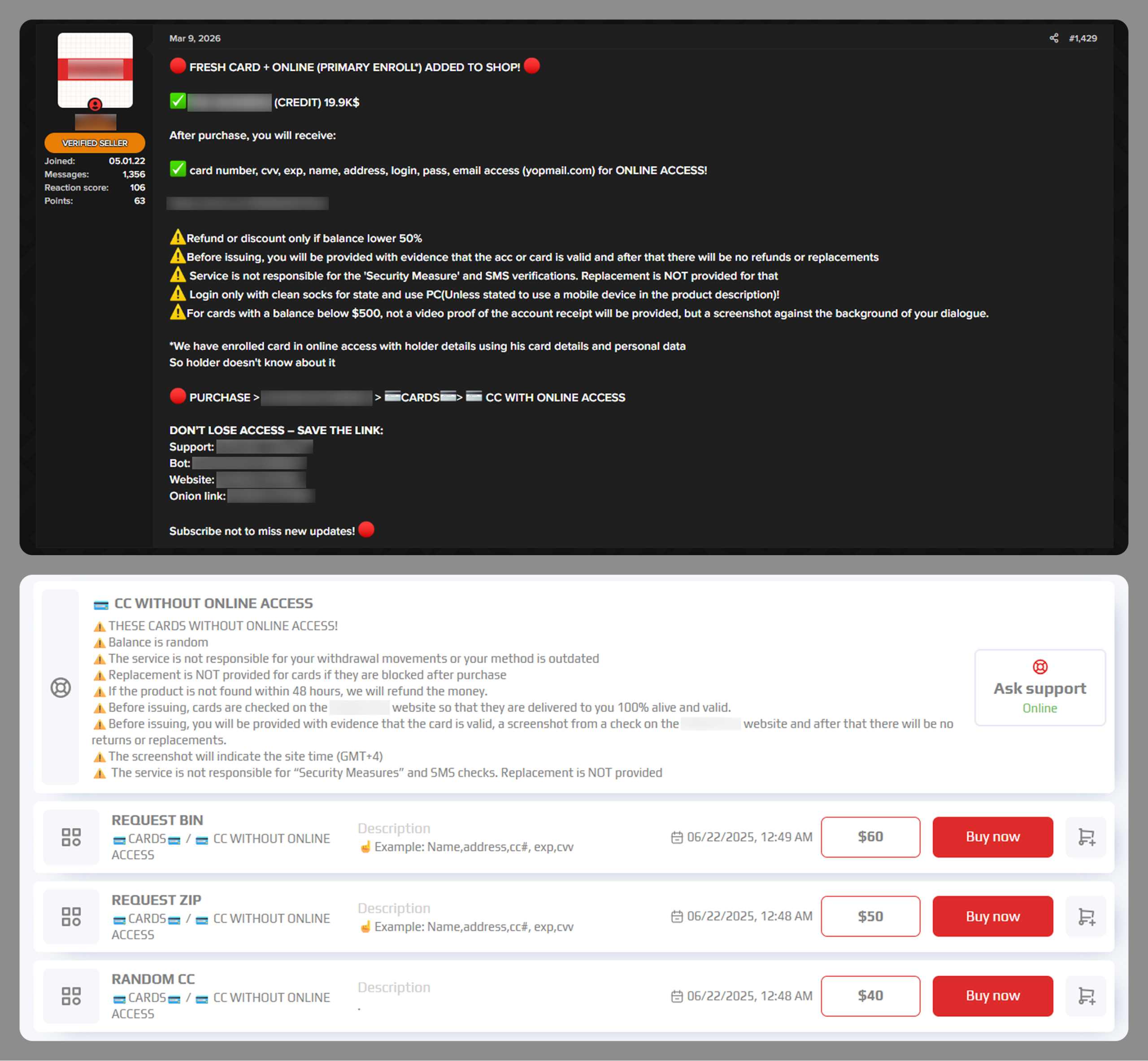
Examples of a post (top) and a site (bottom) offering payment cards
Often, sellers offer complete victim profiles, referred to by fraudsters as “fullz”. These include not only bank accounts or payment cards but also identification documents, dates of birth, residential addresses, and other personal details. A full‑information package is usually more expensive than a payment card or a bank account alone.
