editorially independent. We may make money when you click on links
to our partners.
Learn More
A 22-year-old Alabama man has pleaded guilty to federal charges after hijacking the social media accounts of hundreds of young women and extorting them with stolen intimate images.
Between 2022 and 2025, Jamarcus Mosley used impersonation tactics to seize control of victims’ Snapchat and Instagram accounts, then threatened to publish private photos unless they complied with his demands.
“Mosley is the dangerous online stranger who every parent fears,” said U.S. Attorney Theodore S. Hertzberg in the press release.
He explained, “By exploiting the trust of teens and young adults, Mosley hacked into their accounts to steal intimate and sexually suggestive images and extort them over a three-year period.”
Theodore added, “This cruel, calculated scheme is the latest reminder that everyone must exercise great care with whom they interact online.”
Inside the Multi-State Sextortion Campaign
According to federal prosecutors, Mosley impersonated friends and acquaintances of his victims to manipulate them into sharing account recovery codes and passwords.
Once he obtained those credentials, he allegedly took over their social media accounts, locked them out, accessed private images and videos, and used that material to demand additional explicit content or money.
Federal court filings indicate that victims spanned multiple states and included minors.
In one instance, prosecutors said Mosley posed as a high school friend of a 20-year-old Georgia woman to obtain her Snapchat recovery code.
After gaining access to her account, he allegedly sent a threatening message claiming he had “65 videos and [a] picture of you about to get posted.”
In another case, when an 18-year-old Florida woman refused his demands, he reportedly followed through by publishing her stolen images online.
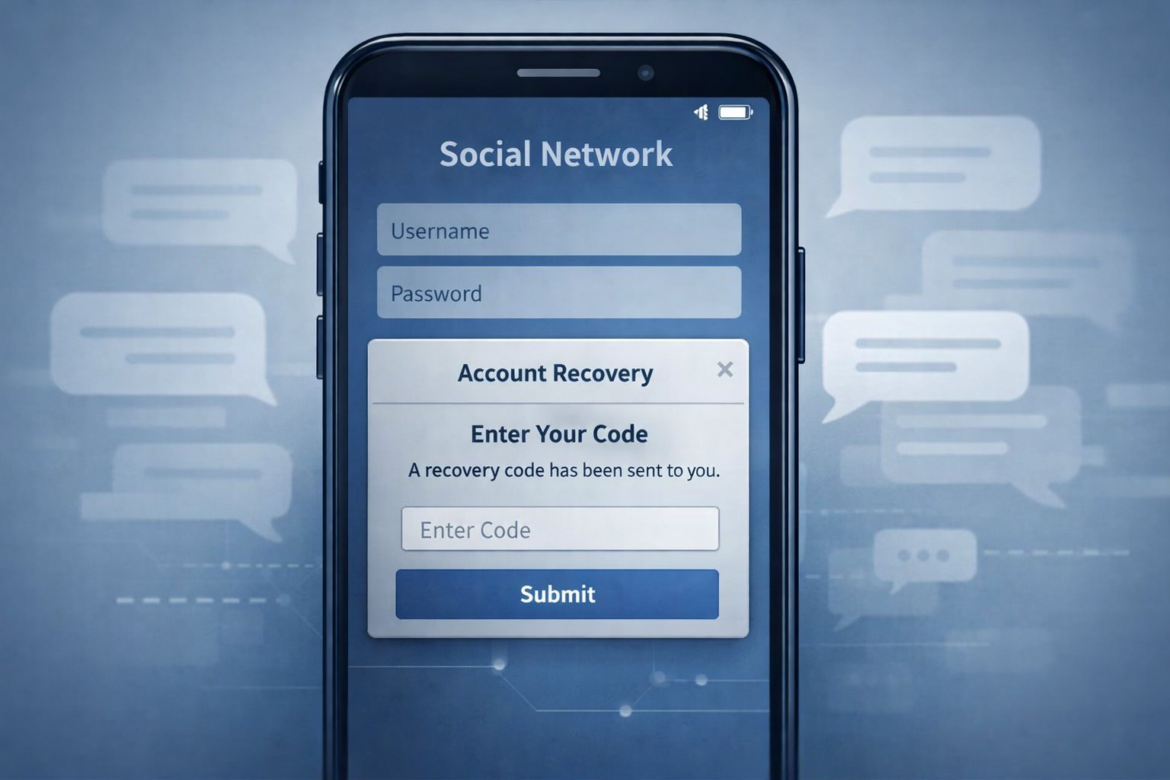
Abuse of Account Recovery Workflows
At the center of the scheme was abuse of account recovery workflows. Social media platforms provide recovery codes and password reset mechanisms to help legitimate users regain access to their accounts.
