
A data breach affecting education publisher McGraw Hill has resulted in the exposure of 13.5 million user records.
The incident, which occurred earlier this month, has now been independently verified through analysis of the leaked dataset by Have I Been Pwned (HIBP).
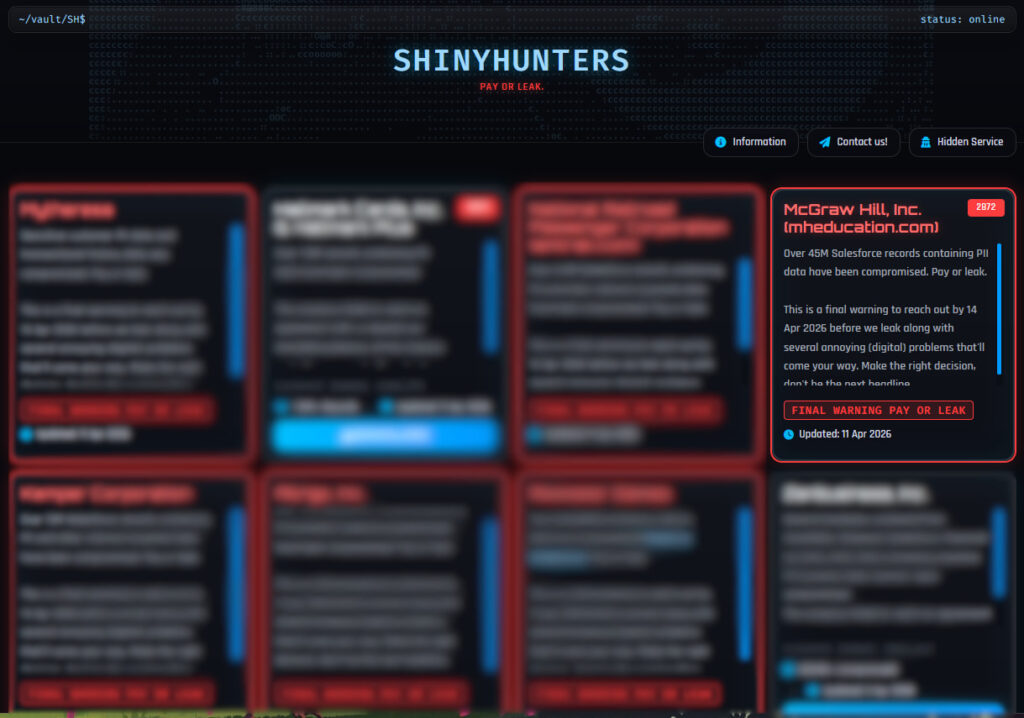
The breach first surfaced on ShinyHunters’ extortion portal, where the group claimed to have compromised tens of millions of Salesforce records tied to McGraw Hill and threatened to release them unless payment was made. The listing included a “pay or leak” ultimatum and references to a large volume of sensitive data. When negotiations apparently failed, the group followed through, publishing over 100 GB of data online.
Subsequent analysis of the leaked files shows that they contain approximately 13.5 million unique email addresses, alongside additional personal information such as names, phone numbers, and physical addresses, although these fields are not consistently present across all records.
McGraw Hill acknowledged the incident earlier this week, attributing it to a Salesforce-related misconfiguration rather than a direct compromise of its internal systems. In a statement shared with media, the company said attackers accessed “a limited set of data from a webpage hosted by Salesforce on its platform,” adding that the issue appears tied to a broader configuration problem affecting multiple Salesforce customers. The company emphasized that its core systems, including customer databases and courseware platforms, were not directly accessed.
McGraw Hill is one of the largest educational content providers globally, serving millions of students, educators, and professionals through its digital platforms and traditional publishing operations. Its reliance on cloud-based infrastructure, including Salesforce services, reflects a broader industry shift toward third-party platforms, an approach that can introduce systemic risks when misconfigurations occur.
The ShinyHunters group has a well-established track record of targeting cloud services and exposed databases, often exploiting weak points in third-party integrations rather than breaching primary infrastructure. Their tactics typically involve data exfiltration followed by extortion, with full dataset leaks used as leverage when victims refuse to pay.
While nearly half of the exposed email addresses had appeared in previous breach collections, a substantial portion are newly exposed, increasing the risk for affected individuals. Even in the absence of passwords, the combination of contact details can be leveraged in phishing campaigns, identity fraud, and other social engineering attacks.
Users potentially impacted by the breach should remain alert for suspicious communications, particularly those impersonating educational services or requesting sensitive information. It is advisable to use unique passwords across accounts, enable multi-factor authentication wherever possible, and monitor financial and online accounts for unusual activity.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


