
A previously undocumented threat actor tracked as UAT-9244 has been targeting telecommunications providers across South America using a set of newly identified malware implants designed to maintain long-term access and expand network infiltration.
The activity was disclosed in a report by Cisco Talos researchers, who analyzed recent intrusions affecting telecom infrastructure in the region. According to Talos, the campaign has been active since at least 2024 and involves a combination of Windows and Linux malware deployed across enterprise endpoints and network edge devices.
Talos assesses with high confidence that UAT-9244 is closely associated with the FamousSparrow advanced persistent threat (APT) group and shares operational overlap with Tropic Trooper, two China-linked threat clusters previously tied to cyber-espionage campaigns targeting governments, telecom providers, and critical infrastructure.
Although the targeting overlaps with operations attributed to the Chinese state-linked Salt Typhoon group, which also focused on telecom providers, Talos said it could not confirm a direct connection between the clusters.
Three new malware families
The campaign relies on three primary malware implants, TernDoor, PeerTime, and BruteEntry, which together provide remote access, persistence, and network expansion capabilities.
The most prominent of the three is TernDoor, a Windows backdoor derived from CrowDoor, itself a variant of the SparrowDoor malware associated with FamousSparrow operations.
Researchers observed the malware being deployed via DLL side-loading, a technique that disguises malicious components as legitimate software. In the observed infection chain, attackers executed a benign program, wsprint.exe, which loaded a malicious DLL, BugSplatRc64.dll.
The DLL retrieves an encrypted file named WSPrint.dll, decrypts it using the key “qwiozpVngruhg123,” and executes shellcode that ultimately loads the TernDoor backdoor directly into memory.
Once active, TernDoor communicates with command-and-control (C2) servers and allows operators to run commands, manage files, gather system information, and deploy additional tools. The malware also installs a malicious driver, WSPrint.sys, which can suspend or terminate processes to evade detection or disable security software.
To maintain persistence, the malware creates a scheduled task named “WSPrint” that runs with SYSTEM privileges when the system starts. In some cases, it also adds a Windows Registry Run key so the malware launches whenever a user logs in.
Peer-to-peer Linux backdoor
Talos also identified a second backdoor, PeerTime, targeting Linux environments and embedded systems commonly found in telecom infrastructure.
Unlike traditional malware that relies on centralized infrastructure, PeerTime uses the BitTorrent protocol to obtain command-and-control information and download payloads from peers, making it harder to disrupt.
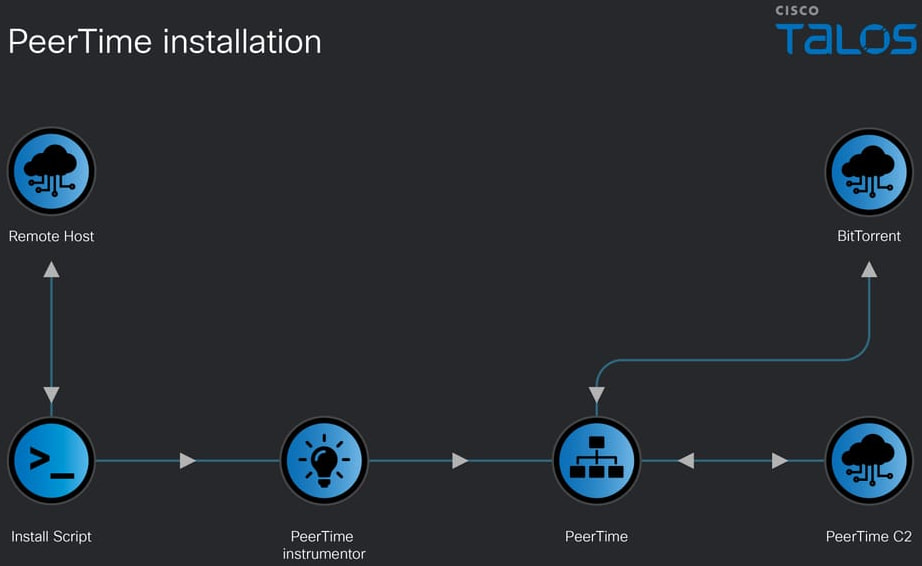
PeerTime is compiled for multiple architectures, including ARM, MIPS, PowerPC, and AArch64, indicating it can infect a wide range of devices such as routers, network appliances, and other embedded systems.
The malware is deployed via a shell script that installs a loader and an “instrumentor” component. If the compromised system has Docker installed, the loader is executed inside a container environment.
Turning infected hosts into scanning nodes
The third tool used in the campaign, BruteEntry, is designed to convert compromised Linux systems, particularly edge devices, into operational relay boxes (ORBs) that scan the internet for additional targets.
Written in Go, BruteEntry registers with a command-and-control server and receives lists of IP addresses to probe. It then attempts to brute-force credentials for services commonly exposed on enterprise networks, including SSH, PostgreSQL databases, and Apache Tomcat management interfaces.
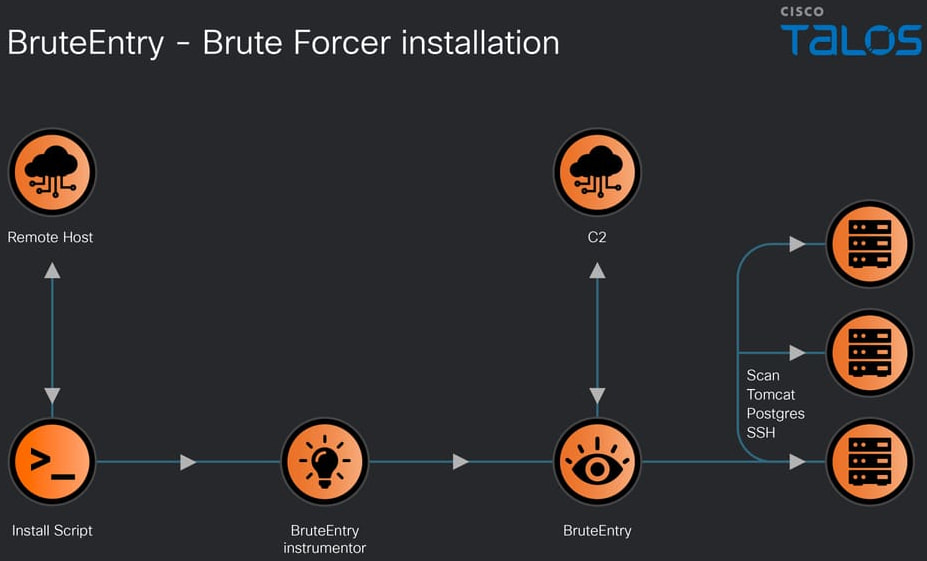
Any successful logins are reported back to the attackers’ infrastructure, allowing them to expand access into additional systems.
Telecommunications providers remain a high-value espionage target due to their access to large volumes of sensitive communications data and network infrastructure.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


