For years, some Mac users believed their devices were largely insulated from the malware plaguing Windows environments. That perception is rapidly eroding.
Flare researchers found a growing underground economy is now centered on macOS Infostealers — malware designed to extract browser credentials, Apple Keychain data, and cryptocurrency wallet seed phrases at scale.
“I remember that about 15 years ago, a CEO I worked with received malware from his CPA. It never executed because it was Windows-based and he was using a Mac,” said Assaf Morag, cybersecurity researcher at Flare in an email to eSecurityPlanet.
He added, “Those days are over. Today, macOS malware is on the rise, and Infostealers are at the center of the current threat landscape.”
The Underground Marketplace Expands
The macOS Infostealer ecosystem is no longer fragmented or experimental — it is organized, commercialized, and highly competitive.
Across criminal forums such as BDFClub and Voided, operators openly advertise Mac/Win fully undetectable malware (FUD) stealers, subscription-based management panels, and affiliate distribution programs.
Listings often read like legitimate product announcements, highlighting new features, performance improvements, and anti-detection capabilities.
Groups such as QuarkLab promote updated control panels with faster builds and streamlined deployment, iterating based on user feedback much like legitimate software vendors.
These operations demonstrate clear operational maturity. Revenue-sharing agreements are common, with some operators offering 50/50 splits to traffickers who drive installation traffic.
Others provide encrypted builds, real-time statistics dashboards, and dedicated support channels.
In one example, an operator stated they were exclusively interested in cryptocurrency theft, allowing affiliates to retain all other stolen data.
This division of labor reflects specialization across the ecosystem — developers focus on malware engineering and wallet extraction logic, while partners handle distribution, phishing infrastructure, and advertising.
macOS Infostealers are part of a structured malware-as-a-service (MaaS) economy with defined roles, monetization models, and ongoing development.
From Terminal Tricks to Signed Malware
The evolution of macOS infostealers reflects a clear shift from crude social engineering to engineered, trust-based compromise.
Early campaigns often relied on “drag-to-Terminal” lures, where victims were instructed to paste shell commands into a Terminal window under the guise of fixing an issue or installing legitimate software.
While effective against less technical users, these tactics were noisy and increasingly easy to detect or block through user awareness and endpoint monitoring.
That approach has largely been replaced by more advanced delivery methods designed to blend seamlessly into Apple’s security model.
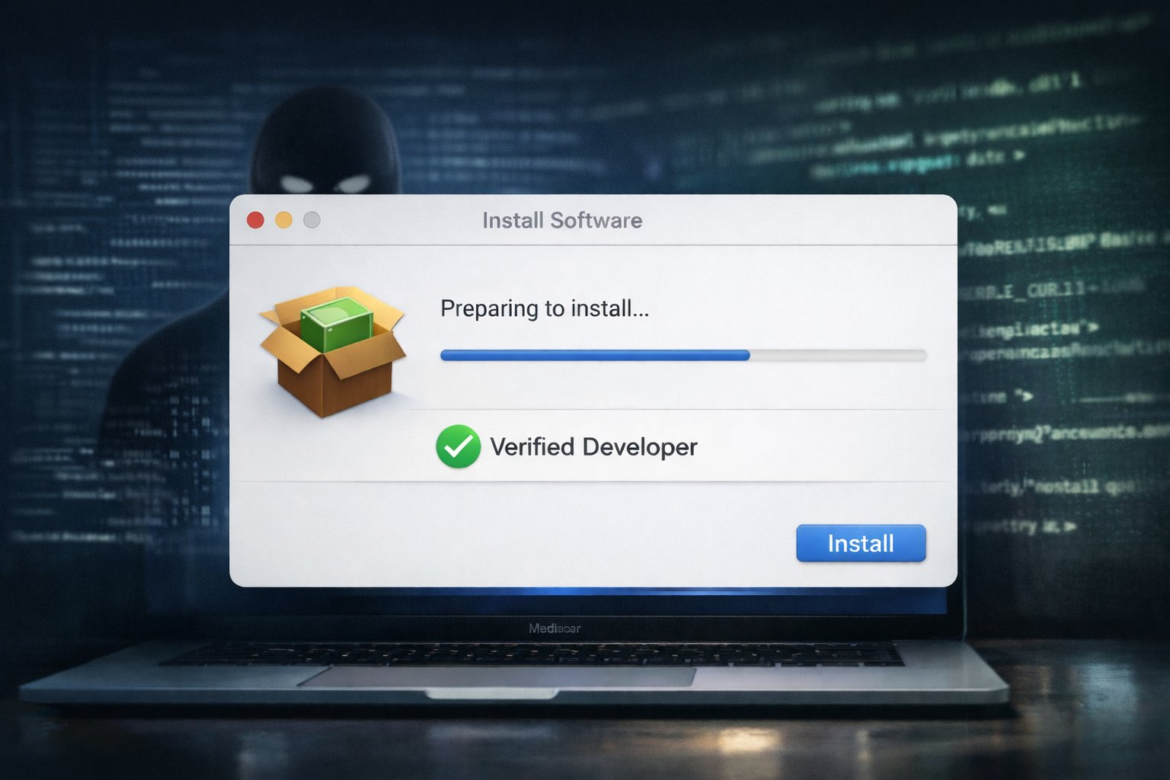
Researchers identified macOS malware distributed inside disk image (DMG) files masquerading as legitimate installers.
