editorially independent. We may make money when you click on links
to our partners.
Learn More
This guide is for IT leaders, network administrators, and security teams evaluating next-generation firewalls (NGFWs), and it covers how they work, key features, and what to look for in 2026 solutions.
NGFWs have evolved beyond traditional firewalls to deliver deep packet inspection, application awareness, and integrated threat prevention, helping organizations defend against increasingly sophisticated attacks. As a foundational component of modern network security, NGFWs play a critical role in protecting business environments, especially as infrastructure expands across cloud, hybrid, and remote networks.
We surveyed the enterprise firewall market. In our analysis, nine NGFW vendors stand out:
Top NGFW Solutions Comparison
The following table helps you overview our top picks to find a next-gen firewall that aligns with your organization’s security objectives, considering a few features and starting prices.
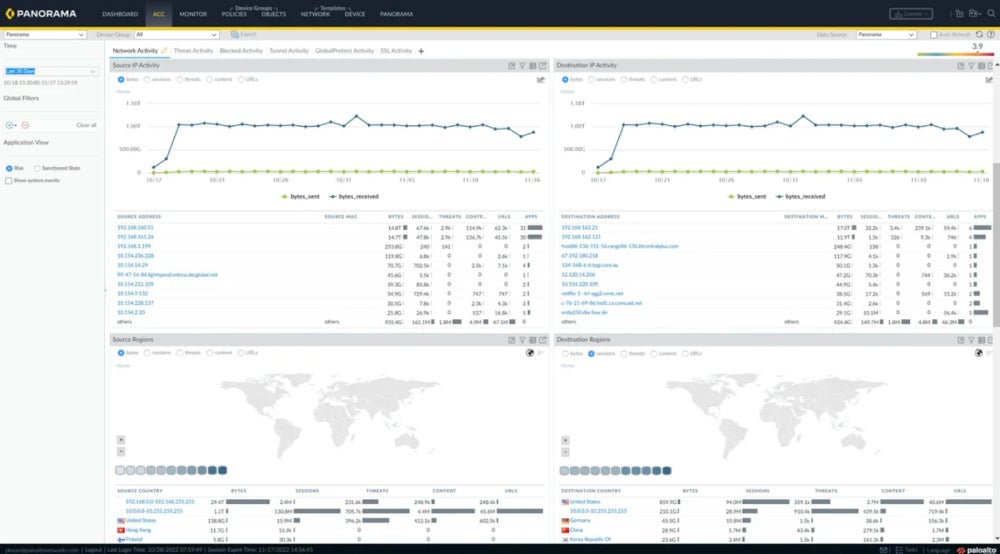
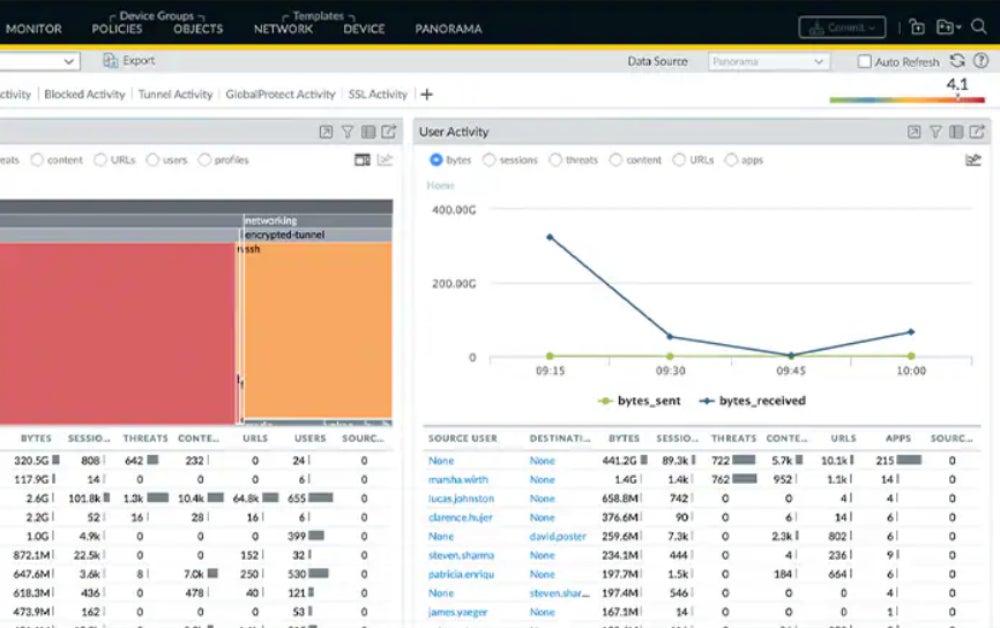
Palo Alto Networks remains a leading network security vendor in 2026, offering a full range of next-generation firewall solutions, including physical (PA-Series), virtual (VM-Series), and container-native (CN-Series) deployments. Its platform is designed to deliver consistent security and centralized visibility across complex, distributed environments — spanning on-premises infrastructure, multi-cloud, and containerized workloads.
