editorially independent. We may make money when you click on links
to our partners.
Learn More
Cisco is warning customers that attackers are actively exploiting multiple vulnerabilities affecting its Catalyst SD-WAN Manager platform.
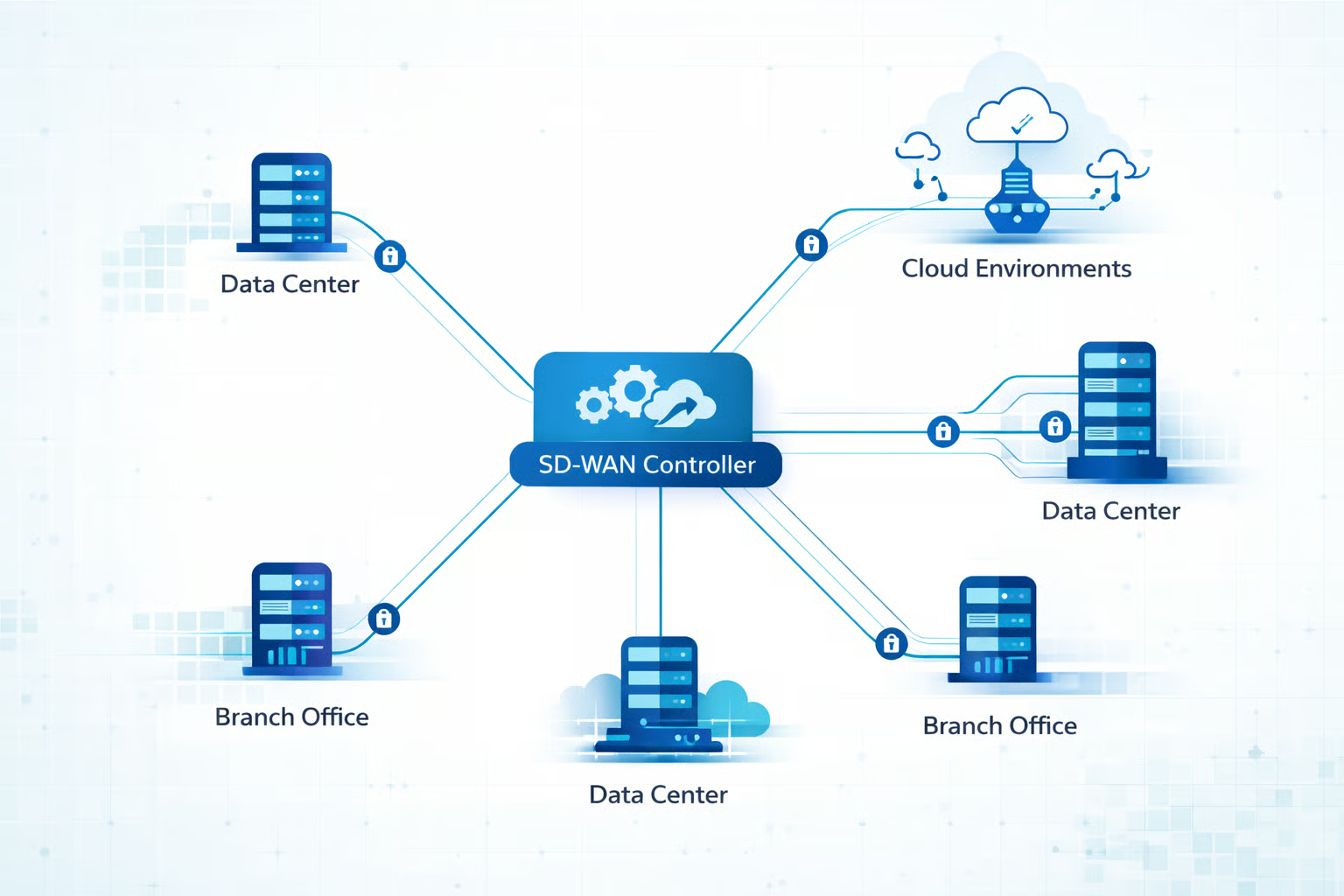
The software serves as a centralized management console used to monitor and control large distributed SD-WAN deployments.
