editorially independent. We may make money when you click on links
to our partners.
Learn More
A zero-day vulnerability in Cisco Catalyst SD-WAN products has been actively exploited since at least 2023, allowing attackers to bypass authentication and ultimately gain root access in targeted environments.
This flaw affects core control-plane components and has been linked to a sophisticated threat actor cluster known as UAT-8616.
“The Cisco Catalyst SD-WAN zero-day, which is a perfect CVSS 10, allowing unauthenticated remote attackers to bypass authentication and gain administrative privileges, is serious on its own. But the way UAT-8616 exploited it is the bigger story,” said Yagub Rahimov, CEO of Polygraf AI in an email to eSecurityPlanet.
He explained, “After gaining initial access through the authentication bypass, the attacker deliberately downgraded the software to re-expose CVE-2022-20775 – a 2022 path traversal flaw that, in isolation, required authenticated access and carried moderate risk.”
Yagub added, “Chaining it with an authentication bypass makes it into something different: a path to persistent root access across the entire SD-WAN fabric. That transformation is the sophisticated part.”
Inside the Cisco SD-WAN Zero-Day
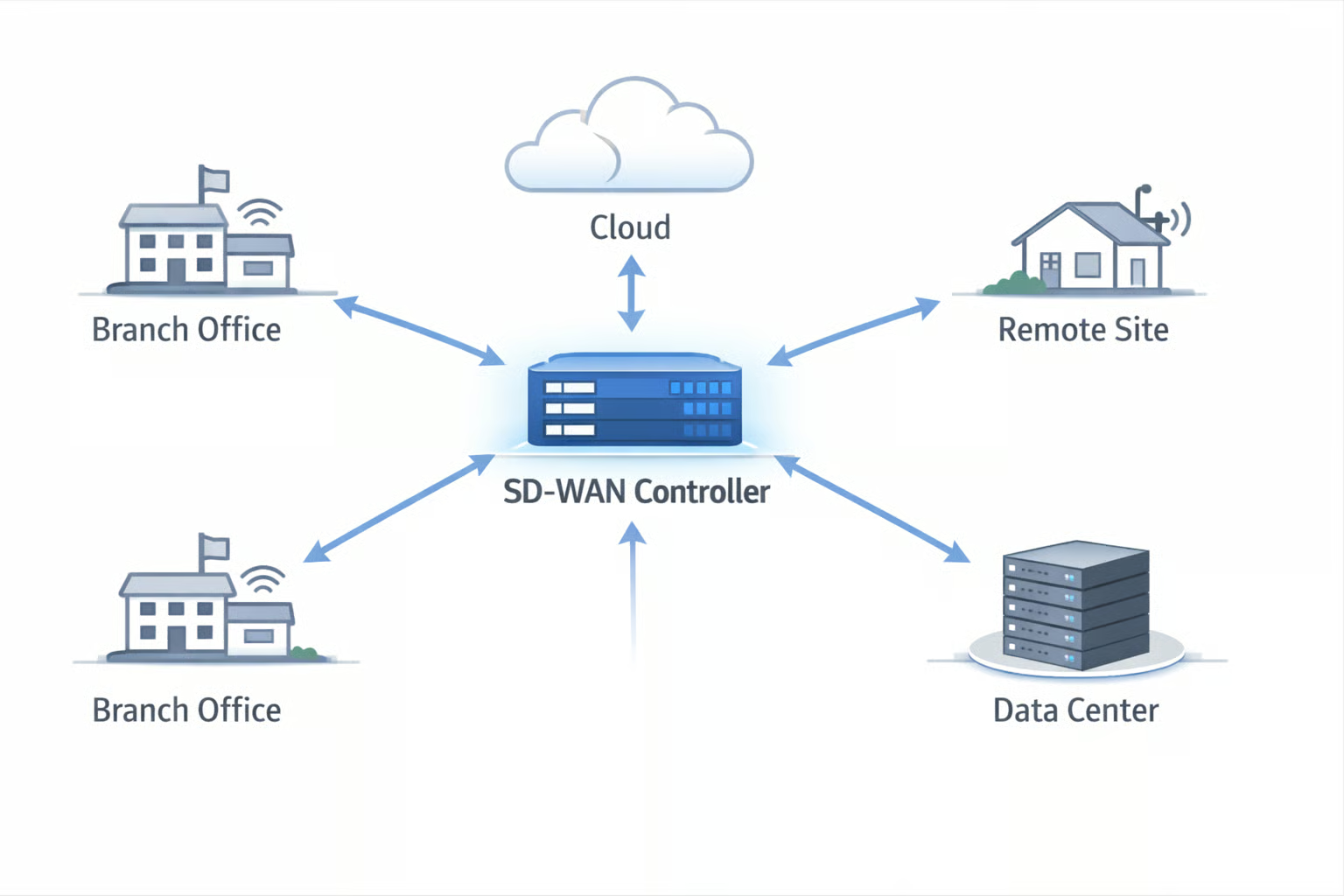
Cisco Catalyst SD-WAN is deployed in enterprise environments to manage distributed networks, branch connectivity, and cloud routing.