Known for its depth of features and advanced threat prevention capabilities, Palo Alto’s firewall portfolio provides granular control, application-level visibility, and strong integration with its broader security ecosystem. While it comes at a premium price point, it’s best suited for mid-sized to large organizations with mature security teams that can fully leverage its extensive capabilities.
Pros
Cons
- User-based policies: User-based firewall policies limit application access by integrating existing user repositories.
- Machine learning for threat detection: These network firewalls use machine learning to locate security threats and prevent intrusions.
- Container security: Palo Alto also has a container firewall that integrates with Kubernetes environments and helps secure CI/CD procedures.
- Centralized management: Palo Alto firewalls use Panorama for central management, giving administrators a single point of contact to handle NGFWs.
Fortinet’s FortiGate next-generation firewalls continue to be a strong option in 2026, delivering high-performance protection for environments ranging from small offices to large enterprises. FortiGate integrates key security capabilities — such as SSL inspection, intrusion prevention, web filtering, and application control — into a single platform, enabling streamlined and efficient threat defense.
With its balance of performance, features, and cost-effectiveness, FortiGate is often positioned as a more accessible alternative to higher-priced competitors. It’s particularly well-suited for small to mid-sized organizations and distributed environments that need enterprise-grade security without the complexity or cost of larger platforms, including businesses in regulated industries like finance and healthcare.
Pros
Cons
- Security Processing Units (SPUs): SPUs and virtual SPUs (vSPUs) are used to speed up network security computing.
- FortiOS: Fortinet’s security-focused operating system offers federated firmware upgrades.
- Zero trust: FortiGate provides zero-trust capabilities for identifying and protecting suspicious users and devices.
- VPN tunneling: Scalable IPsec VPN tunneling helps your team secure a remote and distributed workforce.