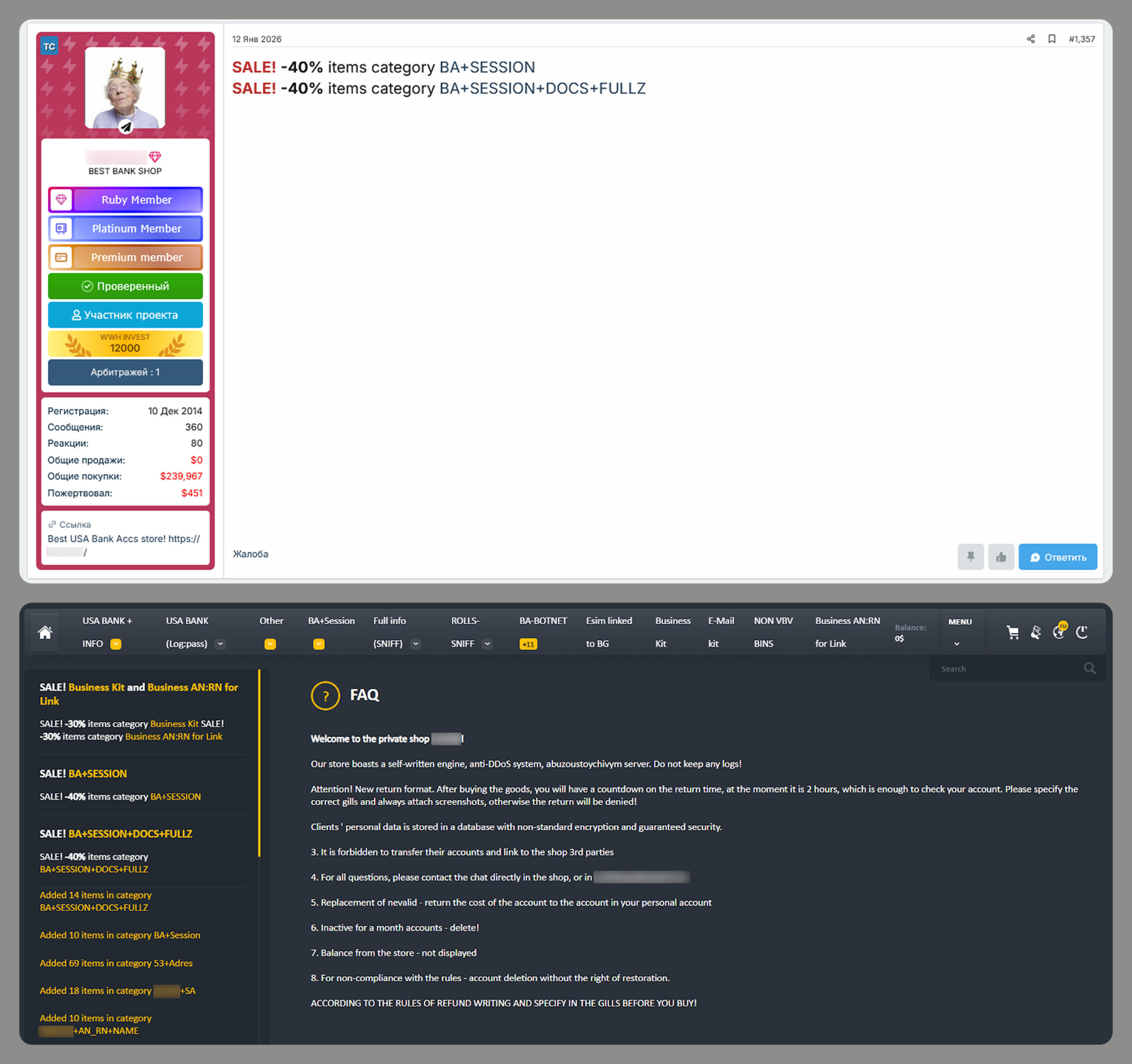
Examples of a post (top) and a site (bottom) offering bank accounts
Compiled databases
Fraudsters exploit various sources, including previously leaked databases, to compile new, thematic ones. Finance- and, in particular, cryptocurrency-related databases, are among the most popular. Compilations aimed at specific user groups, such as the elderly or wealthy people, are also of interest to cybercriminals.
Usually, thematic databases contain personal information about users, such as names, phone numbers, and email addresses. Fraudsters can use this data to launch social engineering attacks.