However, if a victim shares that recovery code — even unknowingly — with a malicious actor, control of the account can effectively be transferred.
Prosecutors allege that Mosley exploited this design by convincing victims he was a trusted contact who needed the code, thereby bypassing authentication safeguards without deploying any technical exploit.
From Digital Coercion to Real-World Intimidation
Once inside the accounts, he allegedly harvested stored private content and escalated his coercion.
Victims were threatened with public exposure, doxing, or further harassment unless they provided additional explicit material, access to more accounts, or financial payments.
In one particularly alarming example described in court documents, Mosley allegedly used a compromised account belonging to a 17-year-old Illinois victim to contact a Florida woman’s 13-year-old sister, sending a Snapchat map image to suggest he knew her physical location.
That escalation demonstrates how sextortion schemes can evolve from digital manipulation into implied real-world intimidation.
This case demonstrates how deception can exploit human trust within legitimate authentication processes, enabling attackers to gain elevated access when victims share recovery credentials under false pretenses.
For schools, parents, and digital safety teams, it highlights the ongoing threat posed by sextortion campaigns that depend more on psychological coercion than technical sophistication.
Mosley pleaded guilty to charges including extortion, cyberstalking, and computer fraud. He is scheduled to be sentenced in May 2026.
Steps to Reduce Sextortion Risk
Preventing sextortion and account takeover requires both organizational safeguards and individual vigilance.
What Organizations Can Do
Organizations should take a layered approach that combines technical controls, user education, and response preparedness.
- Enforce multi-factor authentication using app-based authenticators or hardware keys, restrict account recovery options, and monitor for unusual login or credential reset activity.
- Implement structured digital safety and social engineering awareness programs, especially for youth populations, and establish clear, confidential reporting pathways for sextortion incidents.
- Deploy technical safeguards such as DNS filtering, privacy controls, restricted messaging settings, and endpoint monitoring to detect suspicious access or coercive activity.
- Coordinate proactively with social media trust and safety teams and law enforcement to accelerate takedowns and preserve digital evidence when incidents occur.
- Test incident response plans through tabletop exercises that simulate account takeover and sextortion scenarios to ensure rapid containment, evidence preservation, and victim support.
What Individuals Can Do
Individuals can reduce risk by strengthening account security and recognizing manipulation tactics early.
- Never share passwords, recovery codes, or one-time passcodes with anyone, even if the request appears to come from a friend or trusted contact.
- Enable multi-factor authentication on all social media accounts and review login activity regularly for unfamiliar devices or locations.
- Limit publicly visible personal information and restrict direct messages from unknown users to reduce impersonation opportunities.
- Pause and verify unexpected requests for account access by contacting the person through a separate, trusted communication channel before responding.
Together, these steps help reduce the likelihood of account compromise while improving the speed and effectiveness of response when social engineering attacks occur.
Sextortion Remains a Growing Cyber Risk
Mosley’s guilty plea brings accountability in one case, but the broader threat of sextortion remains a persistent challenge driven by human manipulation rather than technical exploits.
As this case illustrates, attackers often succeed by exploiting trust and misusing legitimate account recovery features, making awareness and layered defenses essential.
For families, schools, and organizations alike, sustained education, stronger authentication practices, and clear reporting pathways are critical to reducing harm and supporting victims when incidents occur.
To support these efforts, organizations are turning to leading cybersecurity companies that specialize in identity protection, threat detection, and risk mitigation solutions.