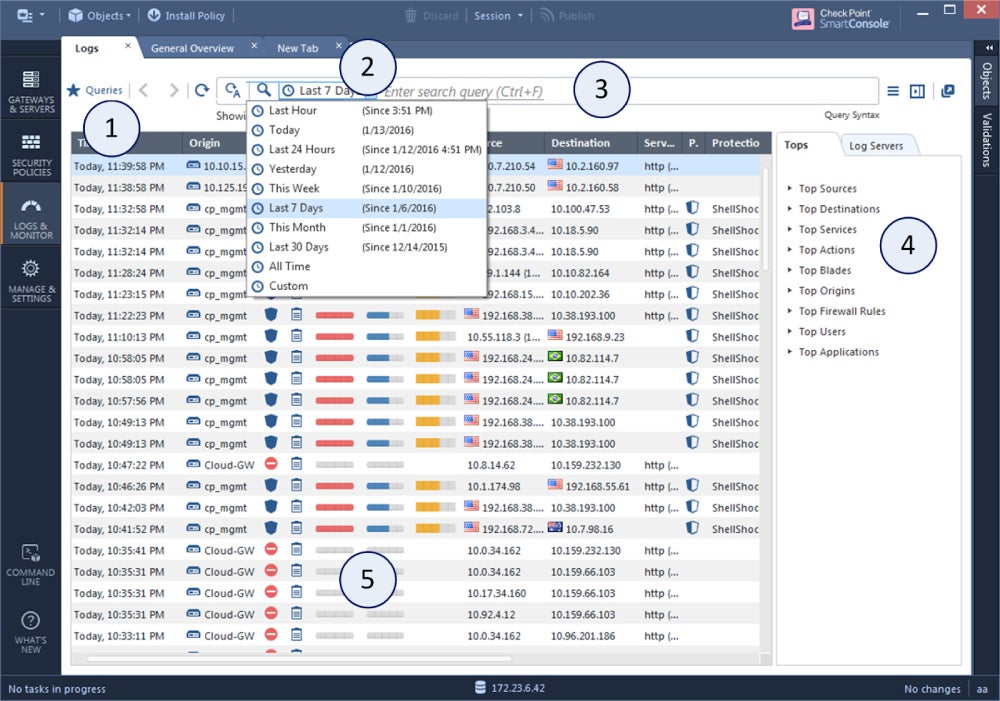
Check Point remains a well-established leader in network security, with its Quantum Security Gateways delivering advanced next-generation firewall capabilities for organizations of all sizes. The platform includes comprehensive threat prevention features such as intrusion prevention (IPS), anti-bot protection, application control, and URL filtering, helping defend against a wide range of modern threats.A standout capability is Check Point’s SandBlast Zero-Day Protection, which uses advanced sandboxing, threat emulation, and file extraction to identify and neutralize unknown threats before they reach users. With its strong emphasis on proactive threat prevention and high-throughput performance, Check Point is a compelling choice for organizations that require robust sandboxing and protection for high-traffic or high-risk environments.
Pros
Cons
- Compatibility with hybrid infrastructure: Check Point supports physical, virtual, cloud, and mobile segments.
- SandBlast zero-day protection: This product is notable for its extensive sandboxing features.
- Centralized management: Check Point provides policy configuration rollout and rollback options for security and IT managers.
- Maestro Orchestrator: Maestro is a network security solution for hyperscale firewall installations.
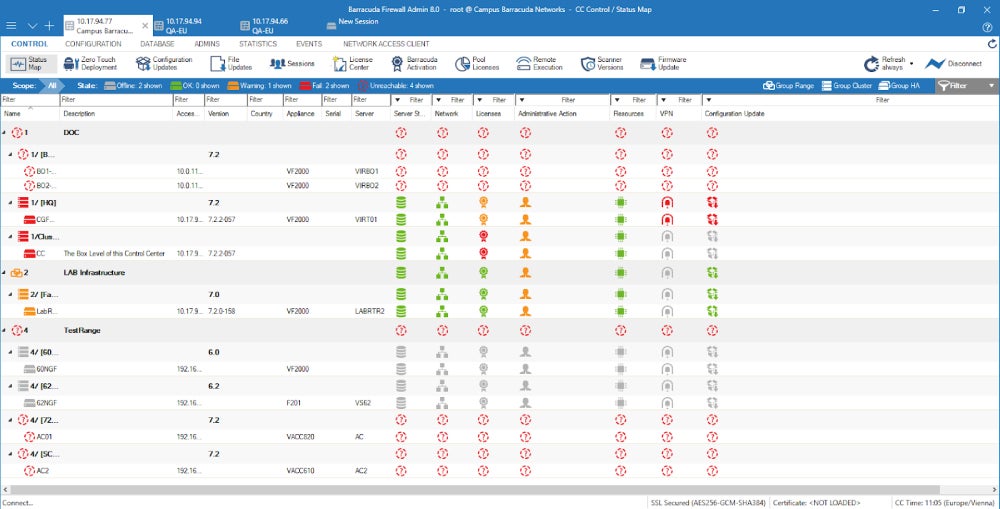
Barracuda CloudGen Firewall is built for modern hybrid and distributed environments, combining next-generation firewall capabilities with integrated SD-WAN, intrusion detection and prevention (IDPS), and secure VPN connectivity. Its F-Series appliances are designed to support both legacy infrastructure and evolving cloud architectures, making it easier for organizations to transition without disrupting existing systems.
Barracuda emphasizes layered threat detection, using a combination of signature-based analysis, behavioral techniques, and advanced inspection to address increasingly evasive threats. It’s a strong option for organizations operating across hybrid and multi-cloud environments, particularly those that need visibility and control over traffic moving between locations, users, and cloud platforms.