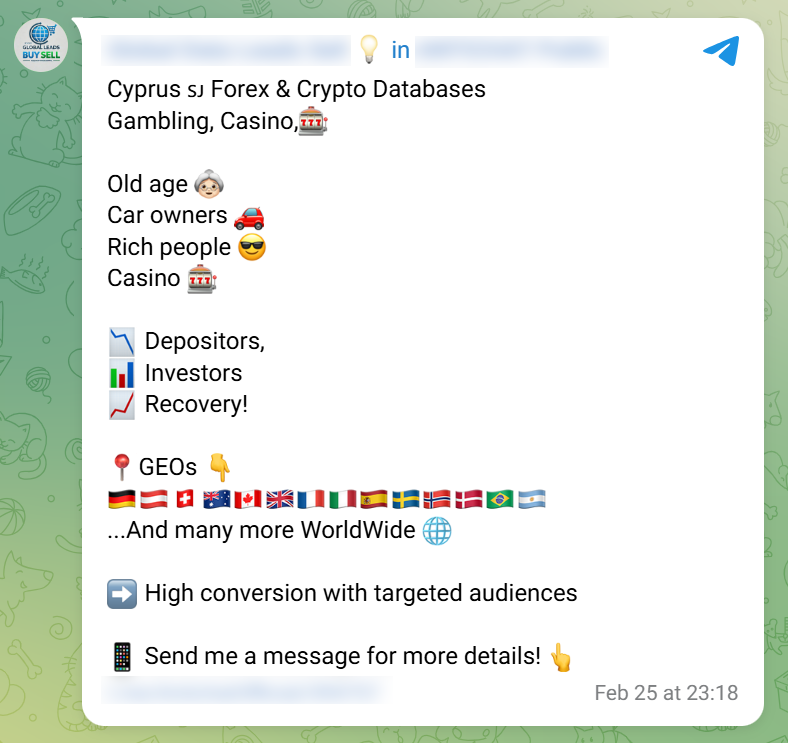
An example of a message offering compiled databases
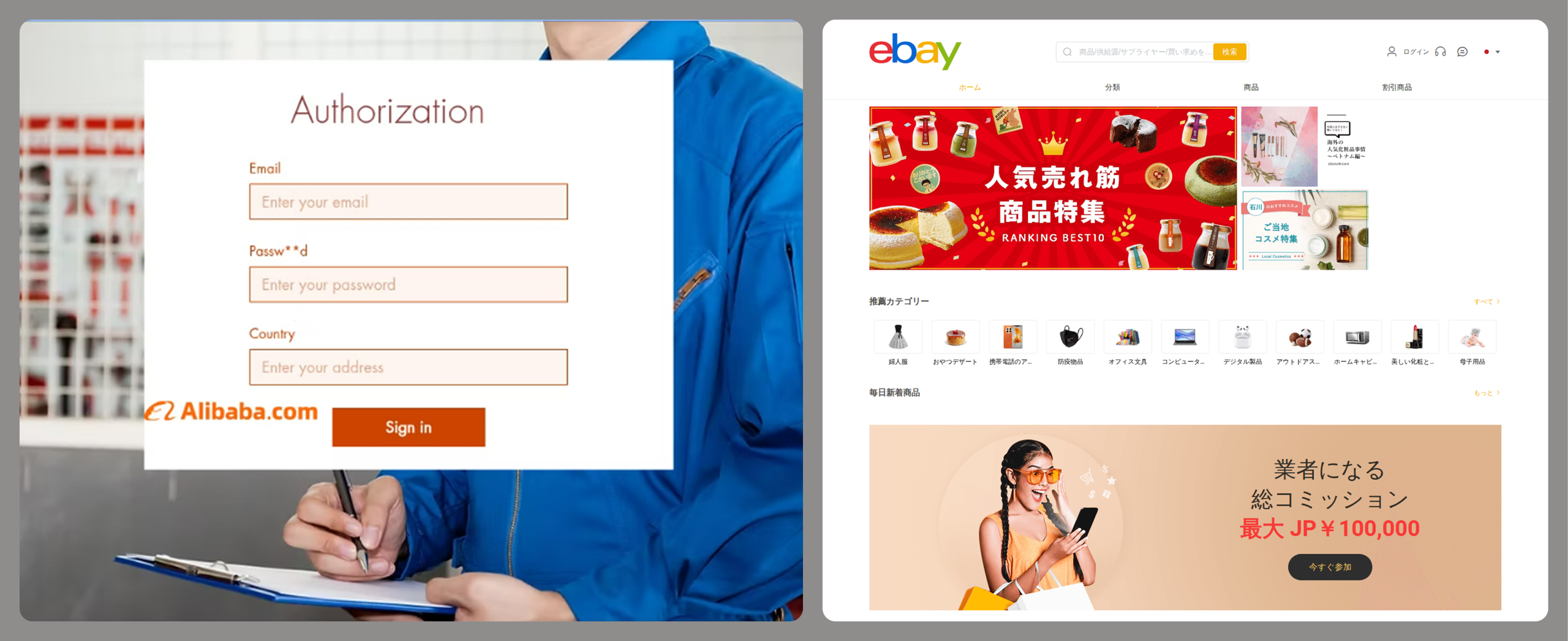
Creation of phishing websites
Phishing websites have become a powerful tool for the financial enrichment of fraudsters. Cybercriminals create fraudulent sites that masquerade as legitimate resources of companies operating in various industries. Gambling and retail sites remain among the most popular targets.
