
ShinyHunters has leaked data from the latest iteration of the BreachForums cybercrime marketplace, exposing hundreds of thousands of user records and prompting breach notifications from Have I Been Pwned (HIBP).
The incident once again highlights the ongoing instability and infighting within one of the cybercrime ecosystem’s most prominent hubs.
The breach affects “BreachForums Version 5,” a short-lived revival of the forum that emerged following multiple takedowns and law enforcement actions against earlier versions. According to a notice published by HIBP, the leak exposed approximately 339,800 unique email addresses, along with associated usernames and Argon2 password hashes. The breach itself occurred earlier in March 2026, with data quickly circulating in underground channels before becoming more widely accessible.
HIBP founder Troy Hunt added the dataset to the service shortly after its public disclosure and has begun notifying impacted individuals. As is standard practice, the platform is alerting users whose email addresses appear in the leaked database, enabling them to take remedial action, such as resetting passwords on other platforms and conducting account audits.
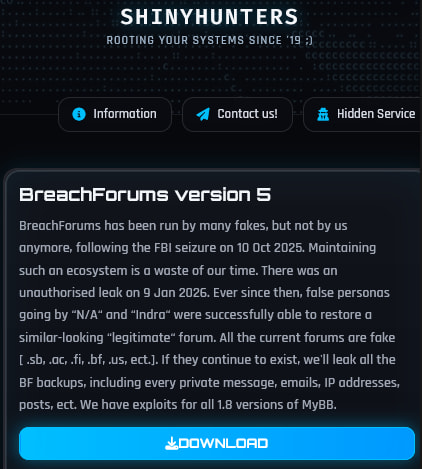
ShinyHunters, a well-known data extortion and hacking collective with a long history of high-profile breaches, claimed responsibility for the leak in a post on its dark web data leak and extortion portal. In that message, the group dismissed the legitimacy of the current forum operators, stating that BreachForums had effectively ceased to exist following an FBI seizure on October 10, 2025. The group further alleged that subsequent versions, including Version 5, were operated by impostors attempting to revive the brand.
The message also references an earlier unauthorized data leak on January 9, 2026, which reportedly enabled these actors to recreate a forum resembling the original platform. ShinyHunters warned that all current BreachForums instances are “fake” and threatened to release additional backend data, including private messages, IP addresses, and full database backups, if they continue to operate.
BreachForums has historically served as a central marketplace for cybercriminal activity, facilitating the sale and distribution of stolen databases, access credentials, and hacking tools. The platform rose to prominence following the 2022 shutdown of RaidForums and has since faced multiple disruptions, including the arrests of administrators and domain seizures. Despite repeated takedowns and arrests of high-profile users, the forum has reappeared under different operators and infrastructures, often with questionable legitimacy.
From a technical perspective, the inclusion of Argon2 password hashes provides some protection against immediate credential cracking, as the algorithm is designed to resist brute-force attacks. However, weak or reused passwords may still be recoverable, particularly if attackers dedicate sufficient computational resources.
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