Pros
Cons
- Advanced threat protection: Barracuda provides advanced threat protection through traffic management, SD-WAN, IDPS, and VPN.
- Stateful deep packet inspection: Stateful deep packet inspection prevents malformed packets and attacks.
- High availability: The Cloud Gen Firewall offers high availability through automatic load balancing and uplink options.
- Control over objects and configuration: Barracuda allows admins to manage objects, repositories, updates, privileges, and configuration.
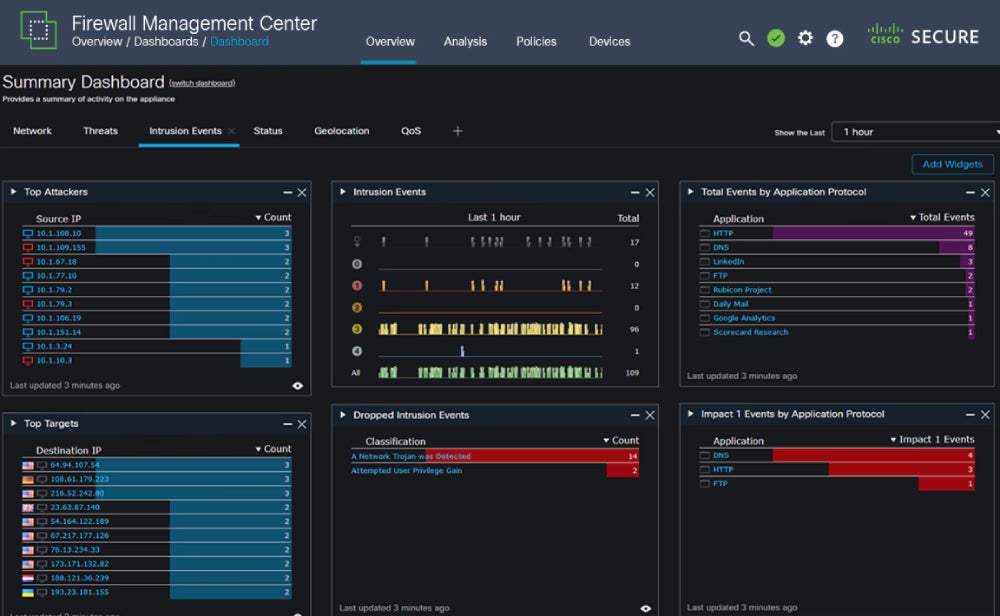
Cisco Secure Firewall delivers real-time threat protection across on-premises, cloud, and hybrid environments, making it well-suited for dynamic, distributed infrastructures in 2026. With integrations like Cisco Secure Workload, organizations can extend consistent security policies as they migrate applications to cloud or multicloud environments.
The platform combines advanced threat detection, application visibility, and centralized policy management to support complex enterprise use cases. Designed for scalability and granular control, Cisco Secure Firewall is a strong fit for large organizations that need to enforce security policies across diverse applications and highly segmented networks.
Pros
Cons
- Dynamic policy support: Cisco Secure Firewall supports tag-based policies and attributes.
- Cloud Native firewall: This Secure Firewall option, orchestrated by Kubernetes, is developer-friendly, extremely elastic, and cloud-native.
- Log management: Secure Firewall offers log management, security incidents, and behavioral analysis.
- Threat intelligence: The Cisco Talos Intelligence Group provides security teams with rapid and actionable threat intelligence.
