editorially independent. We may make money when you click on links
to our partners.
Learn More
A brief compromise of the popular Axios npm package shows how quickly a trusted dependency can become a widespread threat.
Attackers hijacked a maintainer account and published malicious versions that silently installed a remote access trojan (RAT) during routine package installs, putting developer environments and CI/CD pipelines at risk.
“While traditional risks like manual dependency installation and insecure upgrade bots remain significant, the more pressing, forward-looking threat is at hyper-scale: coding agents with full autonomy and tool execution,” said Liran Tal, Head of Developer Relations & Community at Snyk in an email to eSecurityPlanet.
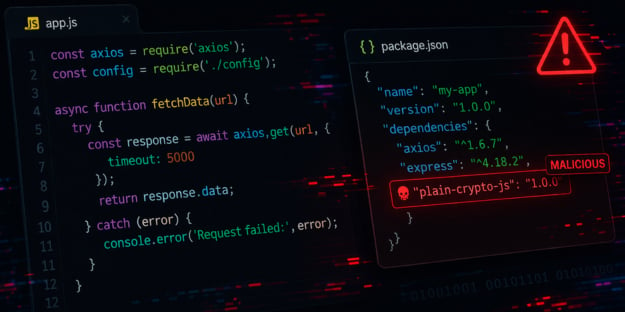
Inside the Axios Supply Chain Attack
Snyk researchers found the attack impacted Axios — used in over 100 million weekly downloads — meaning even a brief exposure created a significant blast radius across development pipelines and production environments.
Organizations relying on automated builds or unpinned dependencies were especially vulnerable, as malicious versions could be pulled without visibility, reinforcing how trusted open-source packages can be weaponized without altering core functionality.
How the Attack Worked
The root cause was a compromised maintainer account, highlighting a growing class of supply chain attacks that target identity rather than code.
By abusing npm’s trust model, the attacker was able to publish malicious versions directly to the official package, bypassing traditional safeguards.
Instead of modifying Axios itself, the attacker inserted a malicious dependency (plain-crypto-js) into the package, allowing the payload to execute during installation through a postinstall script with minimal user interaction.
Once triggered, the attack deployed a multi-stage payload using layered obfuscation techniques to evade detection.
The malware dynamically retrieved platform-specific RATs for macOS, Windows, and Linux systems, enabling broad cross-platform impact.
After execution, it removed traces of its installation, complicating forensic analysis and reducing the likelihood of detection in compromised environments.
The attack was actively exploitable during its brief publication window, and any system that installed the affected versions should be treated as fully compromised.
Given the RAT’s ability to execute commands, exfiltrate data, and establish persistence, this incident underscores how quickly a trusted dependency can become a high-impact attack vector when supply chain controls are weak or absent.
How to Mitigate Supply Chain Risk
Supply chain attacks are becoming more targeted and harder to detect, especially when they originate from trusted dependencies.
Traditional security controls often miss malicious behavior introduced during the build process or package installation.
To reduce risk, organizations need stronger controls across dependency management, build environments, and runtime monitoring.
- Audit lockfiles and enforce dependency pinning to prevent unauthorized or malicious package updates.
- Rotate credentials and secrets for potentially exposed systems to reduce post-compromise risk.
- Restrict postinstall scripts and implement dependency allowlisting using DevSecOps tools to limit execution of untrusted code.
- Verify package integrity using signing, provenance, or attestation to ensure trusted sources.
- Isolate build environments and restrict outbound network access to block malicious callbacks.
- Monitor for anomalous behavior using EDR or runtime controls to detect suspicious processes and connections.
- Test incident response plans for supply chain attack scenarios and use attack simulation tools.
Collectively, these measures help limit the blast radius of supply chain attacks while building resilience across development and deployment environments.
Shift in Supply Chain Threats
This incident reflects a shift in supply chain attacks, where attackers increasingly target maintainers and distribution channels instead of code-level flaws.
As open-source ecosystems grow, these approaches allow for more efficient, lower-noise compromises with broader downstream impact.
These trends highlight the need for a more structured approach to software supply chain security across development and deployment workflows.