
A digital payment skimmer has been discovered on the online store of one of the world’s largest supermarket chains.
Despite multiple disclosure attempts by Sansec, the malicious code remained active at the time of publication.
According to the researchers, the skimmer was first detected on February 16 at 06:13 UTC on an e-commerce site operated by a top-10 global supermarket chain generating approximately €100 billion in annual revenue and running more than 10,000 stores across 25 countries. Part of the retailer’s e-commerce infrastructure is powered by PrestaShop, a widely used open-source e-commerce platform.
Sansec says it attempted to notify the company six times on February 16 through various channels, including the general contact email listed on the retailer’s website, the security contact specified in its security.txt file, and a direct message to the company’s CISO on LinkedIn. As of February 20, the researchers had received no response and confirmed that the skimmer was still operational.
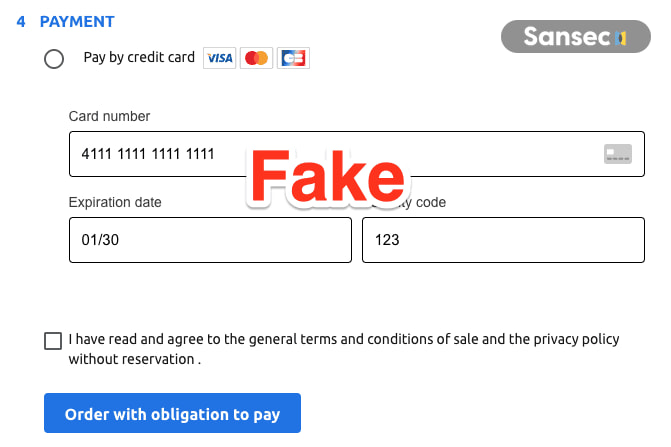
The attack leverages a technique known as “double-tap skimming,” which has grown in popularity as merchants increasingly rely on PCI-DSS-compliant hosted payment pages. Under PCI-DSS rules, sensitive card data must be entered into secure, provider-hosted forms, such as those operated by PayPlug in this case. Threat actors work around this by inserting a convincing fake payment form directly into the checkout page. Victims enter their card number, expiry date, and CVV into the fraudulent overlay, after which they are seamlessly redirected to the legitimate payment form and prompted to re-enter their details. Most customers assume the first attempt failed and complete the transaction, unaware that their card data has already been stolen.
Sansec
Sansec notes that generative AI is accelerating this type of fraud, enabling attackers to rapidly produce localized, brand-consistent payment overlays tailored to different languages and markets.
The skimmer itself is built on a reusable framework that appears to support WordPress, Magento, PrestaShop, and OpenCart. Before activating, it performs a series of checks to detect whether the visitor is an administrator. In such a case, the script logs an “Admin detected” message and aborts, ensuring store operators do not see the malicious form while testing their own checkout.
The framework supports seven injection modes, including replace, overlay, popup, and offscreen rendering, allowing it to adapt to different checkout layouts. An “aggressive hiding” mechanism keeps the legitimate payment form suppressed even if the site’s own JavaScript attempts to restore it.
Technically, the skimmer activates only on checkout pages and uses localStorage to manage its execution state. It monitors all input, select, and textarea elements via event listeners, and even tracks dynamic dropdown components such as Select2 and Vue Select using MutationObserver. Captured data is stored under localStorage keys prefixed with “mn_”, while card details are saved specifically as cardNum, exp, and cvv.
To prevent the stolen data from being overwritten, the script monkey-patches localStorage.setItem, blocking attempts to replace stored card numbers with shorter strings. When the victim clicks the checkout button, the malware validates that the card number contains at least 13 digits, builds a JSON payload containing card and billing data along with the browser’s user agent, Base64-encodes it, and exfiltrates it via a GET request to ‘stylemercedes.top.’
The endpoint is disguised as an analytics API to avoid suspicion. After exfiltration, the malicious code removes its injected elements, restores the original checkout page, re-enables any disabled checkout buttons by stripping the disabled and aria-disabled attributes and numerous CSS classes, and programmatically triggers the legitimate payment process.
Customers can mitigate the risk of having their payment card information stolen by using pre-loaded, one-time virtual cards during checkout.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