These vulnerabilities “… could allow an attacker to access an affected system, elevate privileges to root, gain access to sensitive information, and overwrite arbitrary files,” said Cisco in its advisory.
Inside the Cisco SD-WAN Manager Vulnerabilities
Catalyst SD-WAN Manager plays a central role in many enterprise networking environments by providing administrators with a unified platform to monitor, configure, and manage large distributed SD-WAN deployments.
Because the platform functions as the control plane for SD-WAN environments, it has broad visibility into network topology, device configurations, and traffic routing policies.
If attackers were able to compromise the SD-WAN management system, they could potentially manipulate routing policies, monitor network activity, or introduce malicious devices into trusted network infrastructure.
This level of access could allow threat actors to quietly expand their presence inside an enterprise network while appearing as legitimate infrastructure.
The vulnerabilities currently being exploited include CVE-2026-20122, a high-severity arbitrary file overwrite vulnerability, and CVE-2026-20128, a medium-severity information disclosure flaw.
Both weaknesses impact the SD-WAN Manager platform and can potentially be used as part of a broader attack chain.
CVE-2026-20122
This arbitrary file overwrite vulnerability can be exploited remotely by attackers who already possess valid read-only credentials with API access.
By abusing the flaw, attackers may be able to overwrite files on the system, potentially altering system behavior, modifying configurations, or enabling additional malicious activity within the environment.
CVE-2026-20128
The second vulnerability, CVE-2026-20128, requires attackers to have valid local credentials on the targeted SD-WAN Manager system.
When exploited, the flaw could allow attackers to retrieve sensitive information stored within the platform, such as system configuration details or operational data.
While both vulnerabilities require authenticated access, they still present a risk because threat actors can obtain credentials through phishing campaigns, credential stuffing, or previously compromised systems.
Cisco confirmed that both vulnerabilities are actively being exploited in the wild at the time of publication.
This disclosure follows another recent one involving CVE-2026-20127, a critical authentication bypass vulnerability that has been exploited in attacks since at least 2023.
That flaw allowed attackers to compromise SD-WAN controllers and introduce rogue peers into targeted networks.
These rogue peers appear as legitimate SD-WAN devices within the network fabric, allowing attackers to establish persistence, intercept traffic, and move deeper into compromised environments.
Cisco has released patches for the vulnerabilities.
Hardening SD-WAN Environments
Organizations using Cisco Catalyst SD-WAN Manager should take proactive steps to reduce the risk associated with these vulnerabilities.
Applying the latest software updates is the most effective way to remediate the issue, but additional security controls can further strengthen protection.
- Upgrade Catalyst SD-WAN Manager to the latest patched versions to remediate the vulnerabilities.
- Restrict access to SD-WAN management interfaces by removing public internet exposure and limiting access to trusted networks or VPN connections.
- Enforce strong authentication and least-privilege access controls, including multi-factor authentication and restricted API permissions for administrative accounts.
- Segment SD-WAN controllers and management infrastructure on dedicated management networks to reduce lateral movement risk if a compromise occurs.
- Monitor authentication logs, API activity, configuration changes, and network traffic for unusual behavior that may indicate exploitation.
- Audit SD-WAN device inventories and routing configurations regularly to identify unauthorized peers or suspicious network changes.
- Test incident response plans and build playbooks with scenarios around SD-WAN compromise.
Together, these measures can help limit the potential blast radius of a compromise and strengthen the resilience of an organization’s SD-WAN infrastructure.
Why Attackers Target SD-WAN Management Platforms
The active exploitation of SD-WAN vulnerabilities reflects a broader trend in which attackers focus on centralized network management platforms rather than individual endpoints.
These systems provide broad visibility into network topology, routing policies, and connected devices, making them attractive targets.
If compromised, a management platform could potentially allow attackers to observe network activity, alter configurations, or introduce unauthorized devices into the environment.
These risks are one reason organizations implement zero trust architectures that are designed to reduce implicit trust and limit the impact of compromises involving centralized network management systems.