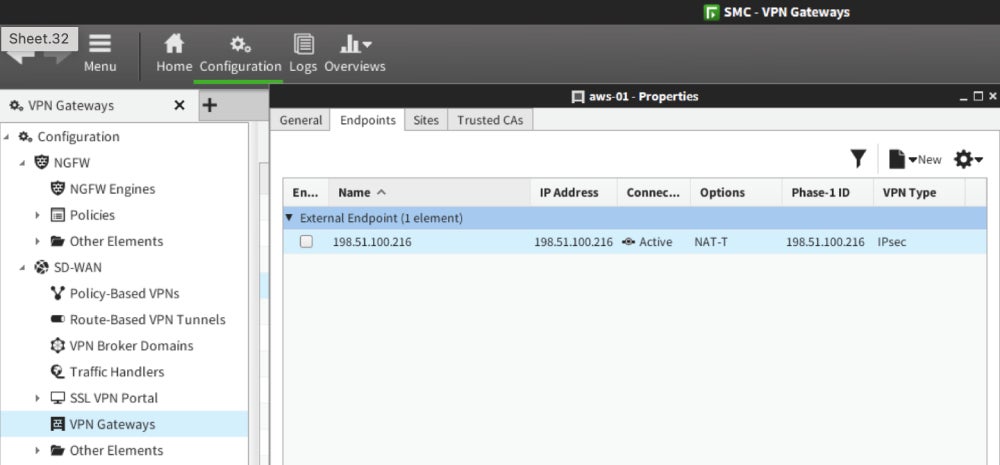
Forcepoint’s next-generation firewall (NGFW) delivers scalable, high-availability network security by combining advanced threat protection with integrated SD-WAN capabilities. Built for distributed and performance-sensitive environments, it enables organizations to manage traffic, enforce policies, and maintain uptime across complex networks.
A key strength of Forcepoint’s platform is its centralized cluster management, which simplifies administration and supports large-scale deployments. In 2026, it remains a strong choice for enterprises that need robust security and network performance without the premium cost of some top-tier competitors, making it a practical option for organizations seeking a balance between functionality and affordability.
Pros
Cons
- High-availability clustering: Forcepoint’s NGFW has high-availability clustering for device, VPN connection, and SD-WAN networks.
- Internal integrations: The NGFW integrates with Forcepoint’s CASB, online security, and anti-malware sandboxing solutions.
- Application-level traffic protection: Forcepoint’s app-focused security helps secure traffic to enterprise applications.
- Smooth policy upgrades: Forcepoint pushes policy updates and software upgrades to its firewall clusters while working to prevent downtime.
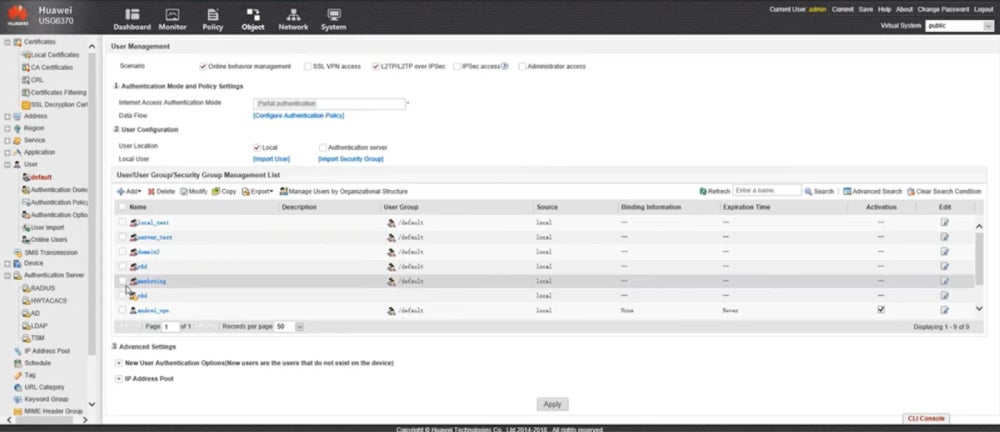
Huawei’s Unified Security Gateway (USG) series is designed for large enterprises, data centers, and service providers that require high-performance, scalable network security. Its AI-powered firewall models, such as the USG6700E series, help streamline policy management and accelerate threat detection with intelligent automation. For more demanding environments, the USG9500 series delivers terabit-level performance, making it suitable for large-scale data centers and cloud infrastructure.
Huawei’s NGFW portfolio continues to focus on high throughput, centralized management, and AI-driven security capabilities, making it a strong fit for organizations that need consistent, high-capacity protection across complex and high-traffic environments.
Pros
Cons
- Integration with cloud and local sandboxes: Huawei works with a local or cloud sandbox to detect, analyze, and prevent zero-day attacks.
- Policy-based routing: Through routing policies, Huawei manages bandwidth per user and IP address.
- Deception system: The firewalls include deception technology to help teams detect threat actor scans with lowered risk.
