Phone-based fraud never went away. It evolved.
Vishing, or voice phishing, is a social engineering technique that uses phone calls to extract money or sensitive information from victims. A few years ago, these attacks typically arrived as unsolicited calls from criminals impersonating the IRS, the FBI, or Microsoft support. The approach was simple and high volume.
Then telecom providers began labeling suspicious calls with warnings such as “Scam Likely.” Call blocking and analytics disrupted the economics of outbound vishing. Attackers responded by changing who initiates the call.
Instead of dialing the victim directly, they began sending emails that instructed the recipient to call a phone number regarding a fake invoice, subscription renewal, or account issue.
By shifting the point of origin, criminals bypassed call-labeling protections and gained an immediate credibility boost. The victim placed the call, so the interaction felt legitimate.
I refer to this model as hybrid vishing because it combines email delivery with voice-based social engineering.
As secure email gateways improved and detection models became more effective at identifying invoice-themed lures, attackers faced a new challenge: message deliverability.
If traditional phishing emails could not reliably reach inboxes, an alternative trusted delivery channel was required.
That requirement led to the latest evolution in vishing tactics: service abuse.
Abusing Trusted Platforms for Message Delivery
Rather than sending malicious emails from attacker-controlled infrastructure, criminals are increasingly abusing legitimate SaaS platforms to deliver their lures.
Below is an example of Google Calendar being abused to deliver a hybrid vishing message:
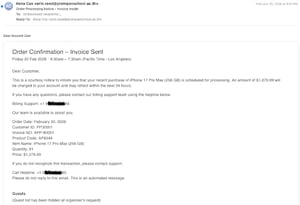
In this case, the attacker created a calendar invitation with the meeting title “Order Confirmation – Invoice Sent” and embedded the vishing instructions within the meeting description. When secure email gateways evaluate the message, they see a legitimate calendar invitation generated by Google’s infrastructure. The message structure, headers, and sending IP all align with expected patterns for Google Workspace traffic.
From an authentication standpoint, the message passes SPF, DKIM, and DMARC. From a reputation standpoint, it originates from a highly trusted domain. From a content standpoint, it is formatted as a standard calendar notification.
Many filtering systems therefore classify the message as a legitimate collaboration artifact rather than a phishing attempt.
Over the past several months, we have observed similar abuse involving Microsoft and Google calendar invitations, Zoom meeting invitations, and other collaboration tools.
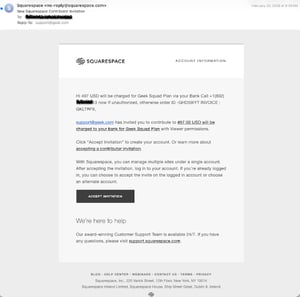
One recent example involved abuse of Squarespace’s website collaboration workflow.
Squarespace allows customers to build and manage websites collaboratively. Administrative users can invite contributors by entering a name and email address. Squarespace then sends an automated invitation email that includes the project name and related details.
The email originates from Squarespace’s servers and passes SPF, DKIM, and DMARC validation. Because the sending domain has a strong reputation, the message is highly likely to reach the recipient’s inbox.
In the observed case, the attacker populated the “name” field with the following text:
“497 USD will be charged for Geek Squad Plan via your Bank Call +1 (802) XXX – XXXX now If unauthorized, otherwise order ID -GHD59IYT INVOICE : GKLTRF9”
The project name was set to:
“497.00 USD will be charged to your bank for Geek Squad Plan”
The result was a fully authenticated, brand-legitimate email carrying a classic refund scam lure. No spoofing was required. No malicious infrastructure was used.
The attacker simply weaponized user-controlled input fields inside a trusted platform. Below is what the recipient saw in their inbox:
Why This Works
This technique exploits a structural asymmetry in email security.
Email authentication protocols such as SPF, DKIM, and DMARC validate domain control.
They do not validate intent. If an attacker can inject malicious content into a legitimate platform that sends authenticated mail, the message inherits that platform’s reputation.
Secure email gateways heavily weight sender reputation and authentication alignment.
When both indicators are positive, content-based detection must carry the full burden of identifying fraud. But because the message is formatted as a legitimate workflow notification, detection models may treat it differently from a traditional phishing email.
The attacker effectively outsources infrastructure, reputation, and deliverability to the abused service provider.
Business Risk and Impact
This shift creates risk on multiple levels.
For end users and enterprises, hybrid vishing attacks often result in direct financial loss.
Victims who call the number provided are socially engineered into granting remote access, transferring funds, or disclosing sensitive information.
Because the victim initiates the call, traditional telephony defenses offer no protection.
For service providers, the impact is reputational and operational. Platforms that are repeatedly abused for fraud may experience:
- Brand damage and erosion of user trust
- Increased abuse reports and support costs
- Potential regulatory scrutiny if controls are deemed insufficient
- Increased filtering or blocking of their legitimate email traffic by downstream mail providers
In extreme cases, large-scale abuse can degrade the deliverability of all transactional email originating from the platform.
Mitigation Strategies for Service Providers
Any service that sends automated messages containing user-controlled content can be abused in this manner.
Service providers should implement layered controls, including:
- Input validation and sanitization
Restrict character sets, limit numeric content in name fields, and enforce reasonable length constraints. For example, a “name” field should not accept full sentences containing dollar amounts and phone numbers.
- Content anomaly detection
Apply automated scanning to outbound transactional emails. Flag or block invitations that contain high-risk keywords, phone numbers combined with currency references, or common refund scam language.
- Contextual warning banners
For collaboration platforms such as calendar systems, prepend warning notices when invitations contain suspicious financial language or external phone numbers. While not a complete solution, visible friction reduces attacker success rates.
- Rate limiting and abuse monitoring
Detect patterns such as large volumes of invitations containing financial terminology or repeated use of phone numbers across unrelated accounts.
Guidance for End Users
End users remain the final line of defense.
Never call the phone number listed in an unsolicited invoice, subscription alert, or meeting invitation. Instead, independently look up the organization’s official contact information and initiate communication using a trusted source.
If a message creates urgency around a financial transaction, assume social engineering until proven otherwise.
Bottom Line
Vishing is not new, but the delivery mechanisms continue to evolve.
As defenders deploy controls at one layer, attackers shift to another. Today, they are exploiting the trust and infrastructure of legitimate online services to ensure their lures reach the inbox.
The voice channel remains the monetization engine, but SaaS platforms have become the delivery vehicle.
Organizations that treat email authentication as a complete solution will continue to be surprised. Authentication proves who sent the message. It does not prove that the message should have been sent at all.