Because these platforms operate at the network control plane, a successful authentication bypass can have far-reaching consequences.
Administrative access to an SD-WAN controller allows an attacker to manipulate routing policies, introduce rogue peers, alter traffic flows, and potentially maintain persistent visibility across the organization’s network fabric.
How CVE-2026-20127 Enables Authentication Bypass
CVE-2026-20127 affects both the Cisco Catalyst SD-WAN Controller (formerly vSmart) and SD-WAN Manager (formerly vManage).
The vulnerability carries a CVSS score of 10.0, reflecting its network-based attack vector, low complexity, lack of required privileges, and absence of user interaction.
In practical terms, this means an unauthenticated attacker can target exposed control planes remotely without relying on stolen credentials or successful phishing attacks.
The flaw stems from weaknesses in the SD-WAN peering authentication mechanism. By sending a crafted request, an attacker can bypass authentication checks and gain access as a high-privileged internal, non-root user.
From there, the attacker can leverage NETCONF functionality to push configuration changes across the SD-WAN fabric, including modifying routing behavior or establishing unauthorized peer connections.
Exploitation Chain and Indicators of Compromise
Cisco Talos has attributed the exploitation activity to a threat cluster it tracks as UAT-8616, which it assesses with high confidence to be a highly sophisticated threat actor.
Following initial access via CVE-2026-20127, investigators found evidence that the actor downgraded software versions to exploit CVE-2022-20775, a path traversal vulnerability, in order to escalate privileges to root.
After obtaining root access, the attackers reportedly reverted the system to its original software version, likely to minimize suspicion and make forensic detection more difficult.
Cisco indicated that exploitation activity associated with this campaign dates back to at least 2023.
Security teams should review logs and configurations for indicators of compromise, including unauthorized control-connection peering events, the addition of rogue peers, unexpected software downgrades followed by reboots, root-level SSH sessions or modified authorized_keys files, and evidence of log clearing or truncation (e.g., missing or altered bash_history or syslog entries).
Because CVE-2026-20127 is remotely exploitable without authentication, internet-exposed SD-WAN management and control planes face elevated risk if not patched and closely monitored.
Hardening Edge Infrastructure Security
Organizations should take a layered approach that reduces exposure of management planes, strengthens access controls, and improves visibility into control-plane activity.
- Patch to the latest version and verify patch levels across both on-premises and cloud-hosted deployments.
- Inventory and reduce exposure of SD-WAN management and control planes by removing unnecessary internet access, implementing segmentation, and enforcing IP allowlisting or zero trust access controls.
- Strengthen identity and privilege management by enforcing MFA for administrative access, disabling unused accounts, restricting NETCONF and API permissions, and applying least-privilege role separation.
- Continuously monitor control-plane activity by auditing peering events, reviewing NETCONF sessions and configuration changes, and alerting on unexpected version downgrades, reboots, or rogue peer additions.
- Conduct proactive threat hunting and integrity checks by reviewing historical logs, validating SSH keys and root access settings, inspecting for log tampering, and confirming device configurations match known-good baselines.
- Enhance telemetry and detection by integrating SD-WAN logs into SIEM platforms, correlating authentication and routing events, and monitoring for anomalous control-connection or policy changes.
- Regularly test incident response plans and conduct tabletop exercises focused on SD-WAN compromise scenarios.
Collectively, these measures help reduce the risk of compromise while strengthening long-term resilience across SD-WAN and network edge environments.
SD-WAN Control Planes Are Targets
The exploitation of this vulnerability highlights the need to layer controls for network control-plane infrastructure.
Chaining authentication bypass, privilege escalation, and software version manipulation demonstrates how attackers can leverage edge devices to maintain persistent access when security controls may be insufficiently enforced.
These risks are driving organizations to leverage zero trust solutions that reduce implicit trust and enforce continuous verification across network infrastructure and management planes.