- Chip-level pattern matching: This technique improves antivirus and IPSec performance.
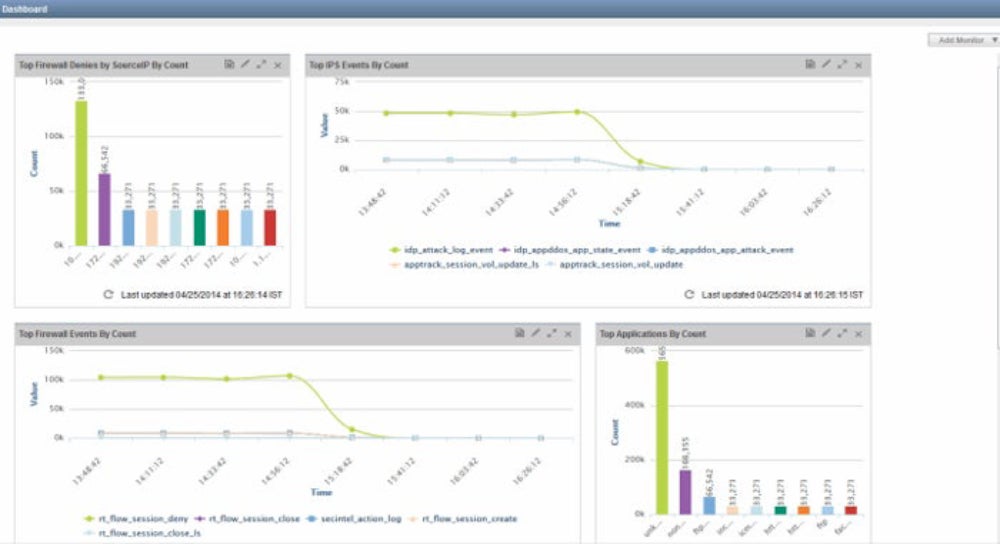
Juniper Networks delivers next-generation firewall capabilities through its SRX Series, powered by the Junos operating system. These gateways provide centralized policy management and consistent security across network edges, data centers, virtual machines (vSRX), and containerized environments (cSRX). Designed for flexibility, Juniper’s platform supports modern architectures while maintaining strong performance and reliability.Juniper continues to emphasize automation, scalability, and integrated networking features like SD-WAN, making it a solid choice for organizations adopting hybrid, cloud-native, or containerized environments. It’s particularly well-suited for mid-sized enterprises and teams that want to combine networking and security within a unified platform.
Pros
Cons
- AppSecure: Juniper uses AppSecure to identify, secure, and manage application and user traffic.
- Intrusion prevention: Juniper’s intrusion prevention system allows you to inspect SSL traffic and create your own IDP policies.
- SDN and policy-based routing: SRX performs SDN and policy-based routing across wired, wireless, and wide-area networks.
- Microsegmentation: Juniper’s NGFW services include network segmentation for improved protection.
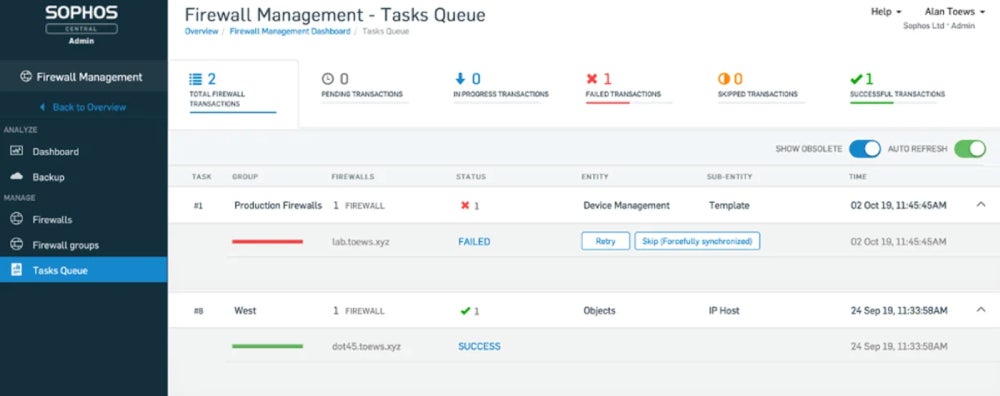
Sophos’ XGS Series next-generation firewalls are designed for modern, distributed networks, delivering strong protection for SaaS applications, SD-WAN traffic, and cloud environments. Powered by threat intelligence from SophosLabs, these firewalls use real-time global data and AI-driven analysis to automatically detect and respond to emerging threats.