In order to obtain personal and financial information from unsuspecting users, adversaries seek out ways to create such phishing websites. Ready-made layouts and website copies are sold on the dark web and advertised as profitable tools. Moreover, fraudsters offer phishing website creation services.
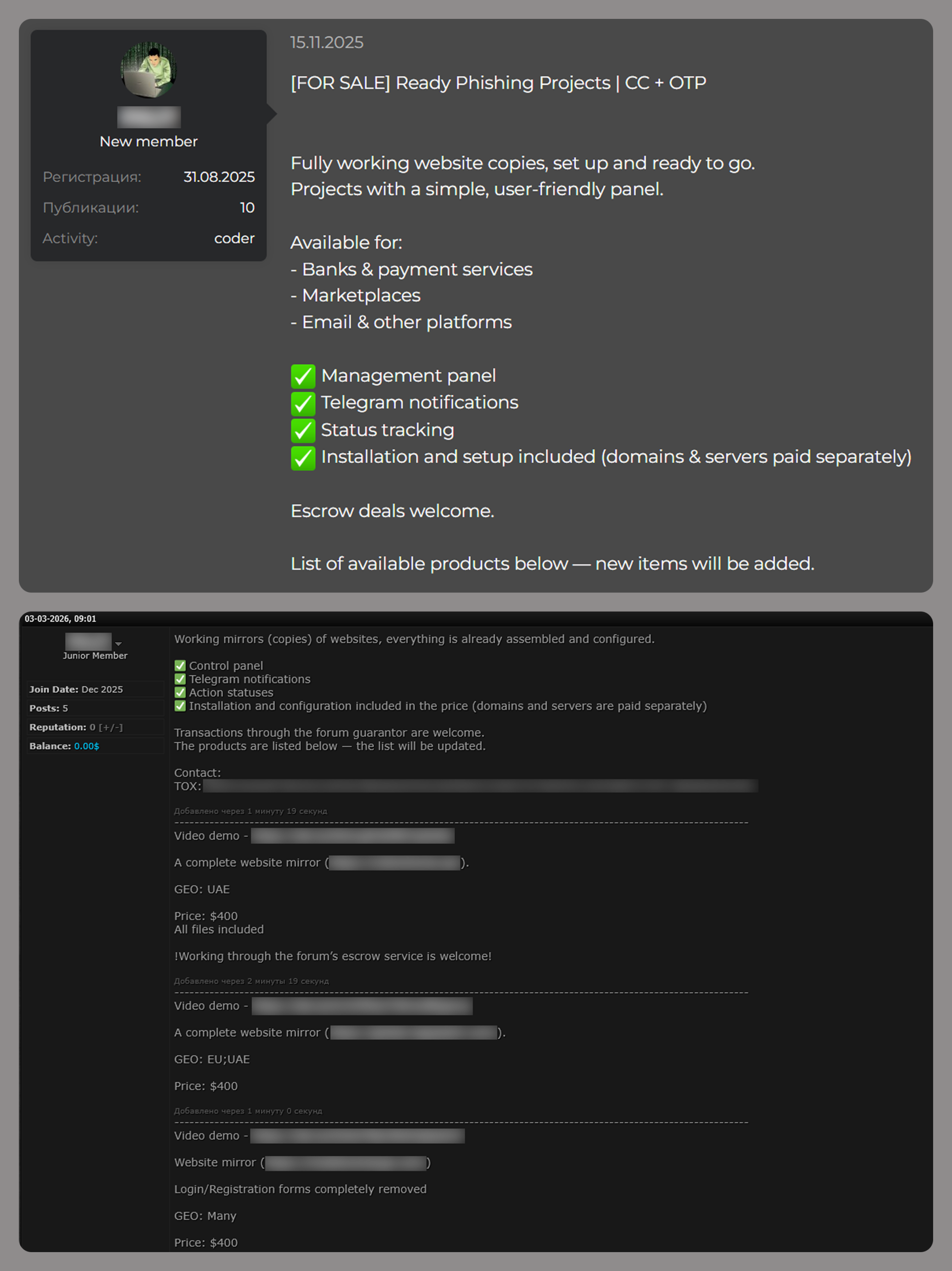
Examples of posts offering creation of phishing websites
Conclusion
The decline of traditional PC banking malware is not an indicator of reduced risk; rather, it highlights a redistribution of attacker effort toward more efficient methods targeting mobile devices, credential theft, and social engineering. Infostealers, in particular, are a force multiplier, enabling widespread compromise at scale.
Looking ahead to 2026, the financial threat landscape is expected to become even more data-driven and automated. Organizations must adapt by focusing on identity protection, real-time monitoring, and cross-channel threat intelligence, while users must remain vigilant against increasingly sophisticated and personalized attack techniques.