The payloads were embedded in fully signed and notarized applications, allowing them to pass Gatekeeper checks without triggering warnings.
Because macOS relies heavily on code signing and notarization to establish trust, malware carrying a valid developer signature appears indistinguishable from legitimate software during installation.
In one documented case, the malicious binary was signed and notarized under Developer Team ID GNJLS3UYZ4 before discovery.
Although Apple revoked the certificate, the case showed attackers can obtain legitimate signing credentials and use them to bypass built-in protections by exploiting Apple’s trust infrastructure rather than evading it.
Anti-Forensic Capability
Modern macOS stealers go further by incorporating anti-analysis techniques and operational safeguards.
Samples have included environment checks to avoid execution in sandboxed or research environments, connectivity validation before launching payloads, and inflated DMG file sizes filled with decoy content to evade heuristic detection.
Some variants remove intermediary scripts to limit forensic traces, reflecting a shift from opportunistic tools to professionally engineered payloads built for stealth and persistence within Apple’s ecosystem.
Abuse of Trusted Platforms
Beyond improving their malware, threat actors are increasingly abusing legitimate platforms and infrastructure to distribute macOS Infostealers.
Google’s Threat Intelligence Group documented one such campaign involving UNC5142, a financially motivated threat actor that has compromised more than 14,000 WordPress sites.
The group injected malicious JavaScript into legitimate sites and used BNB Smart Chain smart contracts for command-and-control, a technique known as EtherHiding.
Instead of hosting C2 instructions on traditional servers that can be seized or blocked, the attackers stored payload references within blockchain transactions.
Because blockchain data is distributed and immutable, takedown efforts become more complex.
At the network level, outbound connections to blockchain nodes may also blend with legitimate Web3 traffic, complicating detection efforts for defenders.
Other campaigns have demonstrated how attackers can exploit trust in emerging technologies.
Researchers identified threat actors posting malicious instructions within ChatGPT and Grok conversations, then promoting those shared chats through paid Google Ads.
Users searching for legitimate software help encountered sponsored results linking to AI-generated instructions that directed them to paste commands into Terminal, ultimately installing the AMOS macOS stealer.
The technique leverages the perceived authority of both search engine rankings and AI platforms, reducing skepticism that might otherwise arise.
Cryptocurrency as the Primary Target
A defining characteristic of the current macOS Infostealer ecosystem is its intense focus on cryptocurrency theft.
Recruitment posts promote support for over 100 Chrome crypto extensions and phishing modules targeting Ledger, Trezor, Exodus, and Atomic wallets.
Rather than treating crypto wallets as a secondary data source, many operators position digital asset theft as the primary monetization strategy.
The technical workflows reflect this priority.
Some phishing modules are designed to validate seed phrases in real time, notifying victims if an entered word is incorrect to maintain credibility and reduce suspicion.
In other cases, malware automatically extracts wallet seed phrases or private keys immediately after a user unlocks their wallet.
Notably, certain compromised wallets continue functioning normally after exfiltration, delaying detection and allowing attackers to move funds without immediately alerting the victim.
This emphasis is driven by clear economic incentives.
Cryptocurrency transactions are irreversible and pseudonymous, making recovery extremely difficult once funds are transferred.
Steps to Secure macOS Environments
As macOS Infostealers continue to evolve, organizations should ensure their Mac endpoints are governed with the same depth of visibility and control as other enterprise systems.
Signed malware, wallet-focused phishing, and abuse of trusted infrastructure require layered defenses across endpoint, identity, and network environments.
- Deploy macOS-capable EDR and enable deep telemetry to monitor for unusual Terminal activity, Keychain access, suspicious process execution, and anomalous outbound connections, including blockchain traffic.
- Enforce strict application control and allowlisting policies, validating even signed and notarized applications against approved software inventories.
- Restrict unapproved browser extensions and harden browser configurations, including limiting credential storage and enforcing enterprise password managers.
- Strengthen identity and access controls by applying least privilege, multi-factor authentication, and tighter restrictions on developer tools and elevated permissions.
- Use network-layer defenses such as DNS filtering, secure web gateways, and segmentation to block malicious domains and limit lateral movement from compromised macOS devices.
- Monitor for abuse of developer certificates, configuration profile installations, and bulk access to sensitive data stores such as Keychain and browser credential databases.
- Regularly test incident response plans through tabletop exercises and red team simulations that include macOS-specific Infostealer and signed malware scenarios.
A structured, defense-in-depth approach helps reduce exposure and improve detection across the macOS ecosystem.
macOS in the Crosshairs
The growth of macOS Infostealers reflects a broader shift in attacker priorities, with threat actors focusing on platforms that combine strong user adoption and financial value.
Organized MaaS models, signed payloads, blockchain-based infrastructure, and cryptocurrency-focused theft demonstrate that macOS is now a consistent and economically viable target.
As adversaries increasingly target trusted platforms, organizations look to zero-trust solutions to better control access, limit lateral movement, and reduce the impact of endpoint compromise.