The XGS platform stands out for its balance of advanced capabilities and ease of use. With an intuitive management interface and streamlined policy controls, it’s well-suited for small to mid-sized teams or organizations with limited security expertise that still need comprehensive, enterprise-grade protection.
Pros
Cons
- Deep packet inspection: The XGS Series offers DPI, intrusion prevention, and proxy-based scanning.
- Threat-intelligent traffic selection: Sophos supports modern cipher suites and covers all ports.
- Deep learning and dynamic sandboxing: Sophos has a sandboxing option and deep learning for analyzing static files.
- Machine learning for threat identification: The XGS series uses machine learning models to identify advanced and unknown threats.
Key Features of NGFW Solutions
When evaluating next-generation firewall (NGFW) solutions in 2026, focus on capabilities that go beyond basic traffic filtering. Modern NGFWs combine identity awareness, deep inspection, centralized management, and integrated threat prevention to protect increasingly complex, hybrid environments.
Application and Identity Awareness
A defining feature of NGFWs is their ability to identify applications and users — not just ports and protocols. This allows administrators to create granular policies based on user identity, device type, and application behavior, improving control and reducing risk across distributed environments.
Centralized Management and Visibility
Modern NGFW platforms provide unified dashboards for managing policies, monitoring traffic, and analyzing threats across on-premises, cloud, and remote networks. In 2026, many solutions also include AI-driven insights to help teams prioritize alerts, identify anomalies, and streamline security operations.
Stateful Inspection Across Layers
Traditional firewalls focus on lower-layer traffic (e.g., IP and port data), whereas NGFWs extend inspection up through the application layer, enabling more detailed analysis of user activity and application behavior. This enables deeper visibility into traffic flows and more accurate differentiation between legitimate and malicious activity, especially as applications move beyond traditional network boundaries.
Deep Packet Inspection (DPI)
Deep packet inspection allows NGFWs to analyze both packet headers and payloads at the application layer. This enables detection of hidden threats, malicious code, and suspicious behavior that basic inspection methods might miss, making it essential for defending against modern attack techniques.
Integrated Intrusion Prevention (IPS)
Most NGFWs now include built-in intrusion prevention systems that can detect and block exploits, malware, and known vulnerabilities in real time. In 2026, IPS capabilities are often enhanced with machine learning and behavioral analysis, helping prevent attacks such as ransomware, brute-force attempts, and zero-day exploits without requiring separate tools.
Frequently Asked Questions (FAQs)
What Firewall Is Deployed the Most?
Determining the most deployed firewall varies based on organizational needs. However, large organizations widely use firewall giants such as Palo Alto Networks, Fortinet, and Cisco. Your unique requirements, preferences, and the company’s size determine which firewalls would be a good fit.
How Many Firewalls Should You Have?
There’s no one-size-fits-all answer. Most organizations use a layered approach, deploying firewalls at the network perimeter, between internal segments, and across cloud environments. This defense-in-depth strategy helps limit lateral movement and strengthen overall security.
Read more about the best practices to implement when deploying and using firewalls.
Which Is Better: UTM or NGFW?
Unified threat management (UTM) solutions bundle multiple security features into a single platform and are often sufficient for small businesses. NGFWs, however, provide more advanced capabilities, scalability, and granular control, making them better suited for mid-sized to large organizations or complex environments.
Bottom Line: Secure Your Network with Next-Generation Firewall Solutions in 2026
Selecting the right NGFW requires aligning your security needs with your organization’s size, infrastructure, and in-house expertise. Modern NGFWs offer powerful protection, but they also require proper configuration, ongoing management, and skilled personnel to be fully effective.
By prioritizing key features, evaluating scalability, and ensuring compatibility with your existing security stack, you can build a strong foundation for protecting your network against today’s evolving threats.
Looking for another comprehensive network security solution? Read our list of best unified threat management tools next.