editorially independent. We may make money when you click on links
to our partners.
Learn More
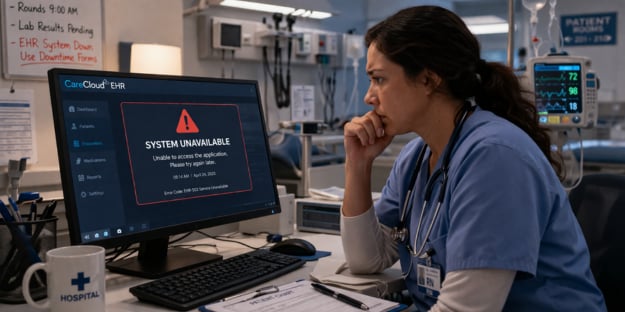
An attack on healthcare IT provider CareCloud has exposed sensitive patient data and temporarily disrupted access to critical systems, highlighting ongoing risks facing digital healthcare infrastructure.
We are “… continuing to investigate the nature and scope of the incident. The affected environment stores patient information, and the Company continues to assess whether, and the extent to which, patient information or other data was accessed or exfiltrated, and the categories and volume of any such data,” said the company in its SEC filing.
What We Know About the CareCloud Incident
CareCloud, a SaaS provider of electronic health record (EHR) and practice management solutions, confirmed unauthorized access to an environment containing patient health data.
Although the company described the incident as limited in scope, the breach underscores ongoing concerns around third-party vendor risk and the potential exposure of protected health information (PHI) within shared healthcare platforms.
At this point, CareCloud has not determined how many individuals were affected or what specific data elements may have been accessed or exfiltrated, leaving the full impact of the incident unclear.
The intrusion appears to have targeted CareCloud’s internal IT infrastructure, specifically affecting one of its six EHR environments used by customers.
While the company restored functionality within approximately eight hours, even brief disruptions can impact healthcare operations that rely on continuous, real-time access to patient records.
The absence of any ransomware group claiming responsibility suggests this may have been a data-focused intrusion rather than an extortion-driven attack.
Although CareCloud has not disclosed the initial attack vector, incidents of this nature can originate from compromised credentials, unpatched vulnerabilities, or misconfigured systems.
Once inside a network, attackers often attempt lateral movement to identify and access high-value assets such as EHR databases and other repositories of sensitive data.
In this case, the compromise was contained to a single environment, which helped limit the overall blast radius.
However, the involvement of patient health records elevates the severity of the incident, as healthcare data remains highly valuable on underground markets due to its depth, persistence, and potential for fraud.
How to Reduce Healthcare SaaS Risk
Organizations relying on healthcare SaaS platforms must take a proactive and layered approach to cybersecurity to reduce risk and limit the impact of potential breaches.
- Conduct third-party risk assessments and continuously monitor third-party SaaS security posture and integrations.
- Enforce strong identity and access controls, including MFA, least privilege, and privileged access management.
- Monitor systems and networks for unusual activity using centralized logging, SIEM, and endpoint detection tools.
- Maintain timely patching and secure configurations across all systems, applications, and cloud environments.
- Protect sensitive data through encryption, data minimization, and using DLP tools to limit breach impact.
- Test incident response plans for scenarios involving data compromise.
- Strengthen overall security architecture with zero trust principles, network segmentation, and resilient backup strategies.
CareCloud stated it has engaged external cybersecurity experts to investigate the incident and strengthen its defenses, and confirmed that the threat actor no longer has access to its systems.
Healthcare Supply Chain Cyber Risk
The CareCloud incident highlights a broader shift toward attacks targeting healthcare technology SaaS vendors rather than individual physician practices.
As reliance on SaaS platforms grows, a single incident can affect multiple organizations that depend on those services.
This reinforces the need for strong supply chain security practices and clear shared responsibility between vendors and their customers when it comes to protecting sensitive data.
To address these evolving risks, organizations are adopting zero trust solutions to strengthen access controls and reduce the potential impact of breaches.