
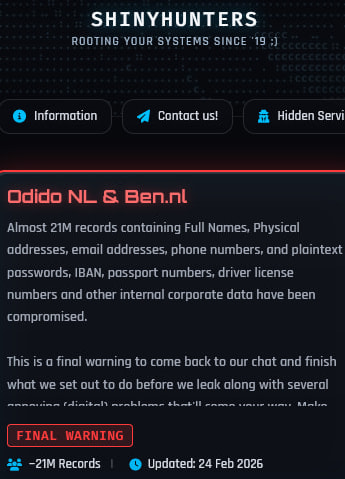
The ShinyHunters hacking group has threatened to publish what it claims are 21 million customer records stolen from Dutch telecom provider Odido.
The threat was posted on the group’s dark web extortion portal, where the attackers warned Odido to resume negotiations or face a public data dump.
In a listing published on February 24, 2026, ShinyHunters claims the dataset contains full names, physical addresses, email addresses, phone numbers, IBAN bank account numbers, passport numbers, driver’s license numbers, and additional internal corporate data.
ShinyHunters is a well-known data extortion group that has previously targeted major technology firms and online services, often leveraging stolen customer databases to pressure victims into paying ransoms.
Odido, one of the largest telecommunications providers in the Netherlands, serves millions of mobile, broadband, and television customers nationwide.
Earlier this month, Odido confirmed that attackers had gained unauthorized access to its customer contact system during the weekend of February 7–8, 2026. The company said 6.2 million customers were affected and that exposed data included names, addresses, phone numbers, email addresses, bank account details, and identification numbers. According to Odido, core telecom infrastructure was not impacted, and services such as mobile calling, internet access, and television remained operational throughout the incident.
At the time, Odido stated there was no evidence that the stolen data had been published online. The ShinyHunters claim now raises questions about the true scope of the breach and whether the attackers exfiltrated a larger dataset than initially disclosed.
In an update to its FAQ page published yesterday, Odido acknowledged that different categories of customer data may have been exposed, and that affected individuals received one of four notification variants depending on the type of information involved. These range from name and address details only, to combinations including bank details and ID document data. The company emphasized that Mijn Odido account passwords, subscription details, call records, billing information, location data, and scans of identity documents were not part of the breach.
Odido also addressed confusion surrounding a leaked database field labeled “password_c.” Despite its name, the company clarified that this field contained a telephone verification “challenge word” used by a limited group of customers during support calls, not login credentials. The practice has since been discontinued.
The telecom provider further stated that national insurance numbers are not stored in its systems and were therefore not exposed. In cases where bank account numbers were compromised, Odido, citing guidance from the Dutch Banking Association (NVB), advised that changing IBANs is not necessary, as account numbers alone cannot be used to access online banking environments.
For customers who have not received a notification email or SMS, Odido says they can assume they were not affected, though it recommends checking spam folders as a precaution.
Odido customers are advised to remain vigilant for phishing emails, SMS messages, and phone calls impersonating Odido or financial institutions. Users should avoid clicking unsolicited links, verify the authenticity of communications through official channels, and consider enabling transaction alerts with their banks. Any suspicious activity should be reported immediately to the relevant financial institution and to the Dutch Central Helpdesk for Identity Fraud (CMI).
If you liked this article, be sure to follow us on X/Twitter and also LinkedIn for more exclusive content.


